token-priv: Abusing Token Privileges For EoP
token-priv
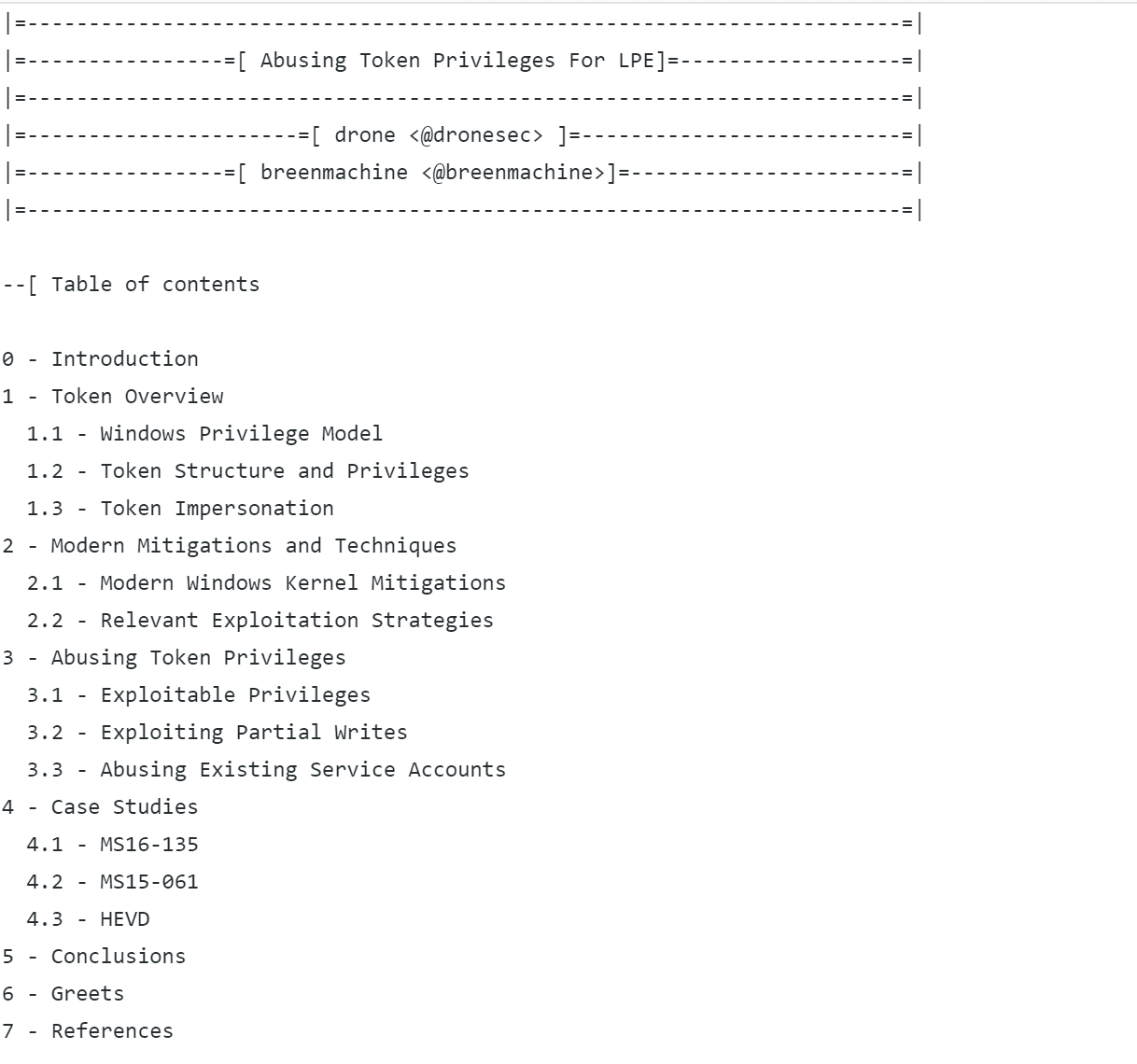
Abusing Token Privileges For EoP
contains all code and a Phrack-style paper on research into abusing token privileges for escalation of privilege.
This repository is organized into three parts:
- lib/, which contains auxiliary scripts (for now just the pykd token script)
- poptoke/, which is the main bulk of the code. It’s organized as a project, but should be noted, and stressed, that it’s NOT going to compile and give you shells as is. It’s an amalgam of proof of concepts and portable functions for use in your own bugs and edification and meant only as a reference guide. Don’t submit issues for “fixing” it, please.
- abusing_token_eop_1.0.txt, complimentary paper on the topic and our findings.
Windows kernel exploitation has grown increasingly complex over the last several years, particularly with the release of Windows 10 and its successive core updates. Techniques have been born and died over the course of months, new ones quickly replacing them. Techniques themselves have grown hyper-specific or brittle, fitting only a particular pattern or space.
Exploitation has often relied on obtaining some form of arbitrary code execution. Obtaining a read/write primitive, stacking strategies to evade mitigations, and eventually obtaining the execution of a privileged action. Recently we’ve seen a trend towards logic basic actions, such as token stealing, enabling god mode bits, or NULLing out token security descriptors [0]. These actions delegate the theft of privileges to userland, freeing the exploit dev from the confines of kernel hell.
The token stealing shellcode popularized by many exploit developers and malware authors over the years is not one of chance. It’s been an extremely reliable technique offering stable, simple shellcode and, until recently, acceptable behavior. Microsoft has implemented detection heuristics within its Advanced Threat Protection platform [2], but as of yet not implemented anything within the Windows kernel itself. For malware writers and skiddies, this might be tolerable, but for advanced adversaries or red teamers, it is not.
Download
git clone https://github.com/hatRiot/token-priv.git
Copyright (c) 2017 Bryan Alexander
Source: https://github.com/hatRiot/






