tor-router v4.0.13 releases: A SOCKS, HTTP and DNS proxy for distributing traffic across multiple instances of Tor
Tor Router
Tor Router is a SOCKS5, DNS and HTTP proxy server for distributing traffic across multiple instances of Tor. At startup, Tor Router will run an arbitrary number of instances Tor and each request will be sent to a different instance in a round-robin fashion. This can be used to increase anonymity because each request will be sent on a different circuit and will most likely use a different exit-node, and also to increase performance since outbound traffic is now split across several instances of Tor.
Changelog v4.0.13
-
Added a mechanism to handle dynamically allocating numerous ports.
- Updates granax package reference.
Install
git clone https://github.com/znetstar/tor-router.git
cd
npm installTo install globally run:
npm install -g tor-router
Alternatively, docker can be used. The build will retrieve the latest version of Tor from the official Tor Project repository.
To build run:
docker build -t znetstar/tor-router .
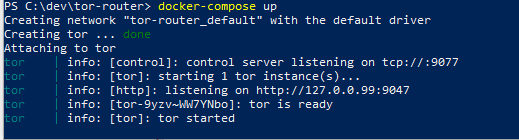
To start run:
docker run --rm -it -p 9050:9050 znetstar/tor-router
 Usage
Usage
| Command line switch | Environment Variable | Description |
|---|---|---|
| -f, –config | Path to a JSON configuration file to use | |
| -c, –controlHost | CONTROL_HOST | Host the control server will bind to and listen for TCP traffic (see below) |
| -w, –websocketControlHost | WEBSOCKET_CONTROL_HOST | Host the control server will bind to and listen for WebSocket traffic |
| -j, –instances | INSTANCES | Number of Tor instances to spawn |
| -s, –socksHost | SOCKS_HOST | Host the SOCKS proxy will bind to |
| -d, –dnsHost | DNS_HOST | Host the DNS proxy will bind to |
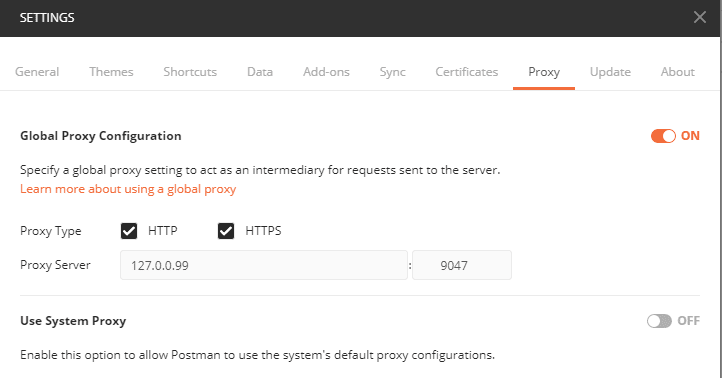
| -h, –httpHost | HTTP_HOST | Host the HTTP proxy will bind to |
| -l, –logLevel | LOG_LEVEL | Log level (defaults to “info”) set to “null” to disable logging. To see a log of all network traffic set logLevel to “verbose” |
| -p, –parentDataDirectory | PARENT_DATA_DIRECTORY | Parent directory that will contain the data directories for the instances |
| -b, –loadBalanceMethod | LOAD_BALANCE_METHOD | Method that will be used to sort the instances between each request. Currently supports “round_robin” and “weighted”. |
| -t, –torPath | TOR_PATH | Provide the path for the Tor executable that will be used |
| -n, –proxyByName | PROXY_BY_NAME | Controls how authenticated requests will be handled. Can be set to “individual”, “group” or false to disable |
Copyright 2018 Zachary Boyd
Source: https://github.com/znetstar/





