volatility-bitlocker: Volatility plugin to extract BitLocker Full Volume Encryption Keys
volatility-bitlocker
A plugin for the Volatility Framework which aims to extract BitLocker Full Volume Encryption Keys (FVEK) from memory. Works on Windows 7 through to Windows 10.
This is very much a work-in-progress and support for Windows 8 – 10 is highly experimental.
Finds the FVEK on Windows 7 by searching for the FVEc pool tag.
Attempts to locate the FVEK on Windows 8, 8.1 and 10 by analyzing memory after finding the Cngb pool tag.
The plugin isn’t entirely reliable for Windows 8 – 10 but works in most cases with a few quirks:
- Returns AES Keys other than the FVEK (See above, these keys only exist on Bitlocker protected systems).
- Doesn’t always work with Windows 10 XTS-AES encryption (Though works with CBC).
- Cannot identify the BitLocker mode of operation above Windows 7.
The plugin operates as follows:
- Obtains Windows version from profile metadata.
- If the version is lower than Windows 8: – Searches for FVEc pool tag
- Identifies BitLocker mode
- Extracts FVEK of appropriate length and TWEAK key if applicable
- If the version is higher than Windows 8: – Searches for Cngb pool tag with a pool size of 672
- Attempts to identify key length (Does not work properly for XTS-AES in Win10)
- Extracts either 128-bit or 256-bit key
- Is unable to guarantee it is a BitLocker FVEK.
- Prints the results.
Download
git clone https://github.com/tribalchicken/volatility-bitlocker.git
Usage
bitlocker.py is a plugin for the Volatility Framework. You can either place the plugin in the plugins directory at volatility/plugins, or alternatively, you can place the plugin in a separate directory and point volatility to it with --plugins
For example, using a directory called “Plugins”:
voldev$ ls plugins
bitlocker.py
voldev$ volatility –plugins=plugins/ –profile=Win81U1x64 -f WIN81X64-20160916-061911.raw bitlocker
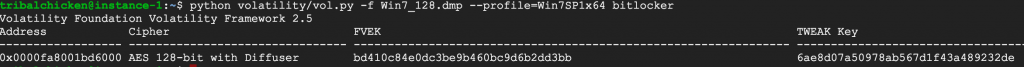
Example of a Windows 7 image:
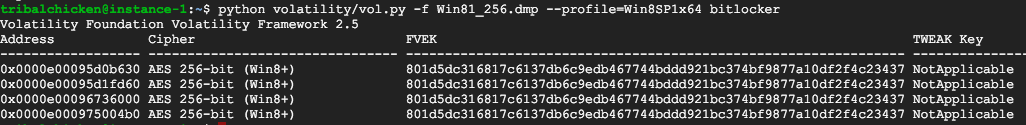
Example of a Windows 8.1 Image:
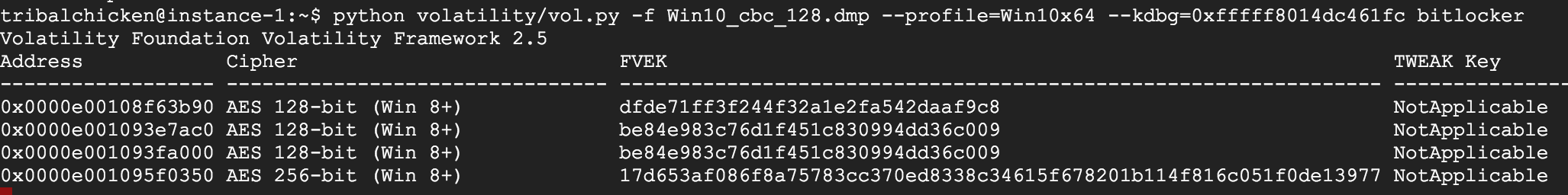
Example of a Windows 10 image (CBC):
And this is a screenshot of mounting the above Windows 8.1 protected volume using the FVEK data:
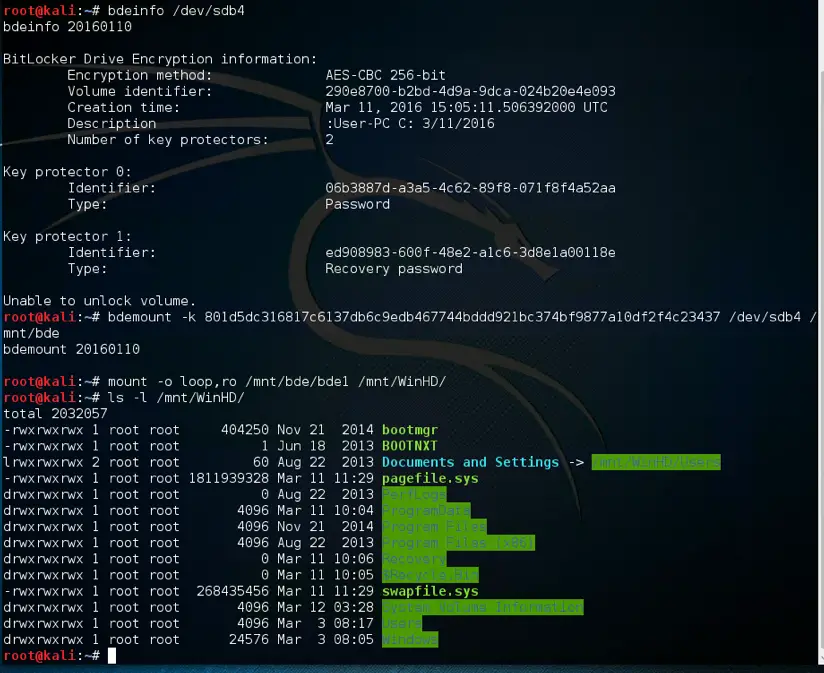
The excellent libbde library can be used to mount BitLocker protected volumes in Linux using the FVEK and TWEAK data.
Common Problems
Volatility tells you it needs something to do
Volatility doesn’t know about the plugin. Check the location of the plugin, and run volatility --info to determine if it is detected
The plugin doesn’t find anything
There could be many causes.
- The drive is not bitlocker encrypted
- The memory image does not contain the key (Image captured after key is evicted from memory, overwritten during acquisition, etc)
- The key exists but the plugin doesn’t find it.
Source: