vopono: run applications through VPN tunnels
vopono
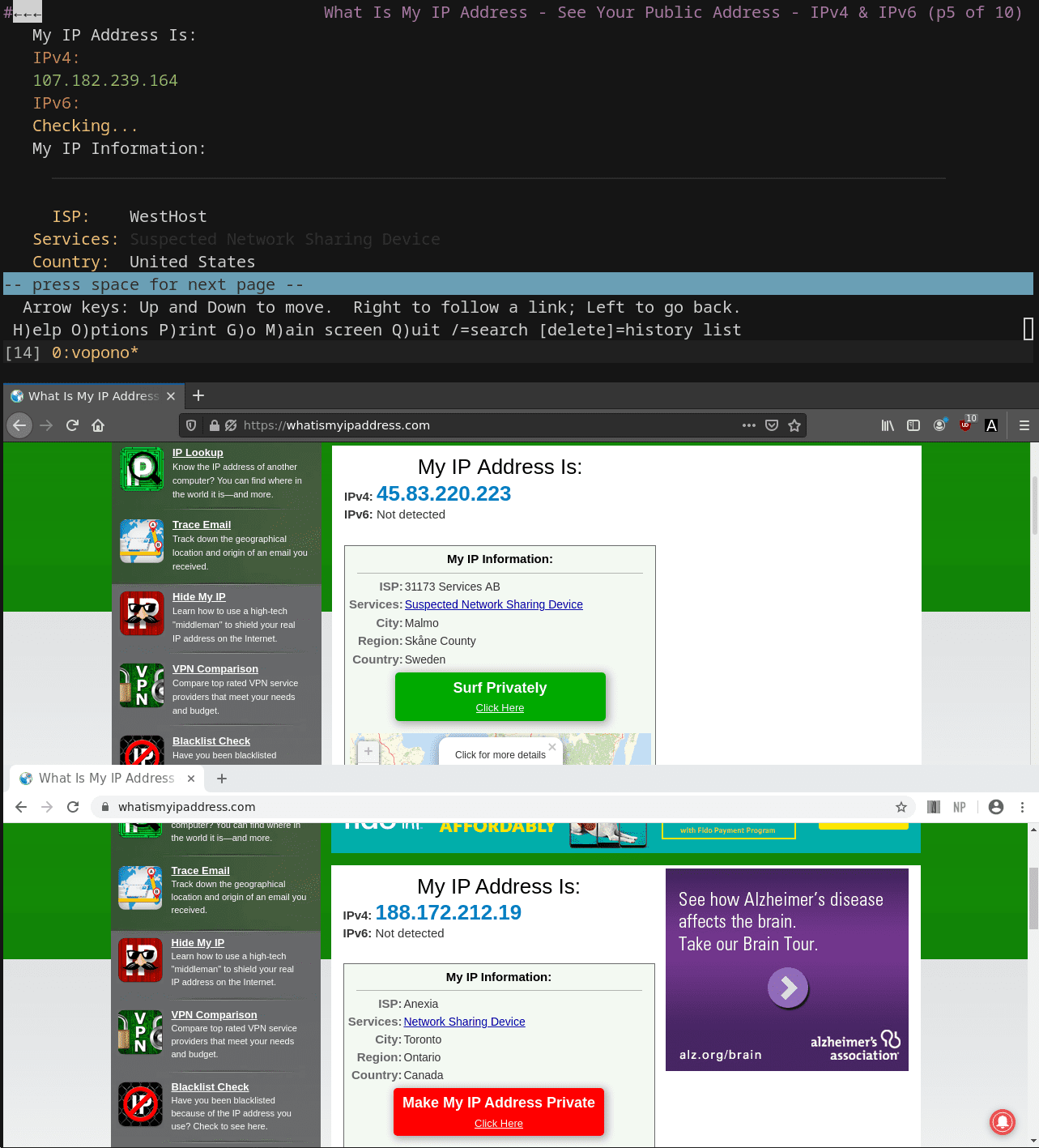
vopono is a tool to run applications through VPN tunnels via temporary network namespaces. This allows you to run only a handful of applications through different VPNs simultaneously, whilst keeping your main connection as normal.
vopono includes built-in killswitches for both Wireguard and OpenVPN.
Currently, Mullvad, AzireVPN, MozillaVPN, TigerVPN, ProtonVPN, iVPN, NordVPN, HMA (HideMyAss), and PrivateInternetAccess are supported directly, with custom configuration files also supported with the –custom argument.
For custom connections, the OpenConnect and OpenFortiVPN protocols are also supported (e.g. for enterprise VPNs).
Supported Providers
| Provider | OpenVPN support | Wireguard support |
|---|---|---|
| Mullvad | ✅ | ✅ |
| AzireVPN | ✅ | ✅ |
| iVPN | ✅ | ✅ |
| PrivateInternetAccess | ✅ | ❌ |
| TigerVPN | ✅ | ❌ |
| ProtonVPN | ✅ | ❌ |
| MozillaVPN | ❌ | ✅ |
| NordVPN | ✅ | ❌ |
| HMA (HideMyAss) | ✅ | ❌ |
Usage
Set up VPN provider configuration files:
$ vopono sync
Note when creating and uploading new Wireguard keypairs there may be a slight delay until they are usable (about 30-60 seconds on Mullvad for example).
Run Firefox through an AzireVPN Wireguard connection to a server in Norway:
$ vopono exec --provider azirevpn --server norway firefox
You should run vopono as your own user (not using sudo) as it will handle privilege escalation where necessary. For more details around running as a systemd service, etc. see the User Guide.
vopono can handle up to 255 separate network namespaces (i.e. different VPN server connections – if your VPN provider allows it). Commands launched with the same server prefix and VPN provider will share the same network namespace.
Default configuration options can be saved in the ~/.config/vopono/config.toml file, for example:
firewall = "NfTables"
provider = "Mullvad"
protocol = "Wireguard"
server = "usa-us22"
Note that the values are case-sensitive.
See the vopono User Guide for much more detailed usage instructions (including handling daemons and servers).
Install
Copyright (C) 2021 jamesmcm






