vscan: vulnerability scanner tool using nmap and nse scripts
Introduction
nmap (“Network Mapper”) is an open source tool for network exploration and security auditing. It was designed to rapidly scan large networks, although it works fine to scan single hosts. nmap uses raw IP packets in novel ways to determine what hosts are available on the network, what services (application name and version) those hosts are offering, what operating systems (and OS versions) they are running, what type of packet filters/firewalls are in use, and dozens of other characteristics. While nmap is commonly used for security audits, many systems and network administrators find it useful for routine tasks such as network inventory, managing service upgrade schedules, and monitoring host or service uptime.
The Nmap Scripting Engine (NSE) is one of Nmap’s most powerful and flexible features. It allows users to write (and share) simple scripts to automate a wide variety of networking tasks. Those scripts are then executed in parallel with the speed and efficiency you expect from Nmap. Users can rely on the growing and diverse set of scripts distributed with Nmap, or write their own to meet customer needs.
vscan puts an additional value into vulnerability scanning with nmap. It uses NSE scripts which can add flexibility in terms of vulnerability detection and exploitation. Below there are some of the features that NSE scripts provide
- Network discovery
- More sophisticated version detection
- Vulnerability detection
- Backdoor detection
- Vulnerability exploitation
This tool uses the path /usr/share/nmap/scripts/ where the nse scripts are located in Kali Linux
The tool performs the following
- check the communication to the target hosts by checking icmp requests
- takes as input a protocol name such as http and executes all nse scripts related to that protocol
- if any vulnerability triggers it saves the output into a log file
- it may perform all of the above actions for a range of IP addresses
If the tool finds a vulnerability in a certain protocol it keeps the output into a log file which is saved in the following location /home/vulnerabilities_enumeration/http_vulnerabilities/http_vulnerabilities/http_vulnerabilities.txt In this example the folders have been created using the protocol prefix which in the current occasion is the http protocol.
Installing
git clone https://github.com/xvass/vscan.git
cd vscan
./vscan -h
Usage
./vscan.sh <ip_range> <protocol> <port> <Pn (optional)>
./vscan.sh <ips_file> <protocol> <port> <Pn (optional)>
./vscan.sh <ip> <protocol> <port> <Pn (optional)>
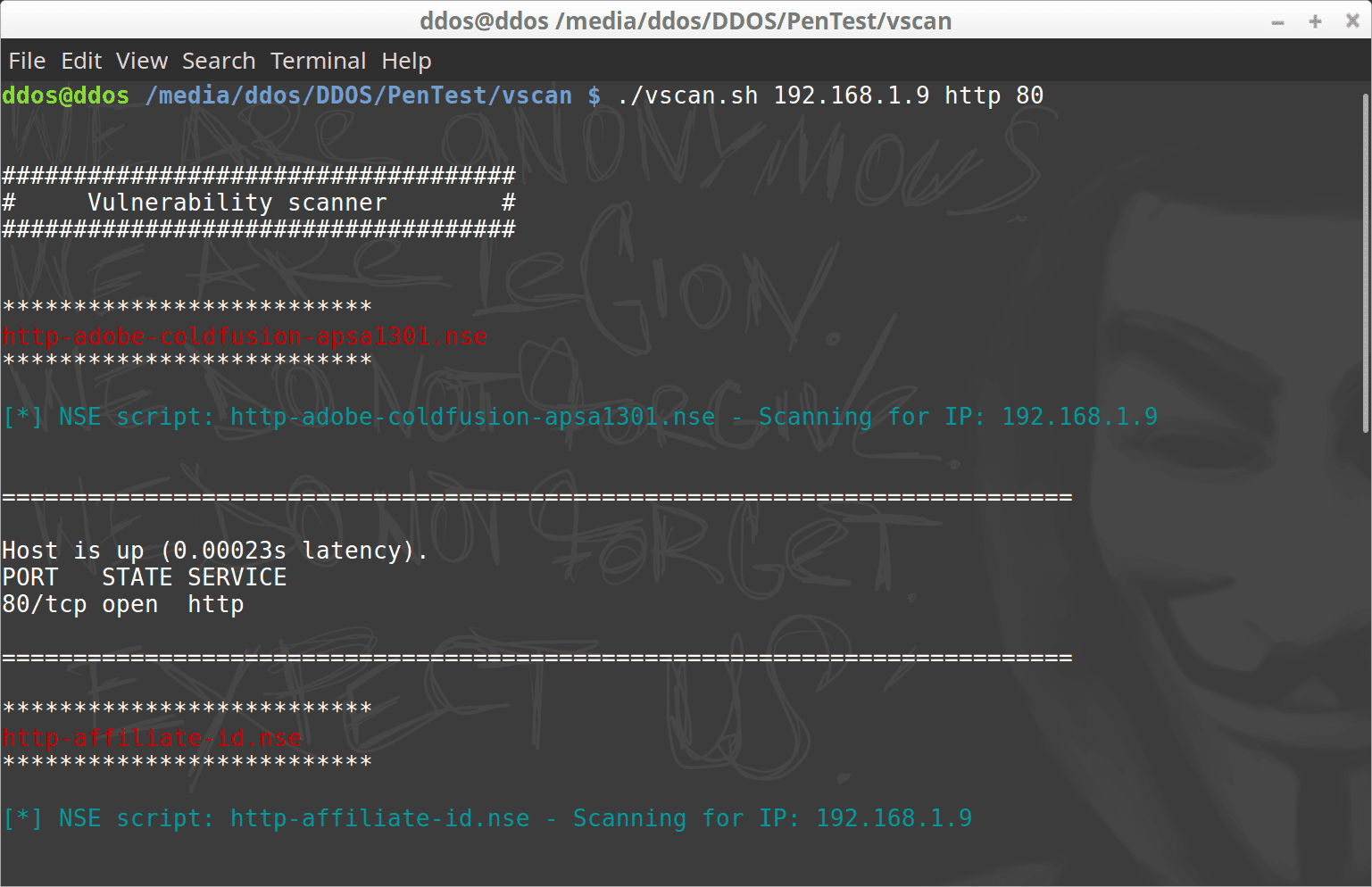
Demo






