Windows-Kernel-Explorer: powerful Windows kernel research tool
Windows Kernel Explorer (you can simply call it “WKE”) is a free but powerful Windows kernel research tool. It supports from Windows XP to Windows 10, 32-bit and 64-bit. Compare to popular tools (such as WIN64AST and PCHunter), WKE is a highly customizable tool and it can run on the latest Windows 10 without updating binary files.
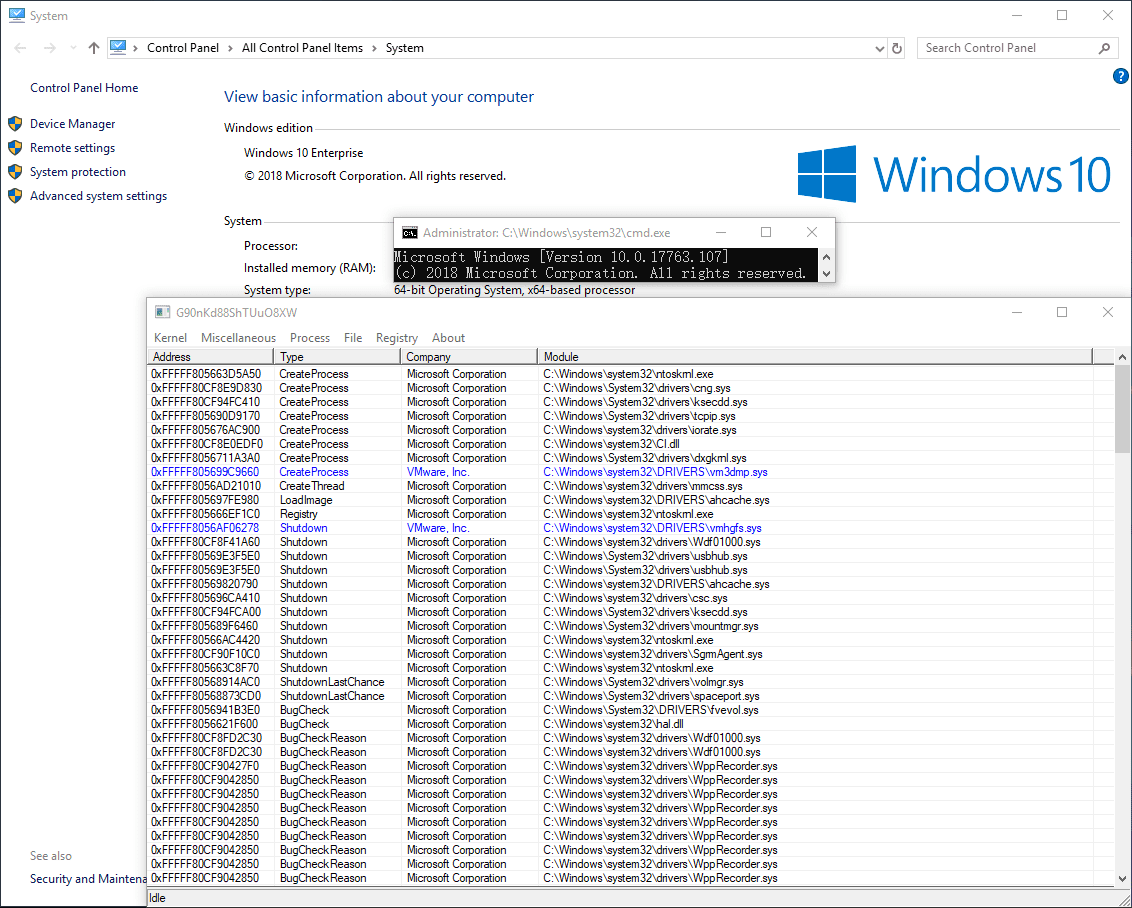
How WKE works on the latest Windows 10
WKE will automatically download required symbol files if no native support for the current system, 90% of the features will work after this step. For some needed data that doesn’t exist in symbol files, WKE will try to get them from the DAT file (so, when new Windows 10 releases, I will upload the newest DAT file to GitHub). If there is no internet access for WKE, 50% of the features will still work. Currently, native support is available from Windows XP to Windows 10 RS3, RS4 and RS5 are fully supported by parsing symbol files and DAT file.
How to customize WKE
You can customize WKE by editing the configuration file. Currently, you can set the device name and symbolic link name of driver, and altitude of the filter. You can also enable kernel-mode and user-mode characteristics randomization to avoid being detected by malware. If you rename the EXE file of WKE, then you need to rename SYS/DAT/INI files together with the same name.
About digital signature
Due to I don’t have a digital certificate, I have to use the leaked digital certificate from HT SRL to sign drivers of WKE. I use “DSEFIX” as an alternative solution to bypass DSE, you can try to launch WKE with “WKE_dsefix.bat” if WKE loads driver unsuccessfully on your system. Signing files with the HT SRL digital certificate causes a side effect: almost all anti-virus software consider files with HT SRL digital signature are viruses because many hackers use it to sign malwares since 2015. If you don’t trust WKE, you can run it in a test environment, or monitor its network activity on your router.
Main Features
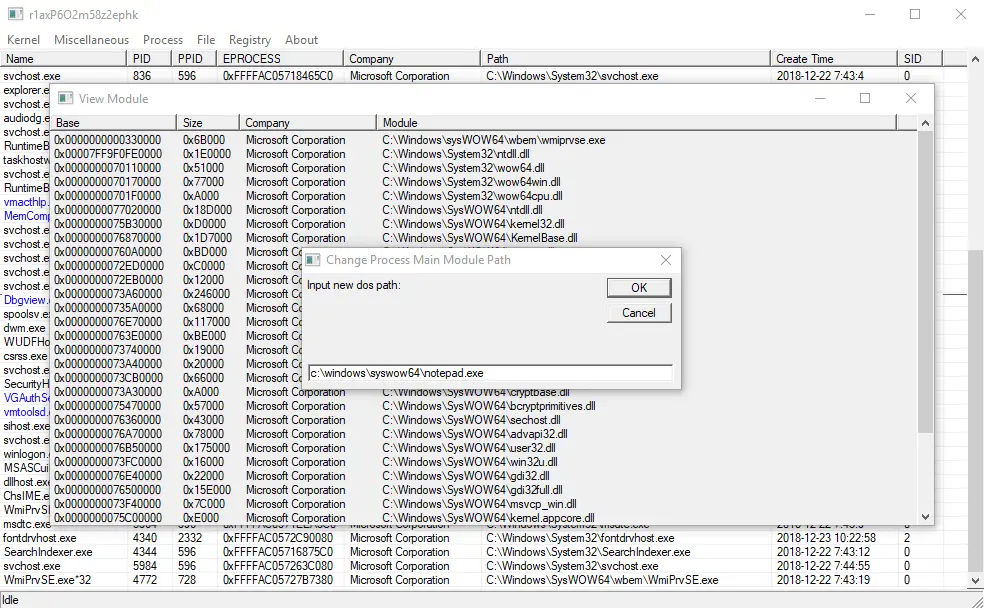
- Process management (Module, Thread, Handle, Memory, Window, Windows Hook, etc.)
- File management
- Registry management
- Kernel-mode callback, filter, timer, NDIS blocks and WFP callout functions management
- Kernel-mode hook scanning (MSR, EAT, IAT, CODE PATCH, SSDT, SSSDT, IDT, IRP, OBJECT)
- User-mode hook scanning (Kernel Callback Table, EAT, IAT, CODE PATCH)
- Memory editor and symbol parser (it looks like a simplified version of WINDBG)
- Protect process, hide/protect/redirect file or directory, protect registry and falsify registry data
- Path modification for driver, process and process module
- Enable/disable some obnoxious Windows components






