Xpath: detecting and exploiting error-based injection security
What is XPath?
XPath Injection
Similar to SQL injection, XPath injection occurs when the site uses the information entered by the user to construct the request for XML data. An attacker sends specially constructed information to the site to explore how the XML used by the site is constructed, and even to obtain data that is not available in the normal way. When XML data is used for account authentication, an attacker can also elevate his privileges. By querying XML with XPath, XPath is a simple, descriptive declaration that allows an XML request to determine the location of some information in XML. (Perhaps equivalent to a path query). Similar to SQL, when looking for the information you can specify specific attributes and characteristics to match the information. When you use xml for your website, you typically accept some form of string request to confirm the location of the content and display the content on the page. This input must be reviewed to ensure that does not return the wrong data. XPath is a standard language, its syntax is generally independent, which means that attacks against it can be automated, in this respect with the SQL injection is no different (sqlmap).
More info, please read my articles here.
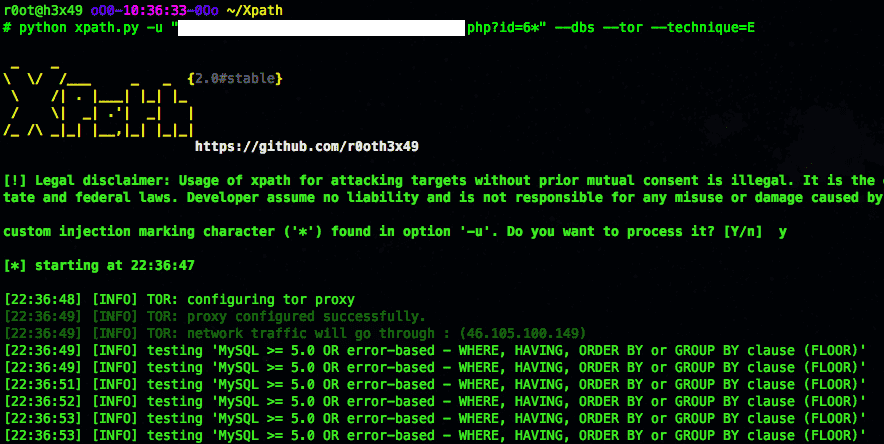
Xpath is a python open source Sql injector that automates the process of detecting and exploiting error-based injection security flaws. At the moment, DBMS supported by XPath is mysql. Please note that this project is an early state. As such, you might find bugs, flaws or malfunction. Use it at your own risk!.
Installation
git clone https://github.com/r0oth3x49/Xpath.git
Usage





