xsshell: XSS reverse shell framework
XSShell
XSShell is a cross-site-scripting reverse shell… Okay, well maybe it’s not a true reverse shell, but it will allow you to interact in real time with an XSS victim’s browser.
Just run the xsshell binary to set up your listener endpoint, do your XSS thing to get the exploit js onto the victim’s browser, and as soon as they run it you should see something like this pop up in your console:
Once you have a connection you can execute any javascript file you want on the browser, and have that script return data to your console. This may not seem very useful at first, but it allows you to be more tactical and react in real time to the environment that the script is running on. Environments like say… an admin page used to approve and manage orders placed on a retail site 🙂
XSShell also comes with a number of premade XSS payloads to use:
- \alert – send a js alert message
- \cs – get cookies and any updates to the cookies
- \gi – download all images on the page
- \kl – key logger
- \ll – list all links on the page
- \src – download the current page source
- \pfl – show the user a modal and prompt them to login
- \xhr – make xhr requests in the context of the victim’s browser
- \ct – crash the victim’s browser tab
- \wcs – attempt to take a snapshot from the victim’s webcam (WARNING: most modern browsers will prompt for access to webcams)
Install
go get github.com/raz-varren/xsshell
go install github.com/raz-varren/xsshell
Mods
If you modify any of the JS files in this package, make sure you run:
go generate github.com/raz-varren/xsshell…
go install github.com/raz-varren/xsshell
This will ensure that the updated files are packed into the binary.
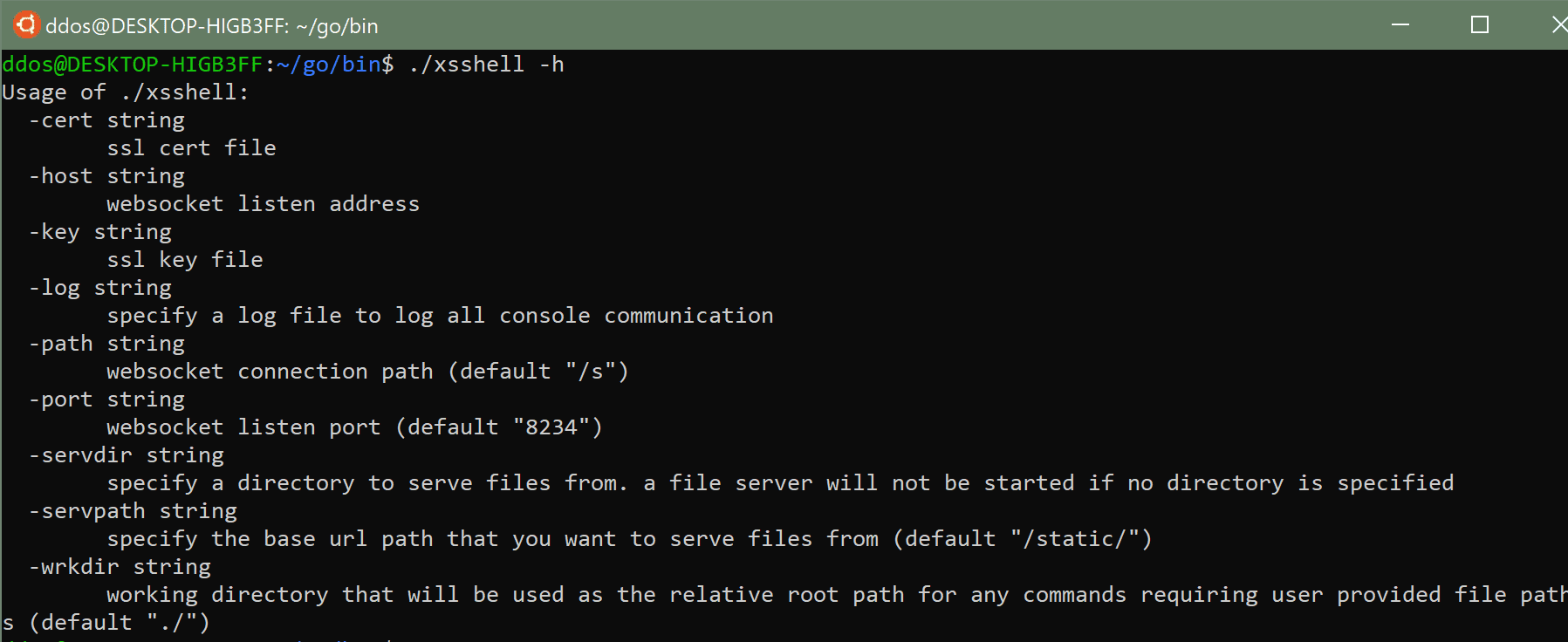
Usage
The xsshell command:
Copyright (c) 2019 Raz Varren
Source: https://github.com/raz-varren/






