amass v4.2 releases: In-depth subdomain enumeration written in Go
The OWASP Amass tool suite obtains subdomain names by scraping data sources, recursive brute forcing, crawling web archives, permuting/altering names, and reverse DNS sweeping. Additionally, Amass uses the IP addresses obtained during resolution to discover associated netblocks and ASNs. All the information is then used to build maps of the target networks.

Use
The most basic use of the tool, which includes reverse DNS lookups and name alterations:
$ amass -d example.com
Add some additional domains to the enumeration:
$ amass -d example1.com,example2.com -d example3.com
You can also provide the initial domain names via an input file:
$ amass -df domains.txt
Get amass to provide the sources that discovered the subdomain names and print summary information:
$ amass -v -d example.com
[Google] www.example.com
[VirusTotal] ns.example.com
…
13242 names discovered – scrape: 211, dns: 4709, archive: 126, brute: 169, alt: 8027
Have amass print IP addresses with the discovered names:
$ amass -ip -d example.com
Have amass write the results to a text file:
$ amass -ip -o out.txt -d example.com
Have all the data collected written to a file as individual JSON objects:
$ amass -json out.txt -d example.com
Specify your own DNS resolvers on the command-line or from a file:
$ amass -v -d example.com -r 8.8.8.8,1.1.1.1
The resolvers file can be provided using the following command-line switch:
$ amass -v -d example.com -rf data/resolvers.txt
If you would like to blacklist some subdomains:
$ amass -bl blah.example.com -d example.com
The blacklisted subdomains can be specified from a text file as well:
$ amass -blf data/blacklist.txt -d example.com
The amass feature that performs alterations on discovered names and attempt resolution can be disabled:
$ amass -noalts -d example.com
Use active information gathering techniques to attempt DNS zone transfers on all discovered authoritative name servers and obtain TLS/SSL certificates for discovered hosts on all specified ports:
$ amass -active -d example.com net -p 80,443,8080
Caution, this is an active technique that will reveal your IP address to the target organization.
Have amass perform brute force subdomain enumeration as well:
$ amass -brute -d example.com
By default, amass performs recursive brute forcing on new subdomains; this can be disabled:
$ amass -brute -norecursive -d example.com
If you would like to perform recursive brute forcing after enough discoveries have been made:
$ amass -brute -min-for-recursive 3 -d example.com
Change the wordlist used during the brute-forcing phase of the enumeration:
$ amass -brute -w wordlist.txt -d example.com
Throttle the rate of DNS queries by number per minute:
$ amass -freq 120 -d example.com
Allow amass to include additional domains in the search using reverse whois information:
$ amass -whois -d example.com
You can have amass list all the domains discovered with reverse whois before performing the enumeration:
$ amass -whois -l -d example.com
Only the first domain provided is used while performing the reverse whois operation.
Network/Infrastructure Options
Caution: If you use these options without specifying root domain names, amass will attempt to reach out to every IP address within the identified infrastructure and obtain names from TLS certificates. This is “loud” and can reveal your reconnaissance activities to the organization being investigated.
If you do provide root domain names on the command-line, these options will simply serve as constraints to the amass output.
All the flags are shown here require the ‘net’ subcommand to be specified first.
To discover all domains hosted within target ASNs, use the following option:
$ amass net -asn 13374,14618
To investigate within target CIDRs, use this option:
$ amass net -cidr 192.184.113.0/24,104.154.0.0/15
To limit your enumeration to specific IPs or address ranges, use this option:
$ amass net -addr 192.168.1.44,192.168.2.1-64
By default, port 443 will be checked for certificates, but the ports can be changed as follows:
$ amass net -cidr 192.168.1.0/24 -p 80,443,8080
Using a Proxy (still under development)
The amass tool can send all its traffic through a proxy, such as socks4, socks4a, socks5, http, and https. Do not use this to send the traffic through Tor, since that network does not support UDP traffic.
$ amass -v -proxy socks5://user:password@192.168.1.1:5050 example.com
Changelog v4.2
- 87f73be updates to the collection function
- 9fdfaf0 updated docs to be consistent with Asset DB
- 8c6361c removed the db subcommand now found in oam_subs
Download
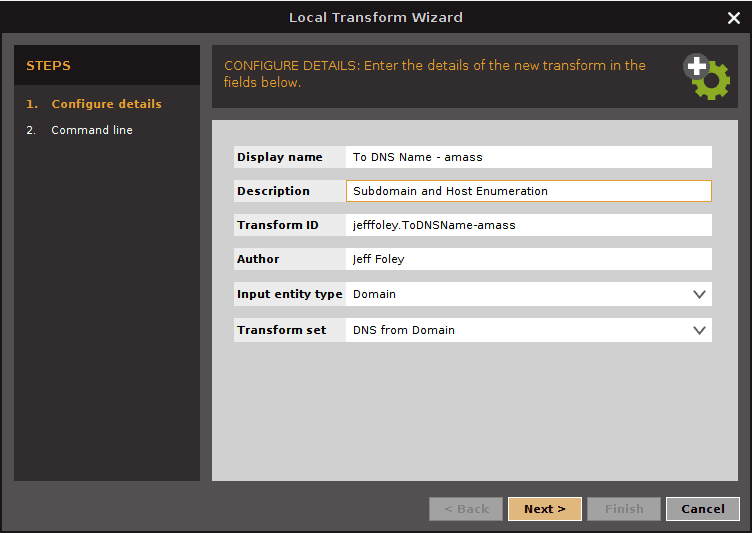
Copyright 2023 Jeff Foley. All rights reserved.
Source: https://github.com/caffix/