Introduction
ARP
short for Address Resolution Protocol, ARP is a used with the IP for mapping a 32-bit Internet Protocol address to a MAC address that is recognized in the local network specified in RFC 826. Once recognized, the server or networking device returns a response containing the required address.
Consider the situation where the computers A and B are in different LANs and linked to each other through the Internet. To transmit data, the computer A uses B PC IP-address as the destination address and sends the packet to the Internet. After going through a series of routers, it hits the network gateway, which belongs to the computer B.
The local B PC network address used for 6-byte MAC address, and when the package reaches the gateway, a further delivery on the LAN data is only possible if you know the MAC -address computer B. If the gateway MAC-address is not known, it sends a network broadcast ARP-request, the essence of which is as follows: “The computer with the IP-address B, let me know (lock) your MAC-address”.Because broadcast request, it reaches the computer B, and in response it sends ARP-reply with its MAC-address. The rest of the computers on the network does not send any packets on the gateway ARP-request, because have IP-addresses that are different from the computer IP-addresses B. Gateway, receiving MAC-address of the computer B, enters into its ARP-table (cache) compliance with the IP-address and the MAC-address of the computer B, and then sends the data to it, obtained via the Internet from the computer A. at the same time, the computer enters B in its ARP-table match the gateway IP and MAC addresses to be able to send data to computer A. At first glance, everything should work easily and reliably, if not for one feature – ARP does not authenticate-ARP requests and ARP responses-and allows you to send ARP-replies network nodes at random, ie, even if the node is not sent on the network no ARP-requests. Spontaneous answers are needed, for example to identify IP-address conflicts in the network.
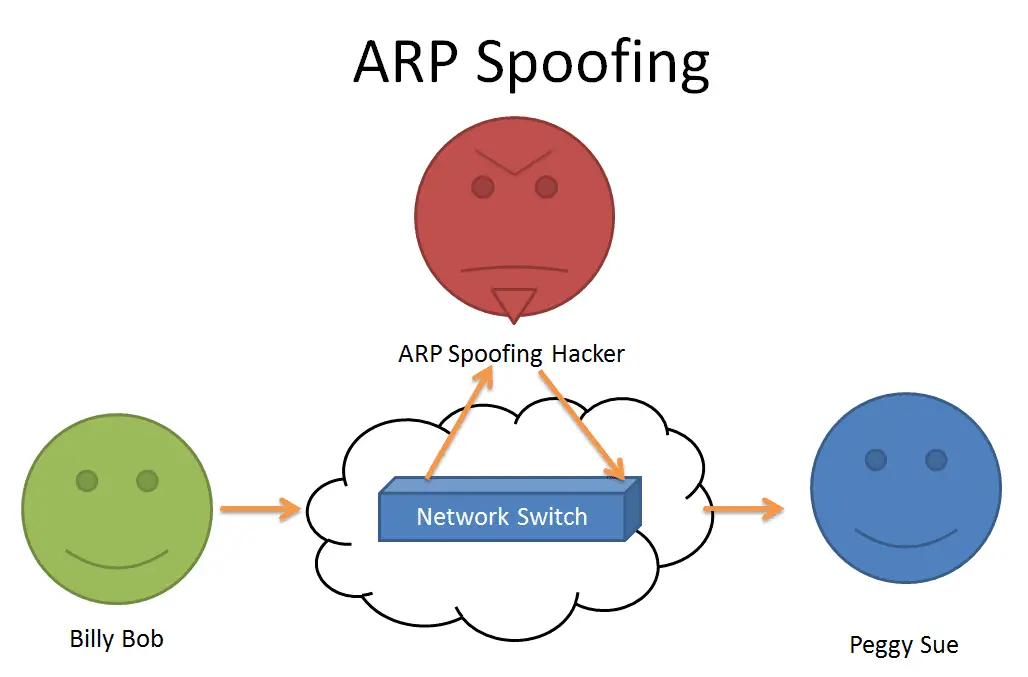
ARP spoofing attack
Assume that we need to listen to the data transmitted between computers A and B. Our computer is in the same local area network with computer B. We have a MAC-address, we know the MAC address-B PC and MAC-address of the gateway of our local network.
Computers in modern LANs connected with each other through switches. The switch “remembers” which port is connected to the host how the MAC-address. Those. receiving a packet from the computer B gateway, we do not get this package, as he will not be sent to all ports on the switch, but only the one which, according to the switch is now connected to the gateway. At a time when used hubs instead of switches, we could hear the traffic without any problems.
ARP-spoofing attack is often referred to as ARP-cache poisoning, and this name is quite telling.
Because we are allowed to send ARP-replies to any network node when we want, we will send the ARP-response gateway such content “I host with IP-address B PC, and here is my MAC-address [MAC-address of our host]” and the computer B will send ARP-response to such content, “I lock my MAC-address [MAC-address again our host].” After receiving these packets, the gateway and the computer B will update its ARP-cache.
Now, if the computer B wants to send data over the Internet computer A, it will send its data as it considers consistent with its ARP-table on the MAC-address of the gateway, when in fact the data will be sent to our MAC-address, and we in turn, will send them on to this MAC-address of the gateway.
Implementation ARP spoofing attack
- Using arpsoof
For the arp-spoofing attack in Kali Linux transit packets should be allowed.
Allow IPv4 forwarding can be editing the file /etc/sysctl.conf is necessary to uncomment the line
net.ipv4.ip_forward = 1
Then run the command
sysctl -p /etc/sysctl.conf
If you do not want to allow this on a regular basis, you can enable forwarding so
echo 1 > /proc/sys/net/ipv4/ip_forwardAs it is necessary to ensure that transit traffic is not blocked by iptables rules.
arpspoof -i eth0 -t ip
-i – indicates the interface connected to the local network of the victim
-t – specifies the IP-address of the host, arp-cache you want to “poison”. If the key is not specified, the attack will be carried out on all hosts in a network, ie, all participants in the network, when you try to send a packet gateway will send it to us. - Using metasploit
use auxiliary/spoof/arp/arp_poisoning module