Security auditing and static code analysis
Aura is a static analysis framework developed as a response to the ever-increasing threat of malicious packages and vulnerable code published on PyPI.
Aura is a static analysis framework developed as a response to the ever-increasing threat of malicious packages and vulnerable code published on PyPI.
Project goals:
- provide an automated monitoring system over uploaded packages to PyPI, alert on anomalies that can either indicate an ongoing attack or vulnerabilities in the code
- enable an organization to conduct automated security audits of the source code and implement secure coding practices with a focus on auditing 3rd party code such as python package dependencies
- allow researches to scan code repositories on a large scale, create datasets and perform analysis to further advance research in the area of vulnerable and malicious code dependencies
Feature list:
- Suitable for analyzing malware with a guarantee of a zero-code execution
- Advanced deobfuscation mechanisms by rewriting the AST tree – constant propagations, code unrolling, and other dirty tricks
- Recursive scanning automatically unpacks archives such as zips, wheels, etc.. and scans the content
- Support scanning also non-python files – plugins can work in a “raw-file” mode such as the built-in Yara integration
- Scan for hardcoded secrets, passwords, and other sensitive information
- Custom diff engine – you can compare changes between different data sources such as typosquatting PyPI packages to what changes were made
- Works for both Python 2.x and Python 3.x source code
- High performance, designed to scan the whole PyPI repository
- Output in numerous formats such as pretty plain text, JSON, SQLite, SARIF, etc…
- Tested on over 4TB of compressed python source code
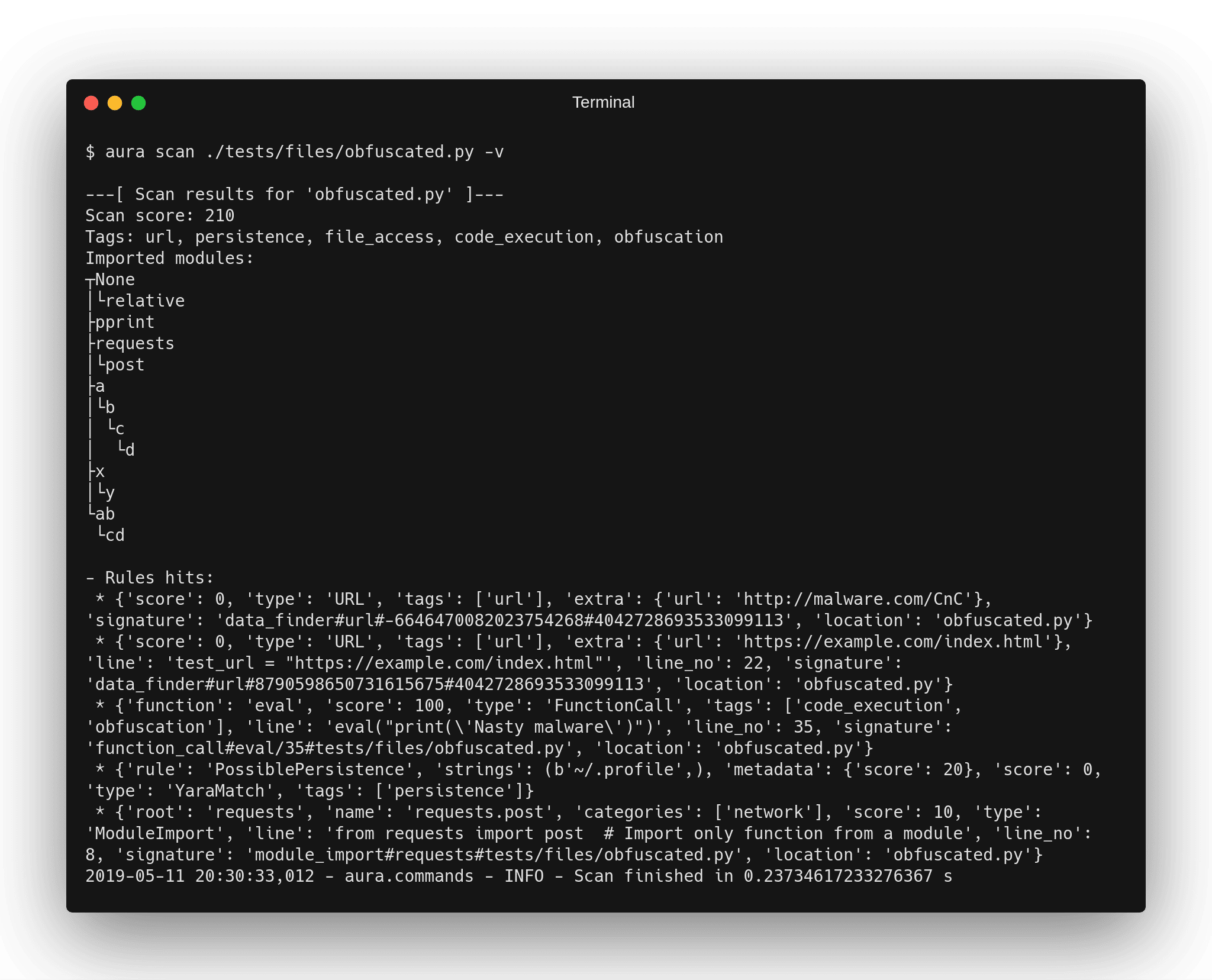
- Aura is able to report on code behavior such as network communication, file access, or system command execution
- Compute the “Aura score” telling you how trustworthy the source code/input data is
- and much much more…
Here is a quick overview of differences between Aura and other similar linters and SAST tools:
-
- input data:
-
- Other SAST tools – usually restricted to only python (target) source code and python version under which the tool is installed.
- Aura can analyze both binary (or non-python code) and python source code as well. Able to analyze a mixture of python code compatible with different python versions (py2k & py3k) using the same Aura installation.
-
- reporting:
-
- Other SAST tools – Aims at integrating well with other systems such as IDEs, CI systems with actionable results while trying to minimize false positives to prevent overwhelming users with too many non-significant alerts.
- Aura – reports as much information as possible that is not immediately actionable such as behavioral and anomaly analysis. The output format is designed for easy machine processing and aggregation rather than human-readable.
-
- configuration:
-
- Other SAST tools – The tools are fine-tuned to the target project by customizing the signatures to target specific technologies used by the target project. The overriding configuration is often possible by inserting comments inside the source code such as # nosec that will suppress the alert at that position
- Aura – it is expected that there is little to no knowledge in advance about the technologies used by code that is being scanned such as auditing a new python package for approval to be used as a dependency in a project. In most cases, it is not even possible to modify the scanned source code such as using comments to indicate to linter or aura to skip detection at that location because it is scanning a copy of that code that is hosted at some remote location.
Install & Use
Copyright (C) 2018 Martin Carnogursky & Mirza Zulfan
