CVE-2022-42889: Apache Commons Text code execution vulnerability
Recently, Apache Commons Text fixed a code execution vulnerability. This bug is caused when processing malicious input, an attacker could exploit this vulnerability to inject arbitrary commands and thus achieve remote code execution. By sending a specially crafted request, an attacker could exploit this vulnerability to execute arbitrary commands. Track as CVE-2022-42889 (CVSS 9.8), the flaw severity is important. The bug has been reported by Alvaro Munoz.
Apache Commons is an Apache project focused on all aspects of reusable Java components. Apache Commons Text is a library focused on algorithms working on strings.
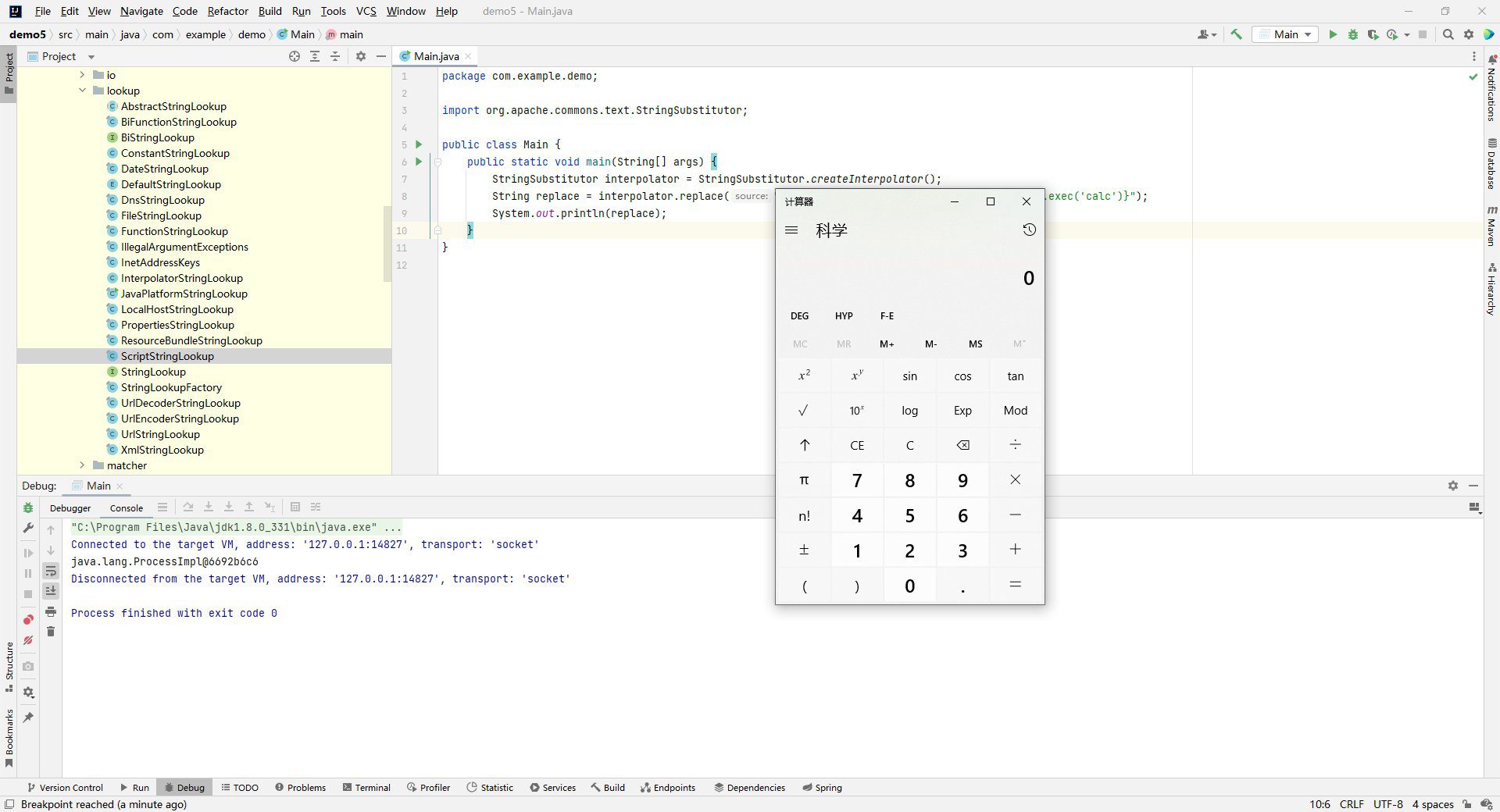
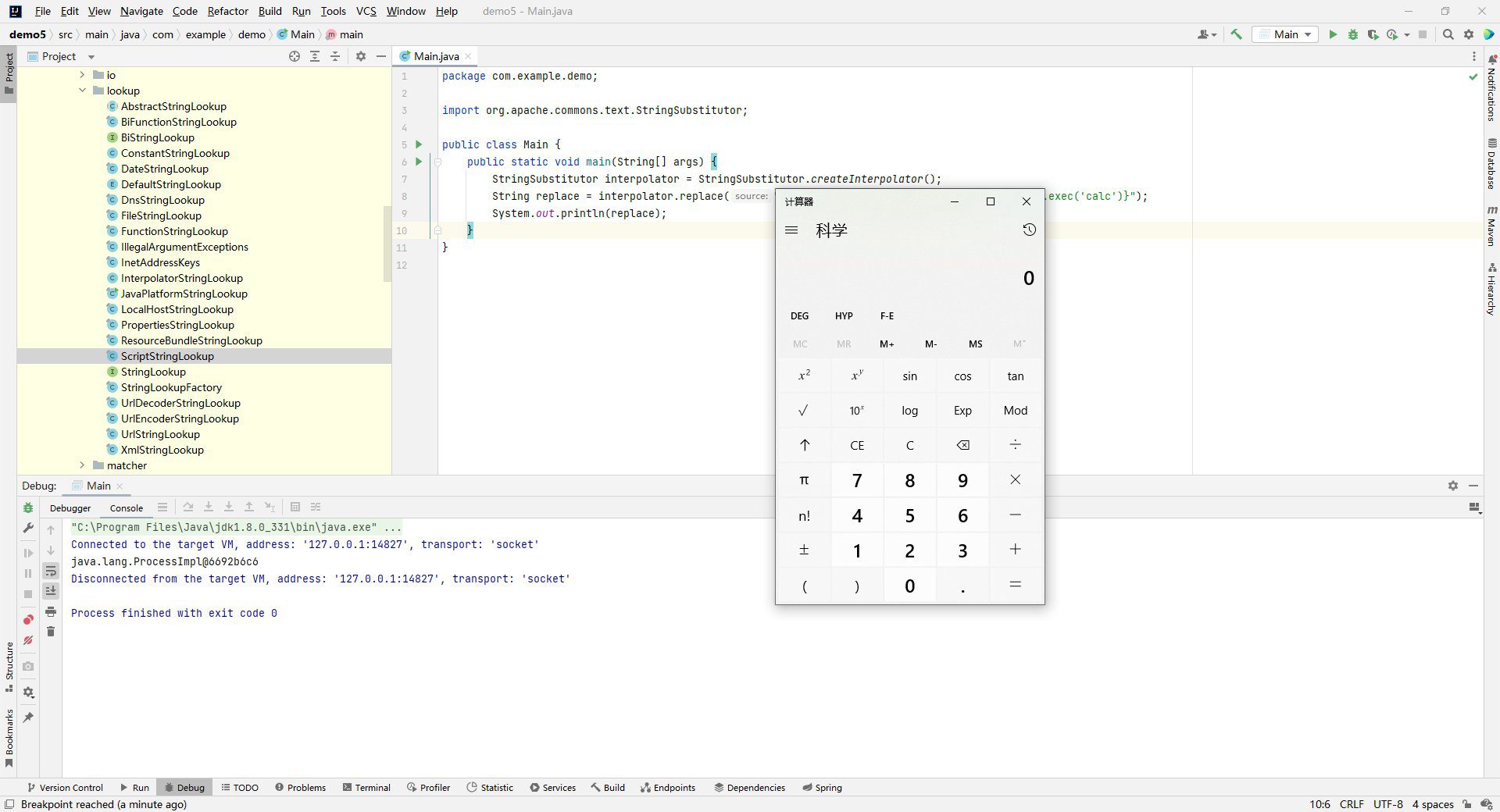
Image: Y4er_ChaBug
“Apache Commons Text performs variable interpolation, allowing properties to be dynamically evaluated and expanded. The standard format for interpolation is “${prefix:name}”, where “prefix” is used to locate an instance of org.apache.commons.text.lookup.StringLookup that performs the interpolation. Starting with version 1.5 and continuing through 1.9, the set of default Lookup instances included interpolators that could result in arbitrary code execution or contact with remote servers. These lookups are: – “script” – execute expressions using the JVM script execution engine (javax.script) – “dns” – resolve dns records – “url” – load values from urls, including from remote servers Applications using the interpolation defaults in the affected versions may be vulnerable to remote code execution or unintentional contact with remote servers if untrusted configuration values are used,” read the project’s mailing list.
The security vulnerability consists of injecting a malicious load on vulnerable Commons Text’s variable interpolation functionality, which will ask Apache Commons Text to fetch untrusted input from a remote attacker, with DNS requests, or via inline scripts. However, in this case, Apache Commons Text does not check the data to be processed by default, which means that malicious code can be executed if no filter has been implemented in the code of the vulnerable application.
The vulnerability exists in the StringSubstitutor interpolator object. “The StringSubstitutor when used with the default interpolators (StringSubstitutor.createInterpolator()) will perform string lookups that may lead to arbitrary code execution.”
In particular, if untrusted data flows into the StringSubstitutor.replace() or StringSubstitutor.replaceIn() methods, an attacker will be able to use the ScriptStringLookup to trigger arbitrary code execution.”
CVE-2022-42889 affects Apache Commons Text versions 1.5 through 1.9. At present, Apache Commons Text has fixed this vulnerability in the latest version (version 1.10), please install the unaffected version as soon as possible.





