gitleaks v8.18 releases: Searches full repo history for secrets and keys
gitleaks – Check git repos for secrets and keys
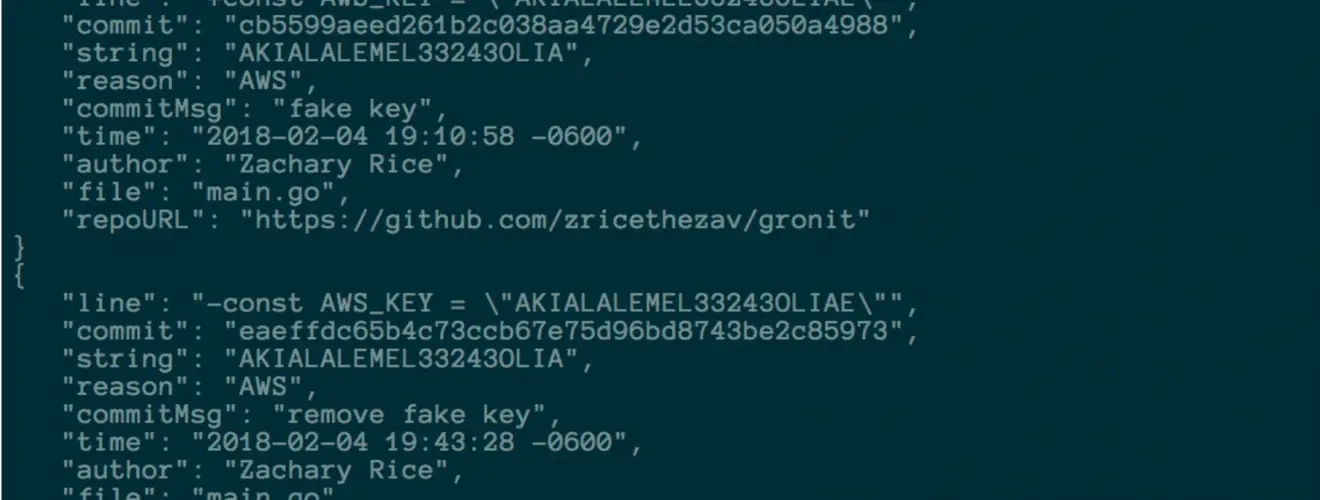
Gitleaks provides a way for you to find unencrypted secrets and other unwanted data types in git source code repositories.
As part of its core functionality, it provides;
- Github support includes support for the bulk organization and repository owner (user) repository scans, as well as pull request scanning for use in common CI workflows.
- Support for private repository scans, and repositories that require key-based authentication
- Output in CSV and JSON formats for consumption in other reporting tools and frameworks
- Externalised configuration for environment-specific customization including regex rules
- Customizable repository name, file type, commit ID, branchname, and regex whitelisting to reduce false positives
- High performance through the use of src-d’s go-git framework
It has been successfully used in a number of different scenarios, including;
- Adhoc scans of local and remote repositories by filesystem path or clone URL
- Automated scans of github users and organizations (both public and enterprise platforms)
- As part of a CICD workflow to identify secrets before they make it deeper into your codebase
- As part of a wider secret auditing automation capability for git data in large environments
Changelog v8.8
- Fix inconsistent generated values in config by @rgmz in #1200
- feat: add JFrog API and Identity keys by @baruchiro in #1233
- Add entropy check to plaid client/secret ID rules by @mortenson in #1213
- Update config template logic by @rgmz in #1201
- Include entropy in Plaid rule file by @rgmz in #1252
- refactor: fix #722 properly by @L11R in #1250
Download
Usage







