goblob: fast enumeration tool for publicly exposed Azure Storage blobs
Goblob
Goblob is a lightweight and fast enumeration tool designed to aid in the discovery of sensitive information exposed publicy in Azure blobs, which can be useful for various research purposes such as vulnerability assessments, penetration testing, and reconnaissance.
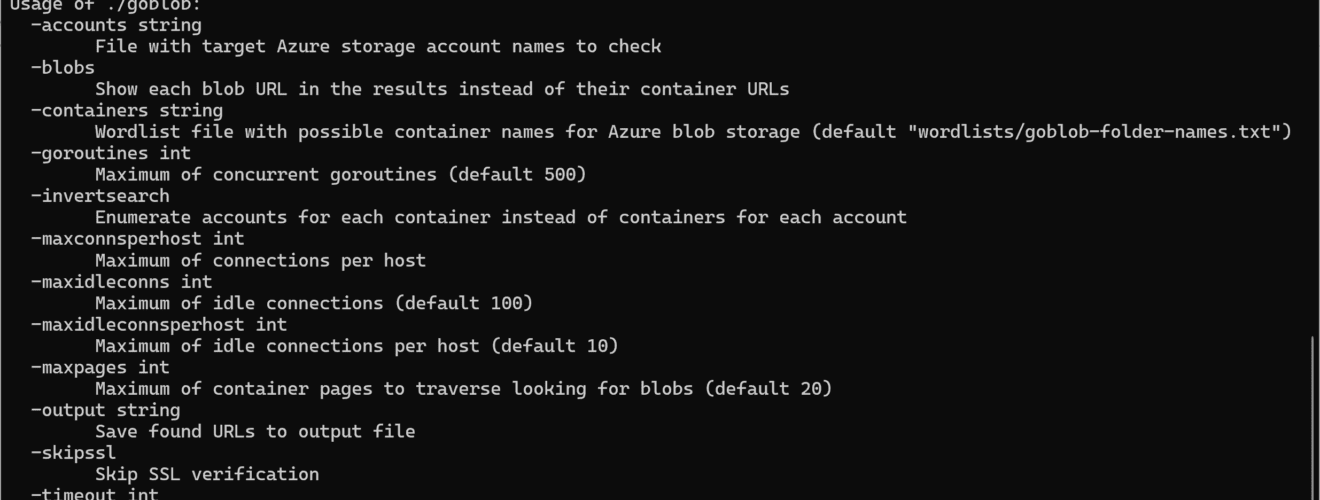
Warning. Goblob will issue individual goroutines for each container name to check in each storage account, only limited by the maximum number of concurrent goroutines specified in the -goroutines flag. This implementation can exhaust bandwidth pretty quickly in most cases with the default wordlist, or potentially cost you a lot of money if you’re using the tool in a cloud environment. Make sure you understand what you are doing before running the tool.
Use
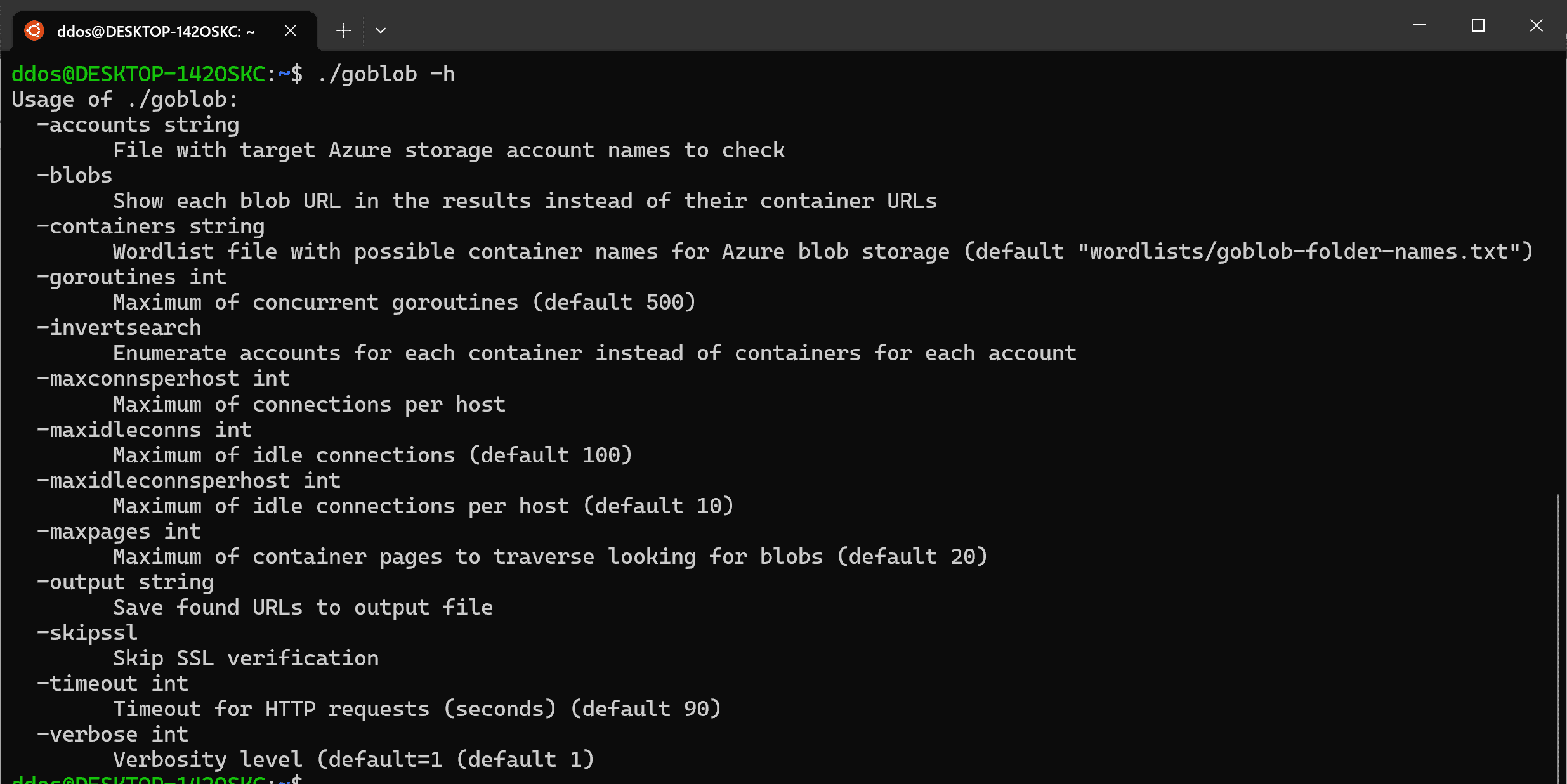
To use goblob simply run the following command:
$ ./goblob <storageaccountname>
Where <storageaccountname> is the target storage account to enumerate public Azure blob storage URLs on.
You can also specify a list of storage account names to check:
$ ./goblob -accounts accounts.txt
By default, the tool will use a list of common Azure Blob Storage container names to construct potential URLs. However, you can also specify a custom list of container names using the -containers option. For example:
$ ./goblob -accounts accounts.txt -containers wordlists/goblob-folder-names.txt
The tool also supports outputting the results to a file using the -output option:
$ ./goblob -accounts accounts.txt -containers wordlists/goblob-folder-names.txt -output results.txt
If you want to provide accounts to test via stdin you can also omit -accounts (or the account name) entirely:
$ cat accounts.txt | ./goblob
Wordlists
Goblob comes bundled with basic wordlists that can be used with the -containers option:
- wordlists/goblob-folder-names.txt (default) – Adaptation from koaj’s aws-s3-bucket-wordlist – a wordlist containing generic bucket names that are likely to be used as container names.
- wordlists/goblob-folder-names.small.txt – Subset of the default wordlist containing only words that have been found as container names in a real experiment with over 35k distinct storage accounts + words from the default wordlist that are part of the NLTK corpus.
- wordlists/goblob-folder-names.micro.txt – Subset of the small wordlist containing only words that have been found as container names in a real experiment with over 35k distinct storage accounts.
Download
Copyright (c) 2023 Artur Henrique Marzano Gonzaga






