goGetBucket: AWS S3 Bucket discovery through alterations and permutations
goGetBucket – AWS S3 Bucket discovery through alterations and permutation
When performing a recon on a domain – understanding assets they own is very important. AWS S3 bucket permissions have been confused time and time again, and have allowed for the exposure of sensitive material.
What this tool does, is enumerate S3 bucket names using common patterns I have identified during my time bug hunting and pentesting. Permutations are supported on a root domain name using a custom word list. I highly recommend the one packaged within AltDNS.
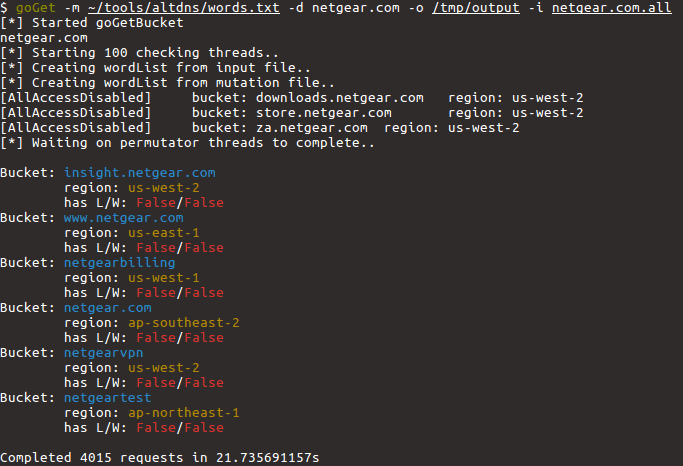
The following information about every bucket found to exist will be returned:
- List Permission
- Write Permission
- Region the Bucket exists in
- If the bucket has all access disabled
Installation
go get -u github.com/glen-mac/goGetBucket
Usage
goGetBucket -m ~/tools/altdns/words.txt -d <domain> -o <output> -i <wordlist>
Copyright (C) glen-mac
Source: https://github.com/glen-mac/





