crosslinked v0.3 releases: LinkedIn enumeration tool
CrossLinked
CrossLinked simplifies the processes of searching LinkedIn to collect valid employee names when performing password spraying or another security testing against an organization. Using similar search engine scraping capabilities found in tools like subscraper and pymeta, CrossLinked will find valid employee names and help format the data according to the organization’s account naming convention. Results will be written to a ‘names.txt’ file in the current directory for further testing.
Changelog v0.3
✅ Updated Documentation
✅ Updated User-Agents
✅ Added Advanced naming format
✅ Fixed Issue #20
Install
git clone https://github.com/m8r0wn/crosslinked
cd crosslinked
pip3 install -r requirements.txt
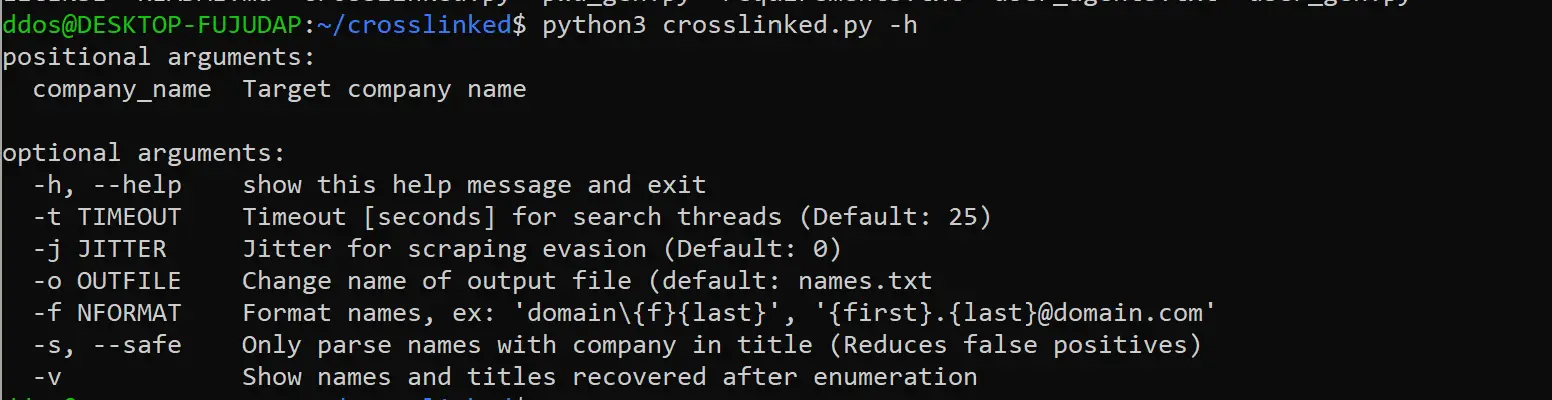
Usage
Additions
Two additional scripts are included in this repo to aid in generating potential username and password files:
- pwd_gen.py – Generates custom password lists using words and variables defined at the top of the script. Perform number/letter substitutions, append special characters, and more. Once configured, run the script with no arguments to generate a ‘passwords.txt’ output file.
- user_gen.py – Generates custom usernames using inputs from firstname.txt and lastname.txt files, provided at the command line. The format is defined similar to crosslinked.py and will be written to ‘users.txt’.
python3 user_gen.py -first top100_firstnames.txt -last top100_lastnames.txt -f “domain\{f}{last}”
Copyright (C) 2019 m8r0wn
Source: https://github.com/m8r0wn/





