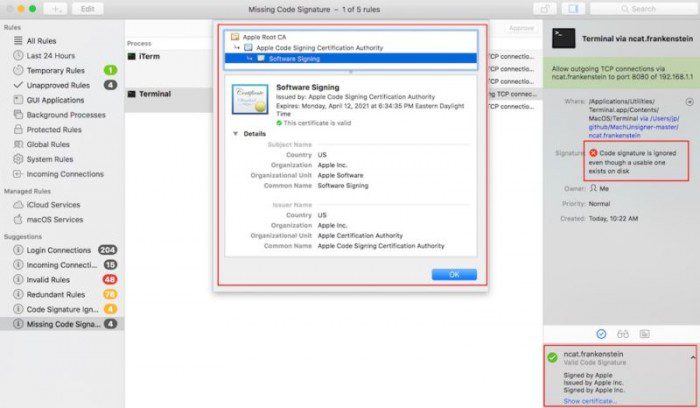
Researchers said that bypassing the signature check method is very easy and trivial. Almost all hackers who find it can disguise malicious code as an Apple-signed application. These digital signatures are core security features that let users know that the application is signed with the private key of the trusted party, just like the official Apple application.