OWASP ZAP v2.15 released: finding vulnerabilities in web applications
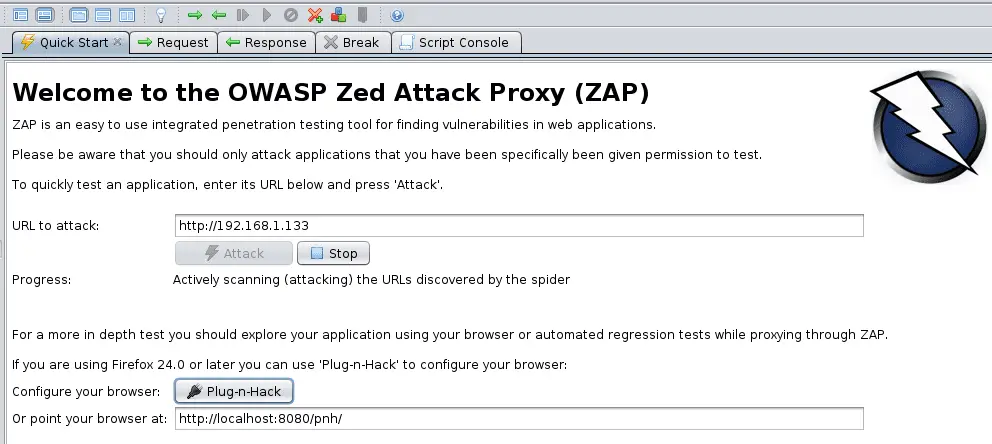
The OWASP Zed Attack Proxy (ZAP) is easy to use integrated penetration testing tool for finding vulnerabilities in web applications. It is designed to be used by people with a wide range of security experience and as such is ideal for developers and functional testers who are new to penetration testing as well as being a useful addition to an experienced pen testers toolbox.
ZAP provides automated scanners as well as a set of tools that allow you to find security vulnerabilities manually.
Some of ZAP’s features:
- Open source
- Cross-platform
- Easy to install (just requires java 1.7)
- Completely free (no paid for ‘Pro’ version)
- Ease of use a priority
- Comprehensive help pages
- Fully internationalized
- Translated into a dozen languages
- Community-based, with involvement, actively encouraged
- Under active development by an international team of volunteers
Some of ZAP’s functionality:
- Intercepting Proxy
- Traditional and AJAX spiders
- Automated scanner
- Passive scanner
- Forced browsing
- Fuzzer
- Dynamic SSL certificates
- Smartcard and Client Digital Certificates support
- Web sockets support
- Support for a wide range of scripting languages
- Plug-n-Hack support
- Authentication and session support
- Powerful REST-based API
- Automatic updating option
- Integrated and growing marketplace of add-ons
Changelog v2.15
Scripts as First Class Scan Rules
Active and passive scan script rules can now be treated as “first class” scan rules. This means that they can be individually referenced in an active scan policy, in the passive scan rules options, and in Automation Framework plans. In addition directories of scripts can now be added with all of the scripts enabled – this will make it much more straightfoward to manage script rules in automation.
Menu Items Restructured
The desktop context sensitive menu items have been reordered, and grouped in a more logical way. This should make it much easier to find the menu item you want, when you want it.
Set Logging Levels
A new -loglevel Command Line option allows you to set the log level, overriding the values specified in the log4j2.properties file in the home directory.
New API calls also allow you to set and view the current logging levels:
Action / core / setLogLevel: Sets the logging level for a given nameView / core / getLogLevel: Gets the detailed logging config, optionally filtered by name
Automation Framework GitHub Action
There is a new ZAP GitHub action – the ZAP Automation Framework Scan. The Automation Framework provides a great balance between ease of use and flexibility + functionality. If you want to perform any non-trivial automation with ZAP then the Automation Framework is probably your best bet.
New Docker Hub Organisation
We have a new DockerHub organisation for the ZAP Docker images: https://hub.docker.com/u/zaproxy We are still using the softwaresecurityproject org for 2.15.0 but we will probably not use it for the following releases. We do recommend that you switch from `softwaresecurityproject` to zaproxy sooner rather than later.
More…
Download
OWASP ZAP Tutorial
Copyright 2022 the ZAP Dev Team






