pmkidcracker: crack WPA2 passphrase with PMKID value without clients or de-authentication
pmkidcracker
This program is a tool written in Python to recover the pre-shared key of a WPA2 WiFi network without any de-authentication or requiring any clients to be on the network. It targets the weakness of certain access points advertising the PMKID value in EAPOL message 1.
How PMKID is Calculated
The two main formulas to obtain a PMKID are as follows:
- Pairwise Master Key (PMK) Calculation: passphrase + salt(ssid) => PBKDF2(HMAC-SHA1) of 4096 iterations
- PMKID Calculation: HMAC-SHA1[pmk + (“PMK Name” + bssid + clientmac)]
This is just for understanding, both are already implemented in find_pw_chunk and calculate_pmkid.
Obtaining the PMKID
Below are the steps to obtain the PMKID manually by inspecting the packets in Wireshark.
*You may use Hcxtools or Bettercap to quickly obtain the PMKID without the below steps. The manual way is for understanding.
To obtain the PMKID manually from wireshark, put your wireless antenna in monitor mode, and start capturing all packets with airodump-ng or similar tools. Then connect to the AP using an invalid password to capture the EAPOL 1 handshake message. Follow the next 3 steps to obtain the fields needed for the arguments.
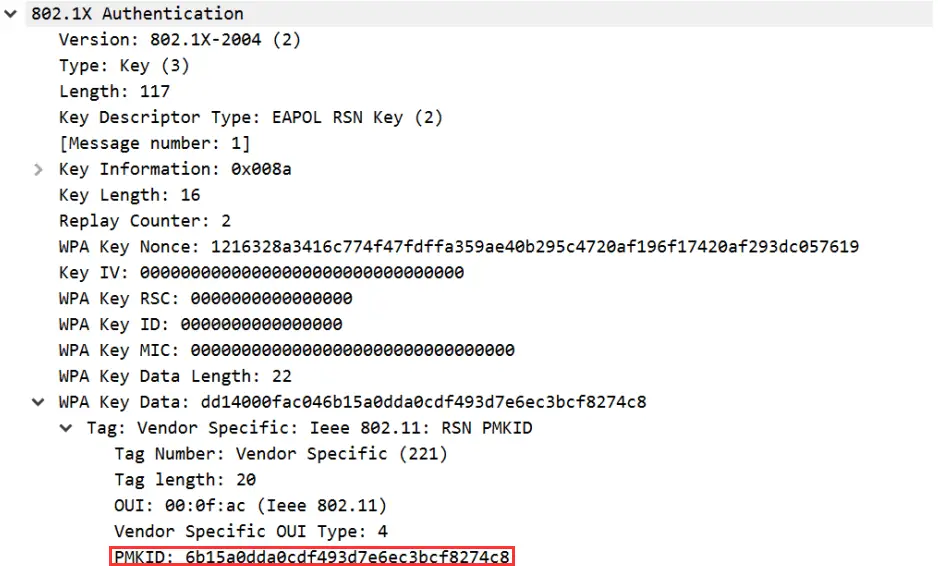
Open the pcap in WireShark:
- Filter with wlan_rsna_eapol.keydes.msgnr == 1 in WireShark to display only EAPOL message 1 packets.
- In EAPOL 1 pkt, Expand IEEE 802.11 QoS Data Field to obtain AP MAC, Client MAC
- In EAPOL 1 pkt, Expand 802.1 Authentication > WPA Key Data > Tag: Vendor Specific > PMKID is below
If an access point is vulnerable, you should see the PMKID value in the below screenshot:
Download
git clone https://github.com/n0mi1k/pmkidcracker.git
Use
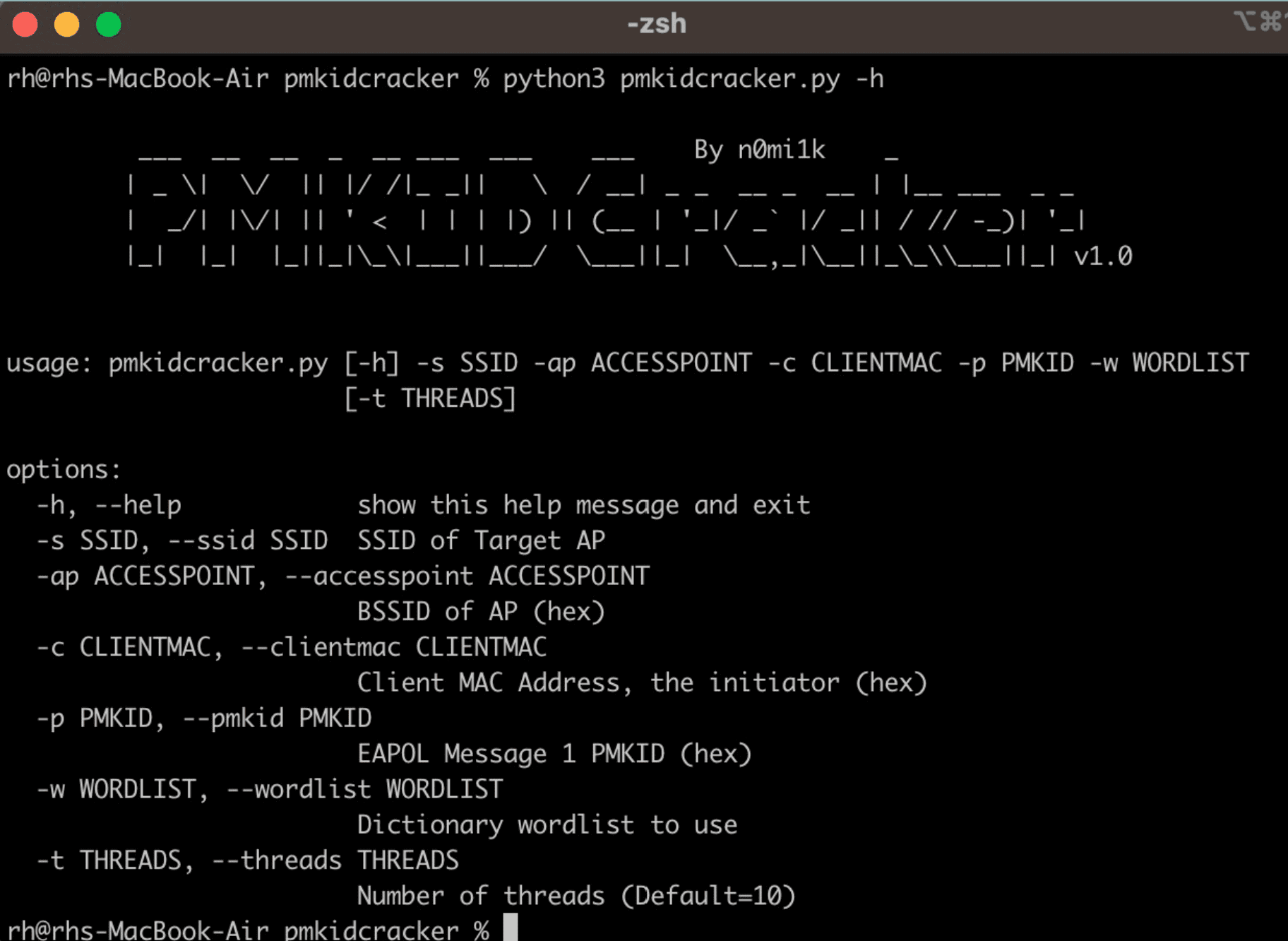
python pmkidcracker.py -s <SSID> -ap <APMAC> -c <CLIENTMAC> -p <PMKID> -w <WORDLIST> -t <THREADS(Optional)>
Copyright (c) 2023 n0mi1k
Source: https://github.com/n0mi1k/





