PoC released for Microsoft WordPad CVE-2023-36563 flaw exploited in attacks
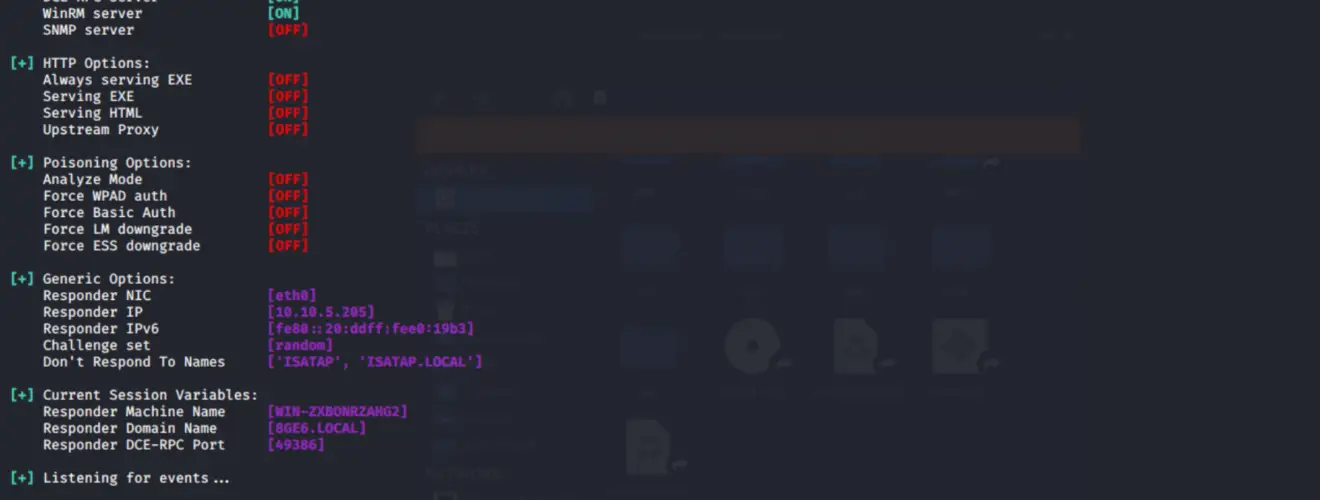
On October 23, security researcher Dillon Franke published a proof-of-concept (PoC) exploit for an actively exploited Microsoft WordPad information disclosure vulnerability tracked as CVE-2023-36563. This vulnerability allows attackers to steal NTLM hashes, which can then be cracked or used in NTLM Relay attacks to gain access to accounts.
CVE-2023-36563 was discovered internally by the Microsoft Threat Intelligence group. As per the October 2023 Patch Tuesday, the vulnerability came into the limelight with a CVSS v3.1 severity rating of 6.5. For the uninitiated, this might just sound like another technical hiccup. But in reality, this vulnerability allows hackers to swipe NTLM hashes when unsuspecting users open a document in WordPad.
NTLM hashes are cryptographic hashes of passwords that are used by Windows to authenticate users to remote servers. If an attacker can steal an NTLM hash, they can attempt to crack it using a variety of methods, or they can use it in an NTLM Relay attack to gain access to the account without having to know the password.
The vulnerability’s anatomy is quite intriguing. Dillon Franke, the astute security researcher who lifted the veil on the PoC and its nitty-gritty, stated that the flaw can be traced back to a legacy functionality. In essence, it’s a way to morph an OLE 1 storage object (OLESTREAM) into the modern IStorage format. By contriving a file imbued with a malicious OLE 1 LinkedObject, a hacker could manipulate authentication to a dubious server and whisk away the prized NTLM hashes.
Franke elaborated, “An unsafe transformation to an OLE LinkedObject was prompting the NTLM authentication. With this insight, the path to creating a potent payload was clear.” For the technically savvy, a deeper dive into the process can be found in Dillon Franke’s comprehensive report.

For all Windows aficionados, the clarion call is clear: install the October 2023 patch pronto. Not only does it address CVE-2023-36563, but it also patches up two more zero-day vulnerabilities that hackers have been exploiting with glee.






