pwndb: Search for leaked credentials using the Onion service
pwndb.py
pwndb.py is a python command-line tool for searching leaked credentials using the Onion service with the same name.
Installation
Just create a virtualenv, install the requirements and make sure Tor is running.
$ git clone https://github.com/davidtavarez/pwndb
$ cd pwndb
$ virtualenv venv
$ source venv/bin/activate
(venv) $ pip install -r requirements.txt
Use
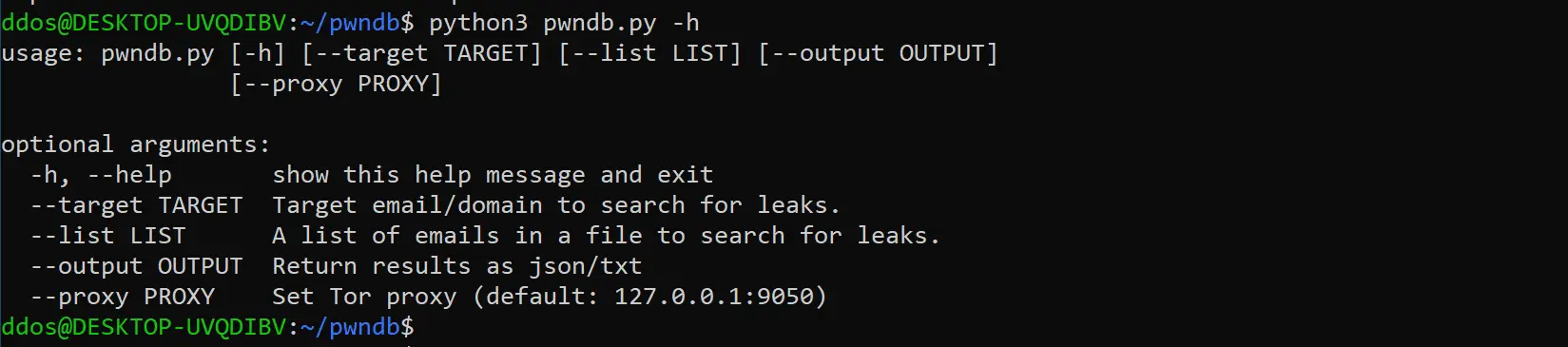
usage: pwndb.py [-h] [–target TARGET] [–list LIST] [–output OUTPUT]
optional arguments:
-h, –help show this help message and exit
–target TARGET Target email/domain to search for leaks.
–list LIST A list of emails in a file to search for leaks.
–output OUTPUT Return results as json/txt
Note: tor service must be up and running to be connected to port 9050
Disclaimer
[!] Legal disclaimer: Usage of pwndb.py for attacking targets without prior mutual consent is illegal. It is the end user’s responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused.
Copyright (c) 2019 David Tavarez
Source: https://github.com/davidtavarez/





