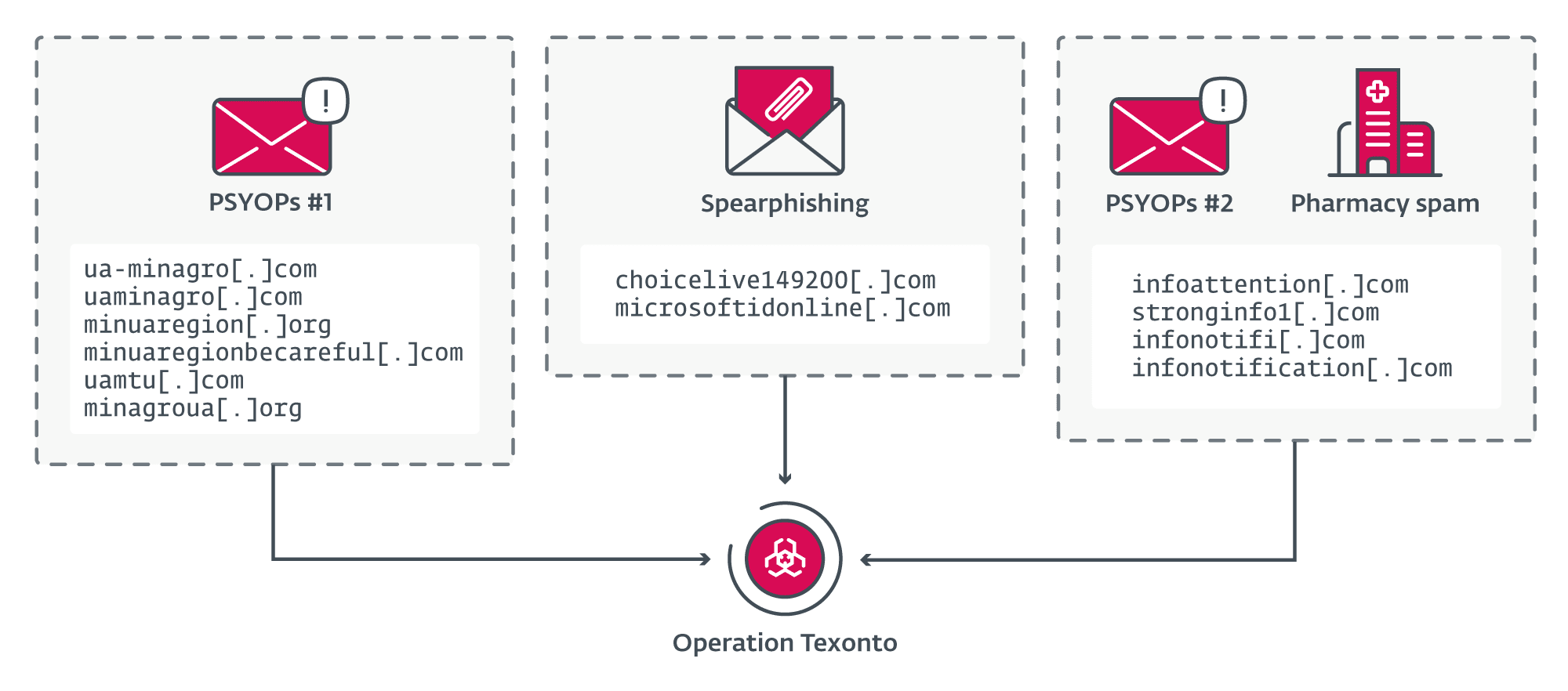
Operation Texonto summary | Image: ESET
ESET researchers have meticulously dissected a complex, ongoing influence operation named ‘Operation Texonto.’ This campaign, exhibiting strong alignment with Russian interests, blends espionage techniques with disinformation tactics to target Ukraine, Ukrainian speakers abroad, and potentially even internal Russian dissidents. Its evolution underscores the fluidity and adaptability adversaries demonstrate in the evolving cyberwarfare landscape.
Operation Texonto’s core disinformation strategy relies on emails expertly crafted to masquerade as official communications from Ukrainian ministries. These emails are designed to erode morale, exploiting themes like drug scarcity, heating disruptions, and food shortages – all of which mirror established Russian propaganda narratives. The psychological operation aims to sow doubt, fear, and resentment within the targeted population.
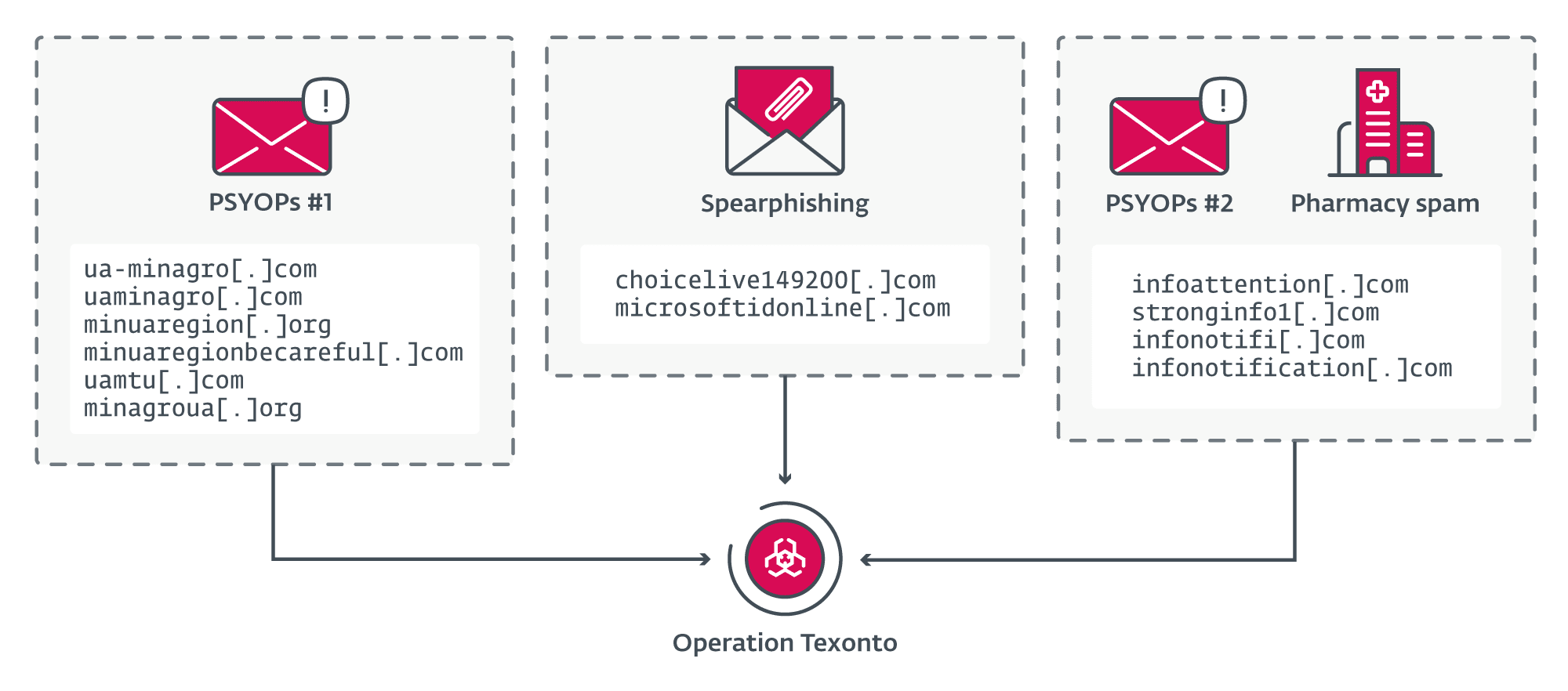
The campaign incorporates spearphishing attacks on critical organizations, like a Ukrainian defense company and an EU agency. These attacks utilize highly convincing Microsoft Office 365 credential theft pages, demonstrating the attackers’ ability to mimic trusted services to compromise sensitive accounts.
Strikingly, domains associated with Operation Texonto were found linked to potential influence operations aimed at Russian citizens. Specifically, these domains seem to have targeted critics of the government and supporters of deceased opposition leader, Alexei Navalny. This suggests the campaign operators may be pursuing a dual objective: demoralization of Ukraine while suppressing domestic dissent.
In an unexpected turn, email servers used in the PSYOP campaign were later repurposed for the distribution of large-scale “Canadian Pharmacy” spam. This practice has strong historical links to organized Russian cybercrime syndicates, hinting at a potential intersection between state-aligned influence operations and the financially motivated cyber-underworld.
Though conclusive attribution to a named group remains a challenge, ESET confidently assesses that Operation Texonto’s tactics, targeting, and messaging strongly suggest the operation is aligned with Russia’s objectives. The similarities to previous campaigns attributed to groups like ‘Callisto’ further underscore this link.
Operation Texonto’s adaptability and multifaceted nature present a heightened concern. The campaign’s ability to blend traditional espionage with disinformation, its potential to target both external and internal audiences, and its possible link to criminal elements exemplify the sophistication of modern information warfare.
Defensive Strategies and Outlook
Individuals and organizations must exercise increased skepticism around emails claiming to originate from official sources. Meticulous verification of sender details, close inspection of URLs, and heightened awareness of inconsistencies are essential.
Robust password management, strict adherence to update schedules, and the use of multi-factor authentication are vital safeguards against credential theft attempts.
Fear-mongering, inflammatory, or sensational content should be approached with a healthy dose of skepticism. Consider the source of the information, its potential objectives, and cross-reference facts.
Support Our Threat Intelligence
If you find our CVE report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee
