Understanding the Mirai Botnet

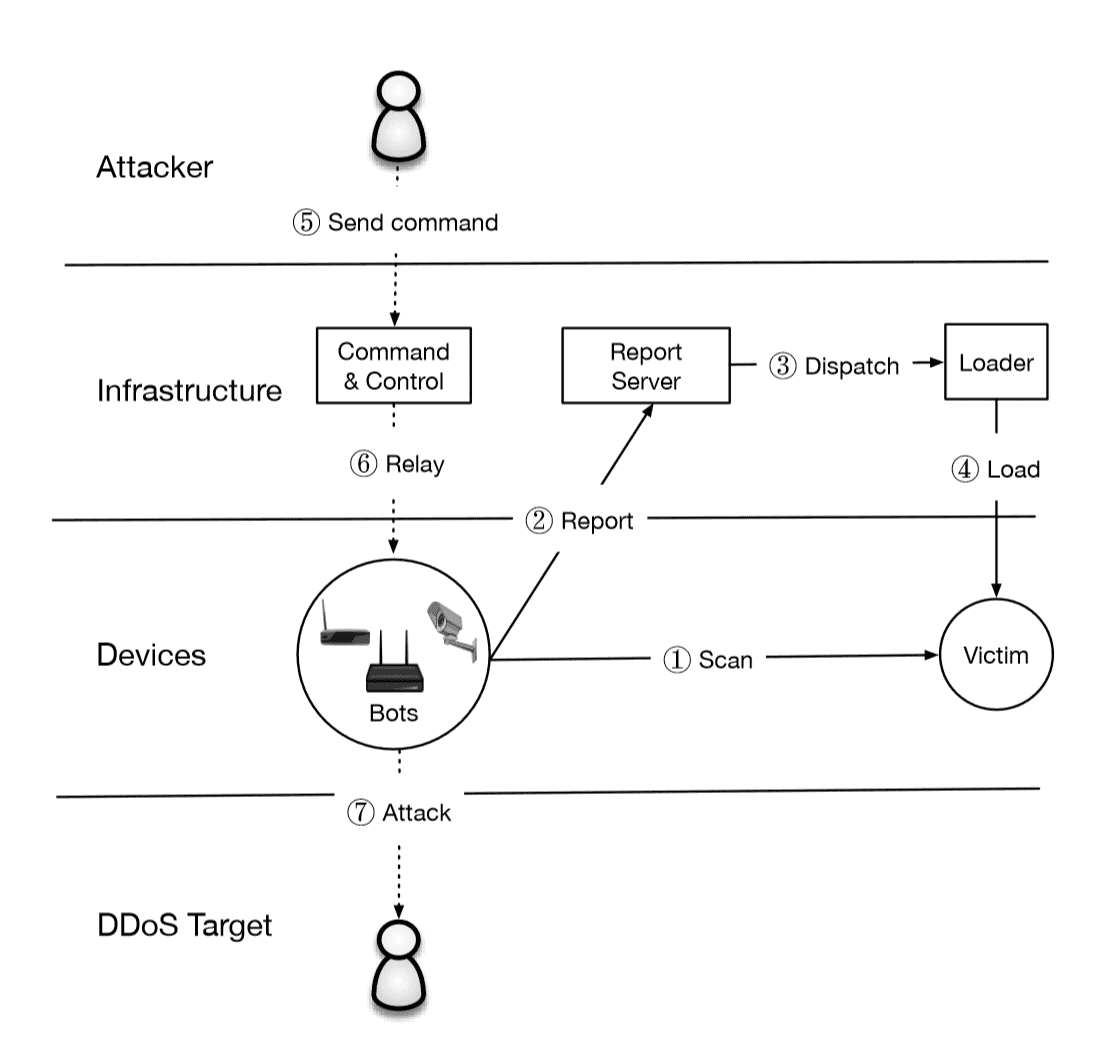
The Mirai botnet, composed primarily of embedded and IoT devices, took the Internet by storm in late 2016 when it overwhelmed several high-profile targets with massive distributed denial-of-service (DDoS) attacks. In this paper, we provide a seven-month retrospective analysis of Mirai’s growth to a peak of 600k infections and a history of its DDoS victims. By combining a variety of measurement perspectives, we analyze how the botnet emerged, what classes of devices were affected, and how Mirai variants evolved and competed for vulnerable hosts. Our measurements serve as a lens into the fragile ecosystem of IoT devices. We argue that Mirai may represent a sea change in the evolutionary development of botnets—the simplicity through which devices were infectedanditsprecipitousgrowth,demonstratethatnovice malicious techniques can compromise enough low-end devicestothreatenevensomeofthebest-defendedtargets. To address this risk, we recommend technical and nontechnicalinterventions, aswellasproposefutureresearch directions.