WiFiBroot
A WiFi-Pentest-Cracking tool for WPA/WPA2 (Handshake, PMKID, Offline Cracking, EAPOLS, Deauthentication Attack).
WiFiBroot is built to provide clients with an all-in-one facility for cracking WiFi (WPA/WPA2) networks. It heavily depends on scapy, a well-featured packet manipulation library in Python. Almost every process within is dependent somehow on scapy layers and other functions except for operating the wireless interface on a different channel. That will be done via native Linux command iwconfig for which you may be need sudo privileges. It currently provides four independent working modes to deal with the target networks. Two of them are online cracking methods while the other runs in offline mode. The offline mode is provided to crack saved hashes from the first two modes. One is for the deauthentication attack on the wireless network and can also be used as a jamming handler. It can be run on a variety of Linux platforms and at least requires WN727N from tp-link to properly operate.

Changelog v1.4
- Major Bugs Fixed.
- Ported Back to Python 2.
- Ported alongside Scapy
Installation
git clone https://github.com/hash3liZer/WiFiBroot.git
sudo pip install scapy
Use
WiFiBroot uses modes to identify which attack you want to perform on your target. Currently, there are three available modes. The usage of each mode can be seen by supplying the –help/-h option right after the -m/–mode option. Here’s a list of available modes and what they do:
Modes:
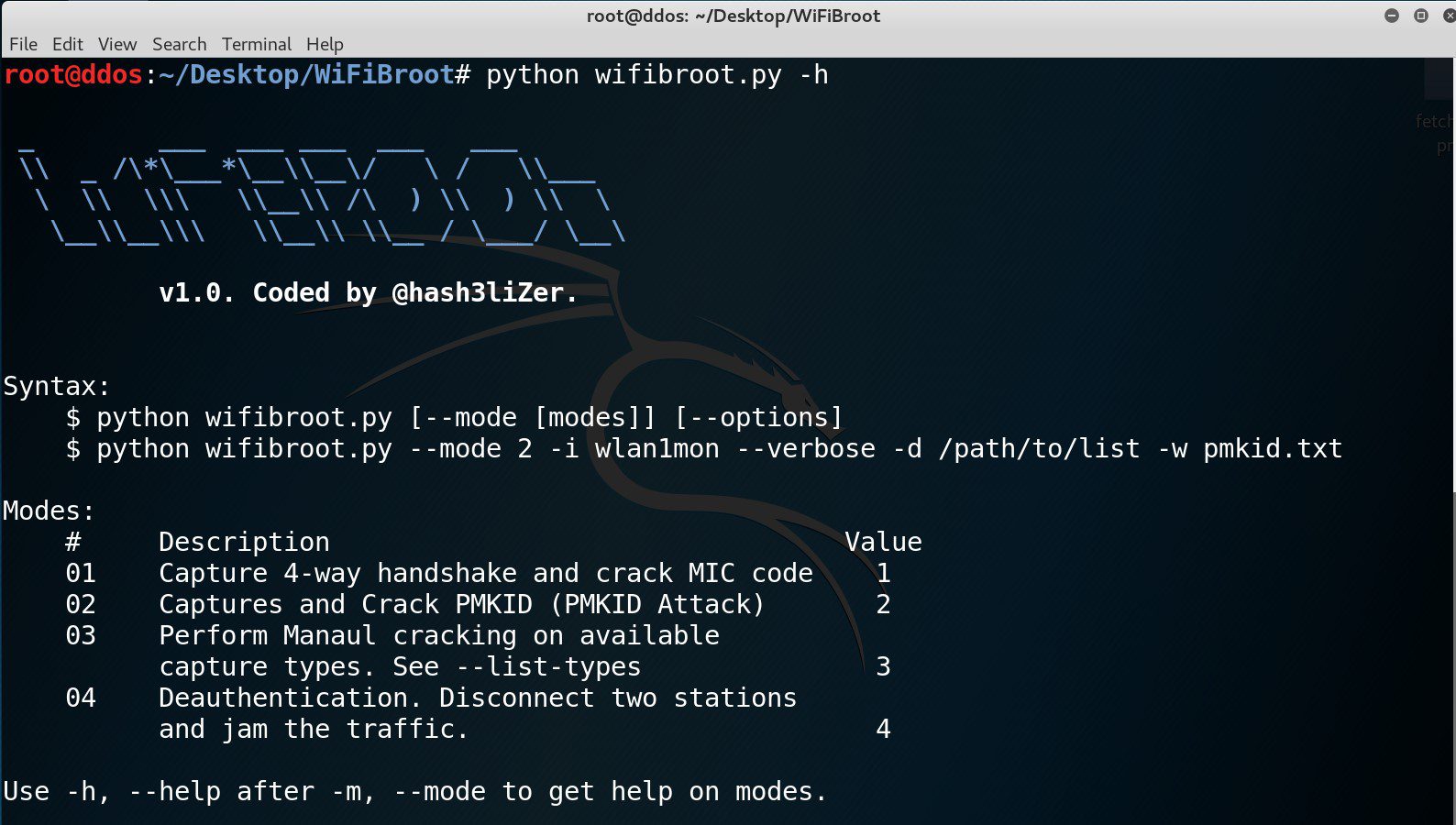
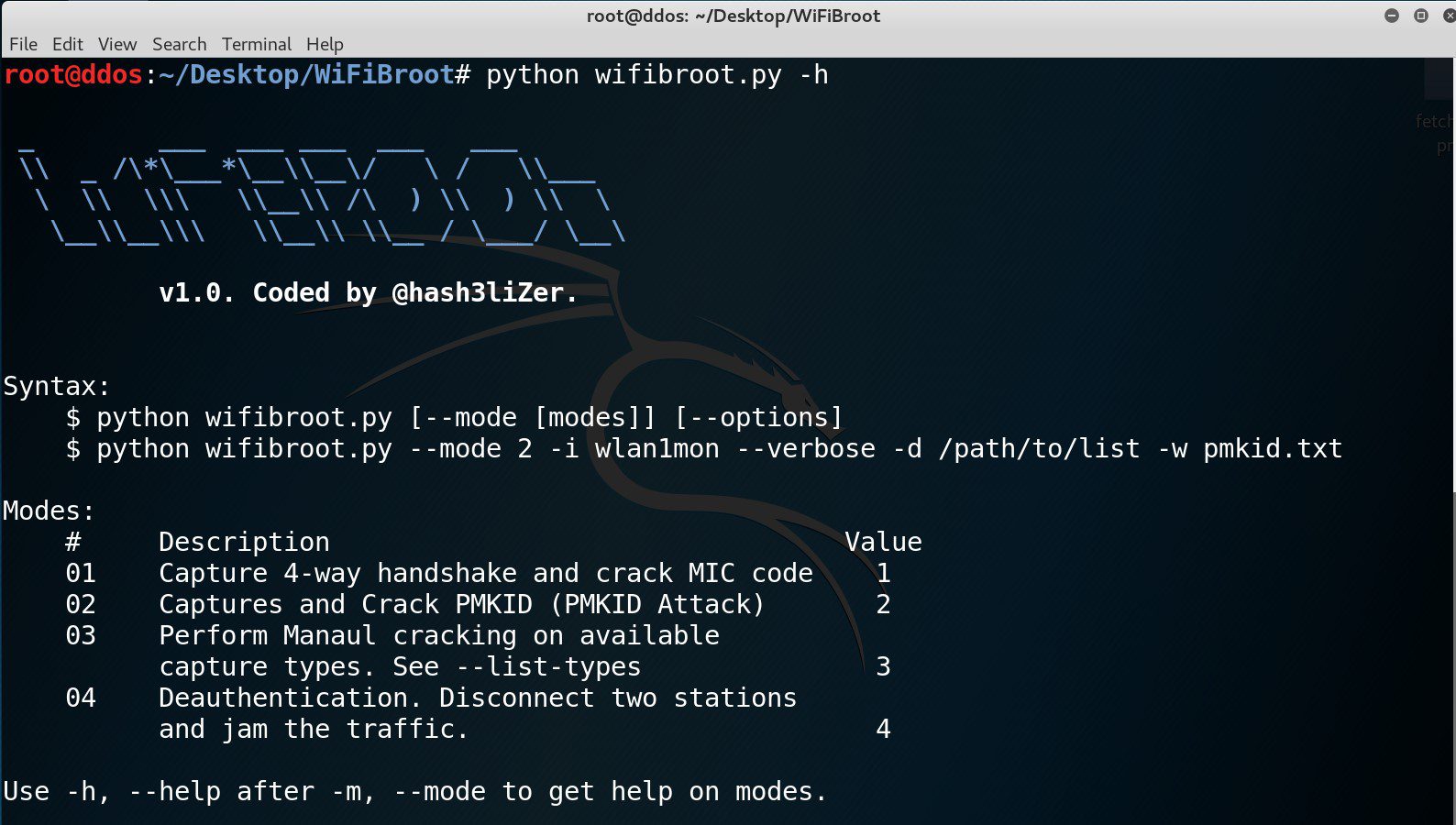
Syntax:
$ python wifibroot.py [--mode [modes]] [--options]
$ python wifibroot.py --mode 2 -i wlan1mon --verbose -d /path/to/list -w pmkid.txt
Modes:
# Description Value
01 Capture 4-way handshake and crack MIC code 1
02 Captures and Crack PMKID (PMKID Attack) 2
03 Perform Manaul cracking on available
capture types. See --list-types 3
04 Deauthentication. Disconnect two stations
and jam the traffic. 4
Use -h, --help after -m, --mode to get help on modes.
Each mode has a specific purpose and has it’s own options:
HANDSHAKE:
Mode:
01 Capture 4-way handshake and crack MIC code 1
Options:
Args Description Required
-h, --help Show this help manual NO
-i, --interface Monitor Interface to use YES
-v, --verbose Verbose Mode. Detail help NO
-t, --timeout Time Delay between two deauth
requests. NO
-d, --dictionary Dictionary for Cracking YES
-w, --write Write Captured handshake to
a seperate file NO
--deauth Number of Deauthentication
frames to send NO
Filters:
-e, --essid ESSID of listening network
-b, --bssid BSSID of target network.
-c, --channel Channel interface should be listening
on. Default: ALL
PMKID ATTACK
Mode:
02 Captures and Crack PMKID (PMKID Attack) 1
Options:
Args Description Required
-h, --help Show this help manual NO
-i, --interface Monitor Interface to use YES
-v, --verbose Verbose Mode. Detail help NO
-d, --dictionary Dictionary for Cracking YES
-w, --write Write Captured handshake to
a seperate file NO
Filters:
-e, --essid ESSID of listening network
-b, --bssid BSSID of target network.
-c, --channel Channel interface should be listening
on. Default: ALL
Offline Cracking
Mode:
03 Perform Manaul cracking on available capture
types. See --list-types 3
Options:
Args Description Required
-h, --help Show this help manual NO
--list-types List available cracking types NO
--type Type of capture to crack YES
-v, --verbose Verbose Mode. Detail help NO
-d, --dictionary Dictionary for Cracking YES
-e, --essid ESSID of target network.
Only for HANDSHAKE Type YES
-r, --read Captured file to crack YES
DEAUTHENTICATION ATTACK (Stress Testing)
Mode:
04 Deauthentication. Disconnect two stations
and jam the traffic. 4
Options:
Args Description Required
-h, --help Show this help manual NO
-i, --interface Monitor Mode Interface to use YES
-0, --count Number of Deauthentication
frames to send. '0' specifies
unlimited frames YES
--ap Access Point MAC Address NO
--client STA (Station) MAC Address NO
Copyright (C) 2018 hash3liZer