Adaz: Active Directory Hunting Lab in Azure
Adaz: Active Directory Hunting Lab in Azure
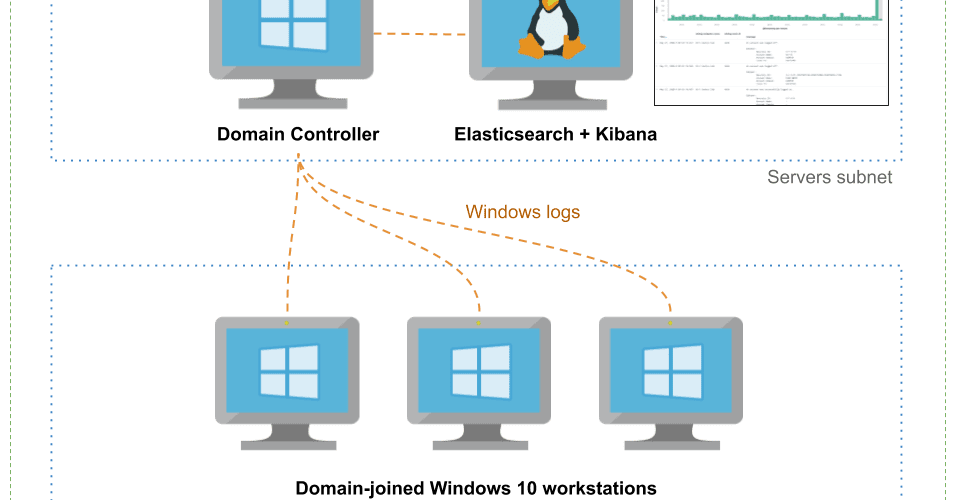
This project allows you to easily spin up Active Directory labs in Azure with domain-joined workstations, Windows Event Forwarding, Kibana, and Sysmon using Terraform/Ansible.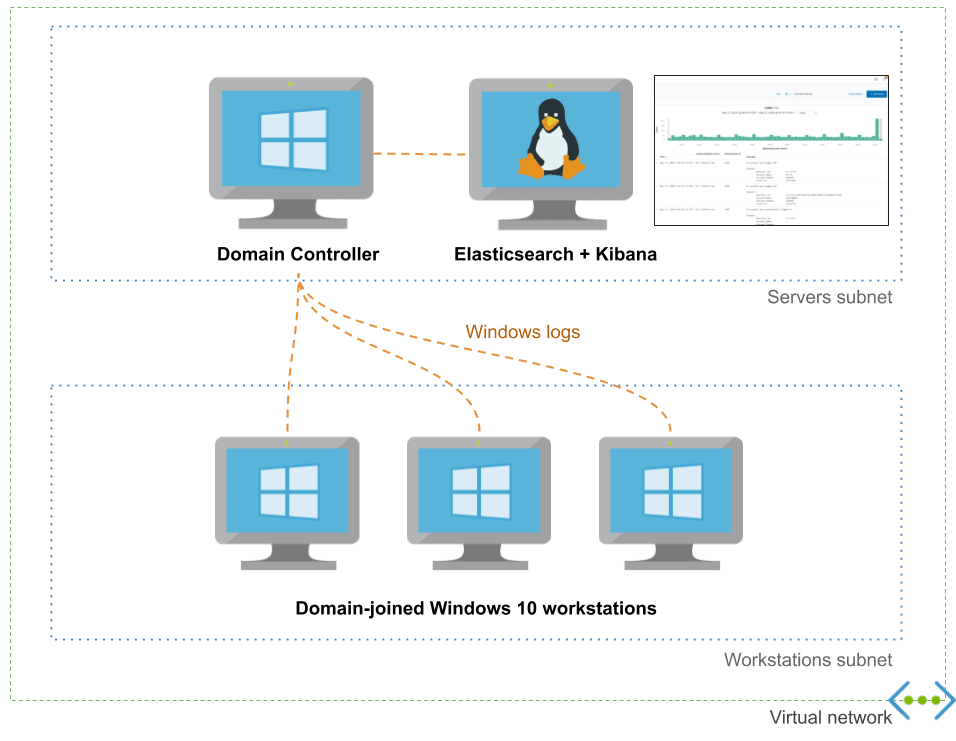
It exposes a high-level configuration file for your domain to allow you to customize users, groups, and workstations.
Features
- Windows Event Forwarding pre-configured
- Audit policies pre-configured
- Sysmon installed
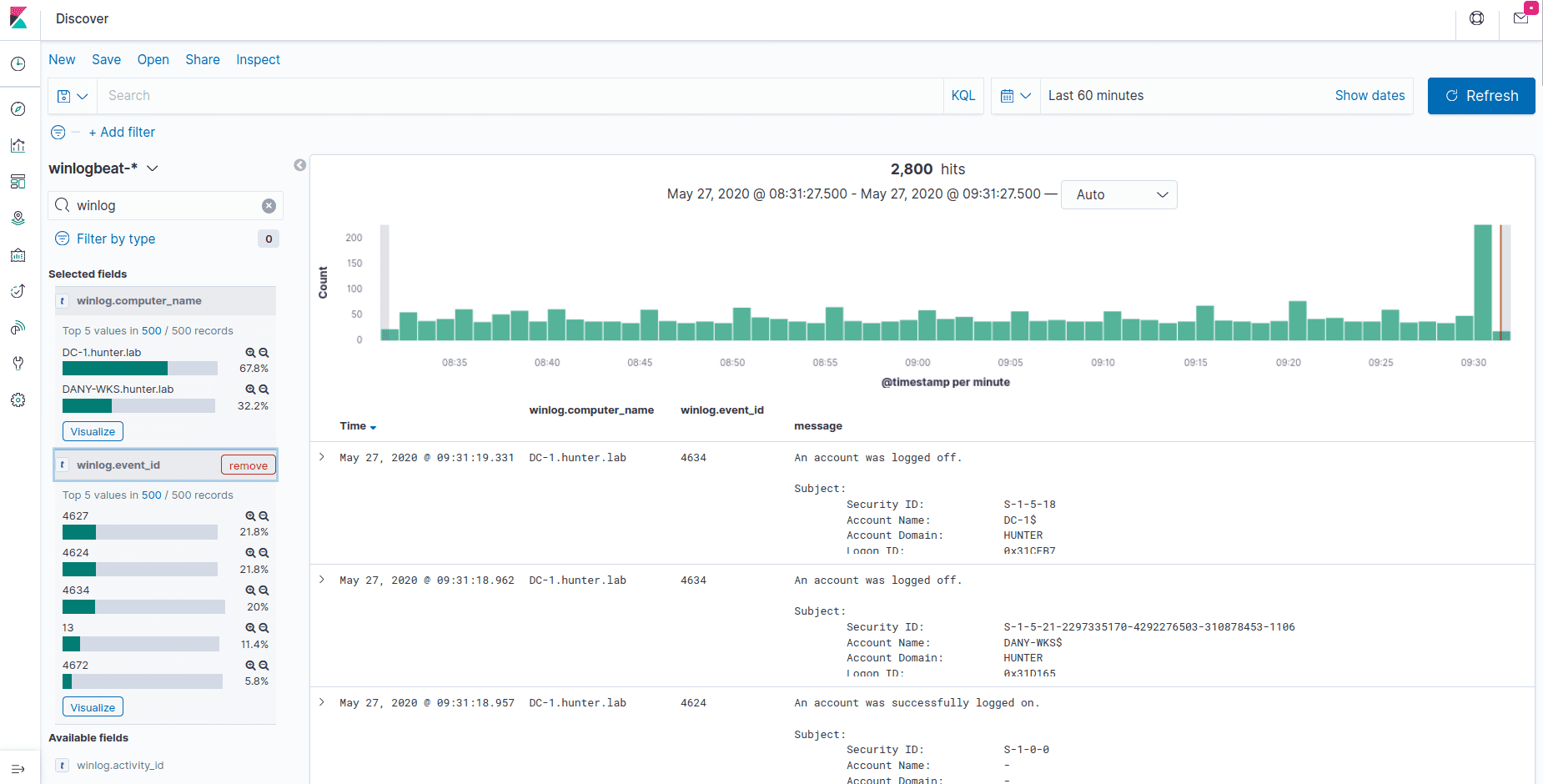
- Logs centralized in an Elasticsearch instance which can easily be queried from the Kibana UI
- Domain easily configurable via YAML configuration file
Here’s an incomplete and biased comparison with DetectionLab:
| Adaz | DetectionLab | |
|---|---|---|
| Public cloud support | Azure | AWS |
| Expected time to spin up a lab | 15-20 minutes | 25 minutes |
| Log management & querying | Elasticsearch+Kibana | Splunk Enterprise |
| WEF | ✔️ | ✔️ |
| Audit policies | ✔️ | ✔️ |
| Sysmon | ✔️ | ✔️ |
| YAML domain configuration file | ✔️ | 🚫 |
| Multiple Windows 10 workstations support | ✔️ | 🚫 |
| VirtualBox/VMWare support | 🚫 | ✔️ |
| osquery / fleet | 🚫(vote!) | ✔️ |
| Powershell transcript logging | 🚫 (vote!) | ✔️ |
| IDS logs | 🚫 (vote!) | ✔️ |
Use-cases
- Detection engineering: Having access to clean lab with a standard is a great way to understand what traces common attacks and lateral movement techniques leave behind.
- Learning Active Directory: I often have the need to test GPOs or various AD features (AppLocker, LAPS…). Having a disposable lab is a must for this.