AMSITrigger: The Hunt for Malicious Strings

AMSITrigger
AMSITrigger will identify all of the malicious strings in a powershell file, by repeatedly making calls to AMSI using AMSIScanBuffer, line by line. On receiving an AMSI_RESULT_DETECTED response code, the line will then be scrutinised to identify the individual triggers.
In order to speed up the scanning process, AMSITrigger breaks a file up into smaller chunks. Being able to ignore whole chunks, reduces calls to AMSIScanBuffer but presents a few problems that can result in false-negatives ie. A clean result where you expected a trigger.
The first problem is where the signature length exceeds the chunk size. To cater for this I’ve included a ChunkSize parameter, which should be increased if you’re getting an unexpected result.
The second problem is where a signature spans 2 consecutive chunks, which is more likely when you use smaller chunk sizes. To cater for this, I’ve added a maxSignatureLength parameter. This will assume that the final maxSignatureLength bytes in a chunk could be the start of a truncated signature, and will prepend the next chunk with those bytes.
Use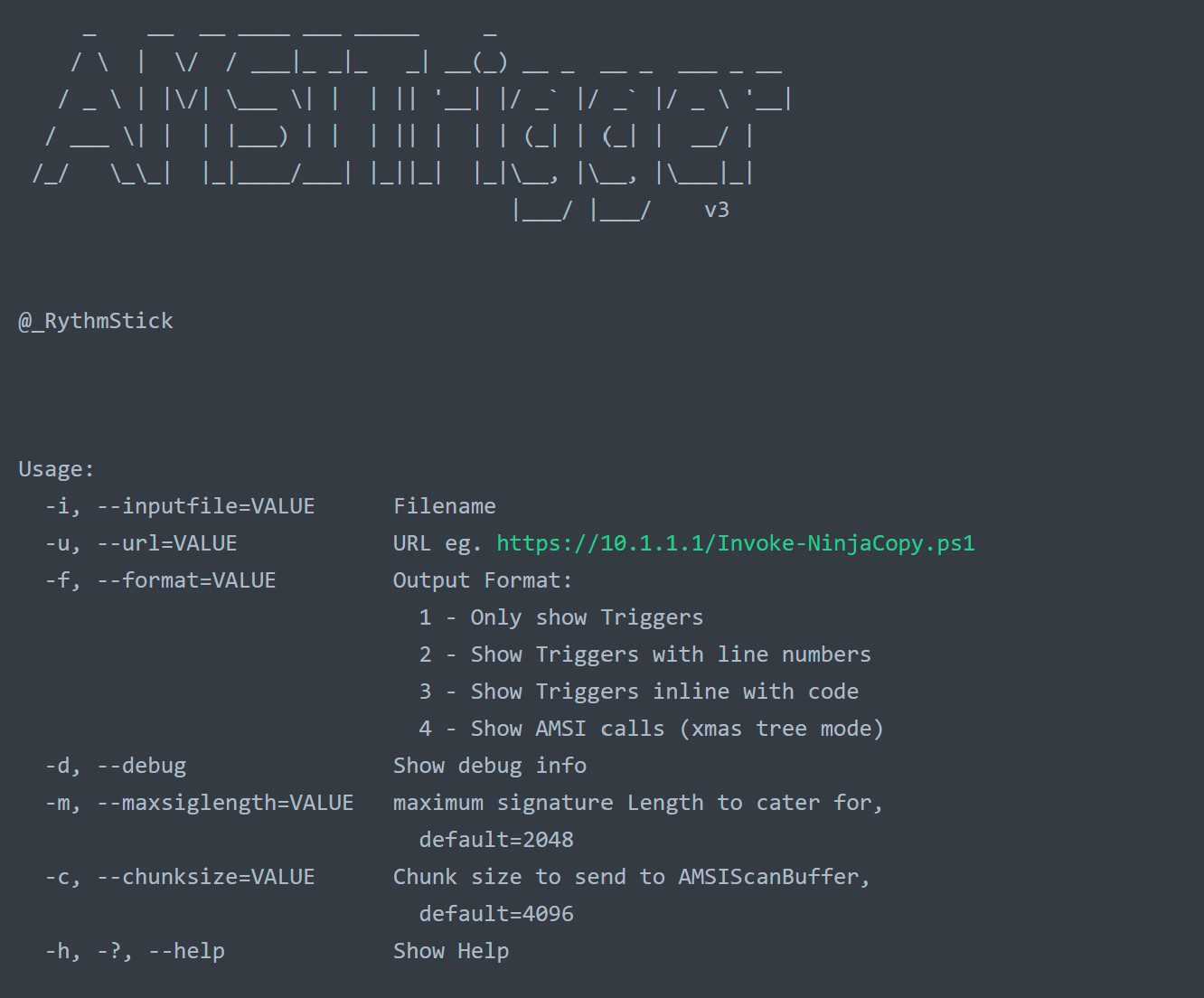
Download
Copyright (C) 2020 RythmStick






