Android-PIN-Bruteforce: bruteforcing the lockscreen PIN
Android-PIN-Bruteforce
Unlock an Android phone (or device) by bruteforcing the lockscreen PIN.
Turn your Kali Nethunter phone into a bruteforce PIN cracker for Android devices!
How it works
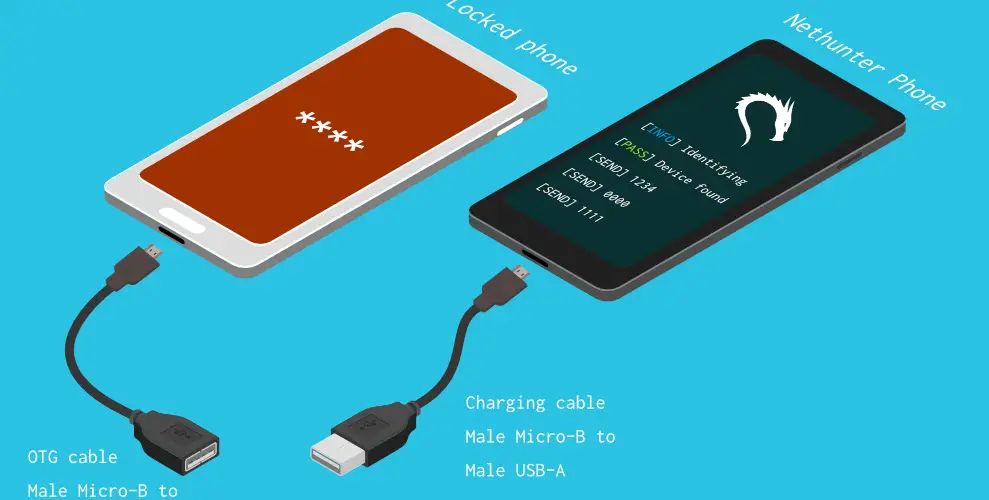
It uses a USB OTG cable to connect the locked phone to the Nethunter device. It emulates a keyboard, automatically tries PINs and waits after trying too many wrong guesses.

[Nethunter phone] <–> [USB cable] <–> [USB OTG adaptor] <–> [Locked Android phone]
The USB HID Gadget driver provides emulation of USB Human Interface Devices (HID). This enables an Android Nethunter device to emulate keyboard input to the locked phone. It’s just like plugging a keyboard into a locked phone and pressing keys.
⏱ This takes just over 16.6 hours with a Samsung S5 to try all possible 4-digit PINs, but with the optimised PIN list it should take you much less time.
You will need
- A locked Android phone
- A Nethunter phone (or any rooted Android with HID kernel support)
- USB OTG (On The Go) cable/adapter (USB male Micro-B to female USB A), and a standard charging cable (USB male Micro-B to male A).
- That’s all!
🌟 Benefits
- Turn your NetHunter phone into an Android PIN-cracking machine
- Unlike other methods, you do not need ADB or USB debugging enabled on the locked phone
- The locked Android phone does not need to be rooted
- You don’t need to buy special hardware, e.g. Rubber Ducky, Teensy, Cellebrite, XPIN Clip, etc.
- You can easily modify the backoff time to crack other types of devices
- It works!
⭐ Features
- Crack PINs of any length from 1 to 10 digits
- Use config files to support different phones
- Optimised PIN lists for 3,4,5, and 6-digit PINs
- Bypasses phone pop-ups including the Low Power warning
- Detects when the phone is unplugged or powered off, and waits while retrying every 5 seconds
- Configurable delays of N seconds after every X PIN attempts
- Log file






