androwarn v1.6 releases: static code analyzer for malicious Android applications

Androwarn
Androwarn is a tool whose main aim is to detect and warn the user about potential malicious behaviors developed by an Android application.
The detection is performed with the static analysis of the application’s Dalvik bytecode, represented as Smali, with the androguard library.
This analysis leads to the generation of a report, according to a technical detail level chosen from the user.
Features
- Structural and data flow analysis of the bytecode targeting different malicious behaviours categories
- Telephony identifiers exfiltration: IMEI, IMSI, MCC, MNC, LAC, CID, operator’s name…
- Device settings exfiltration: software version, usage statistics, system settings, logs…
- Geolocation information leakage: GPS/WiFi geolocation…
- Connection interfaces information exfiltration: WiFi credentials, Bluetooth MAC adress…
- Telephony services abuse: premium SMS sending, phone call composition…
- Audio/video flow interception: call recording, video capture…
- Remote connection establishment: socket open call, Bluetooth pairing, APN settings edit…
- PIM data leakage: contacts, calendar, SMS, mails…
- External memory operations: file access on SD card…
- PIM data modification: add/delete contacts, calendar events…
- Arbitrary code execution: native code using JNI, UNIX command, privilege escalation…
- Denial of Service: event notification deactivation, file deletion, process killing, virtual keyboard disable, terminal shutdown/reboot…
- Report generation according to several detail levels
- Essential (-v 1) for newbies
- Advanced (-v 2)
- Expert (-v 3)
- Report generation according to several formats
- Plaintext txt
- Formatted html from a Bootstrap template
Changelog v1.6
- 2019/05/30: Python 3 support and few fixes
Install
pip install androwarn
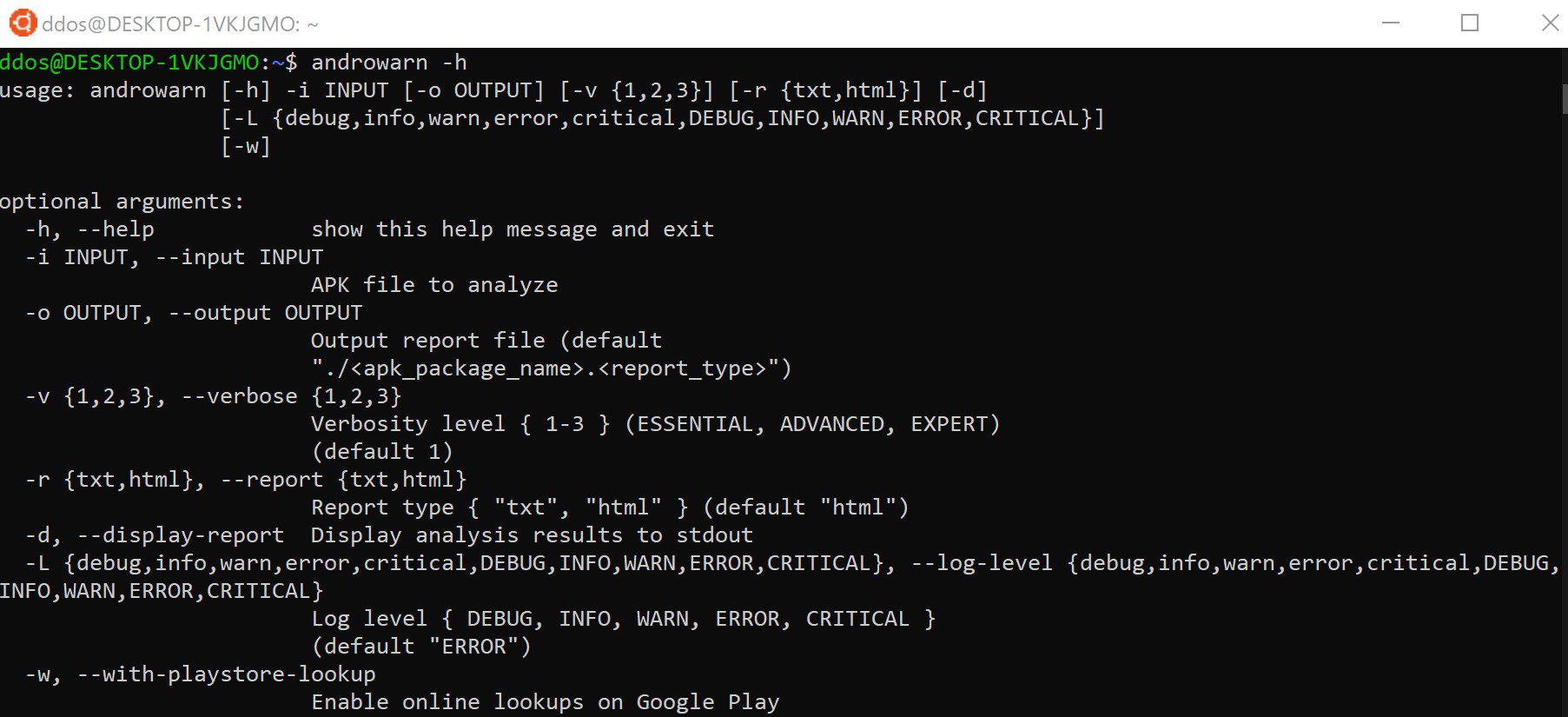
Usage
Copyright (C) 2018 maaaaz
Source: https://github.com/maaaaz/






