Apache Pulsar Patches Authorization Flaw (CVE-2024-29834) – Update Now to Protect Sensitive Data
Apache Pulsar, a highly popular open-source messaging and streaming platform, has recently patched a critical security vulnerability that could leave your organization’s data exposed. The flaw, tracked as CVE-2024-29834, enables unauthorized users to make changes to sensitive data streams and system access rules.

What is Apache Pulsar?
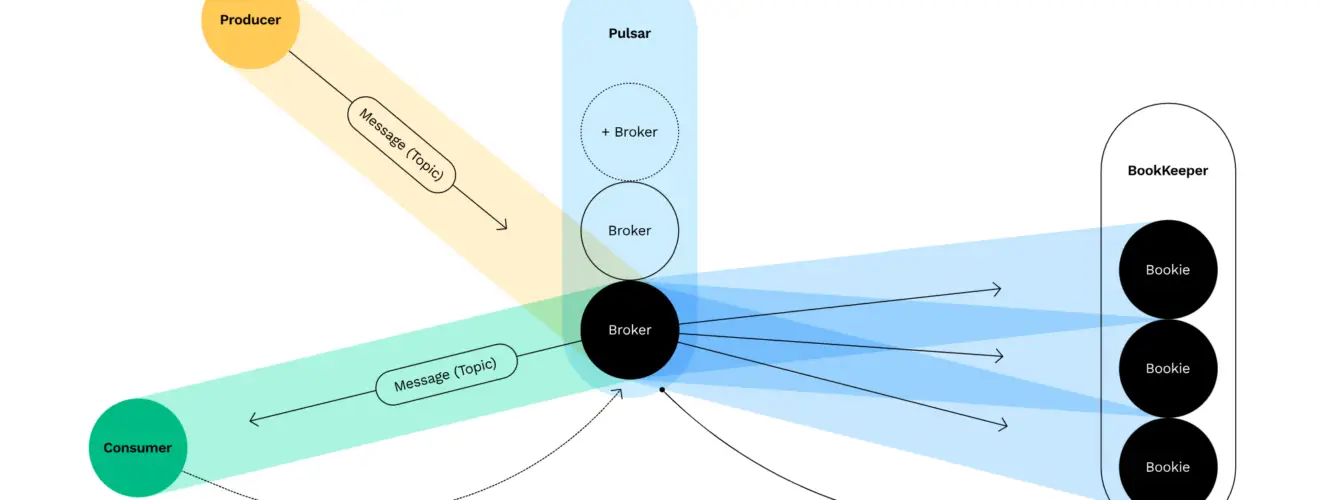
Before we dive into the specifics of the vulnerability, let’s understand Apache Pulsar. Pulsar is a widely adopted platform for managing real-time data flows. It boasts features like:
- Scalability: Handles millions of messages across multiple servers with ease.
- Low latency: Delivers messages to consumers within milliseconds.
- Geo-replication: Synchronizes data between different regions for reliability.
- Versatility: Supports multiple programming languages for seamless integration.
Companies trust Pulsar to handle sensitive information, making this vulnerability a significant concern.
The Vulnerability Explained
CVE-2024-29834 is an improper authorization issue. In essence, it allows users with basic permissions (intended for sending or receiving messages) to perform actions that should be reserved for system administrators. These unauthorized actions include:
- Changing data access rules
- Modifying data storage policies
- Manipulating data subscriptions
The Impact
A malicious actor exploiting this vulnerability could:
- Steal or alter sensitive data within Pulsar streams.
- Disrupt critical business operations by modifying data pipelines.
- Gain unauthorized access to broader systems connected to Pulsar.
Who’s Affected?
If your organization uses Apache Pulsar versions 2.7.1 to 2.10.6, 2.11.0 to 2.11.4, 3.0.0 to 3.0.3, 3.1.0 to 3.1.3, or 3.2.0 to 3.2.1, you are vulnerable.
The Fix
The Apache Pulsar team has swiftly released patches to address this vulnerability. Immediate action is highly recommended:
- 3.0 users: Upgrade to at least version 3.0.4
- 3.1 & 3.2 users: Upgrade to at least version 3.2.2
If you run versions older than 3.0, it’s strongly advised to upgrade to one of the patched releases. You can find more information about the patches on the Apache Pulsar website.
Protect Your Data
Staying on top of security updates is vital, especially for software handling critical data flows. Regularly review security advisories and patch your systems promptly. Consider setting up automated patch management systems for increased protection.






