Pulsar: network fuzzer with automatic protocol learning

PULSAR
Protocol Learning, Simulation, and Stateful Fuzzer
Pulsar is a network fuzzer with automatic protocol learning and simulation capabilities. The tool allows modeling a protocol through machine learning techniques, such as clustering and hidden Markov models. These models can be used to simulate communication between Pulsar and a real client or server thanks to semantically correct messages which, in combination with a series of fuzzing primitives, allow to test the implementation of an unknown protocol for errors in deeper states of its protocol state machine.
For detailed information about the method implemented by Pulsar, you can read the following publications:
Pulsar: Stateful Black-Box Fuzzing of Proprietary Network Protocols
Hugo Gascon, Christian Wressnegger, Fabian Yamaguchi, Daniel Arp and Konrad Rieck
Proc. of 11th EAI International Conference on Security and Privacy in Communication Networks (SECURECOMM) October 2015
Learning Stateful Models for Network Honeypots
Tammo Krueger, Hugo Gascon, Nicole Krämer and Konrad Rieck
ACM Workshop on Security and Artificial Intelligence (AISEC) October 2012
Download
git clone https://github.com/hgascon/pulsar.git
Configuration
The directory pulsar/conf contains a series of configuration files that define the parameters required for certain operations in each one of the Pulsar methods for automatic learning, simulation, and fuzzing.
Use
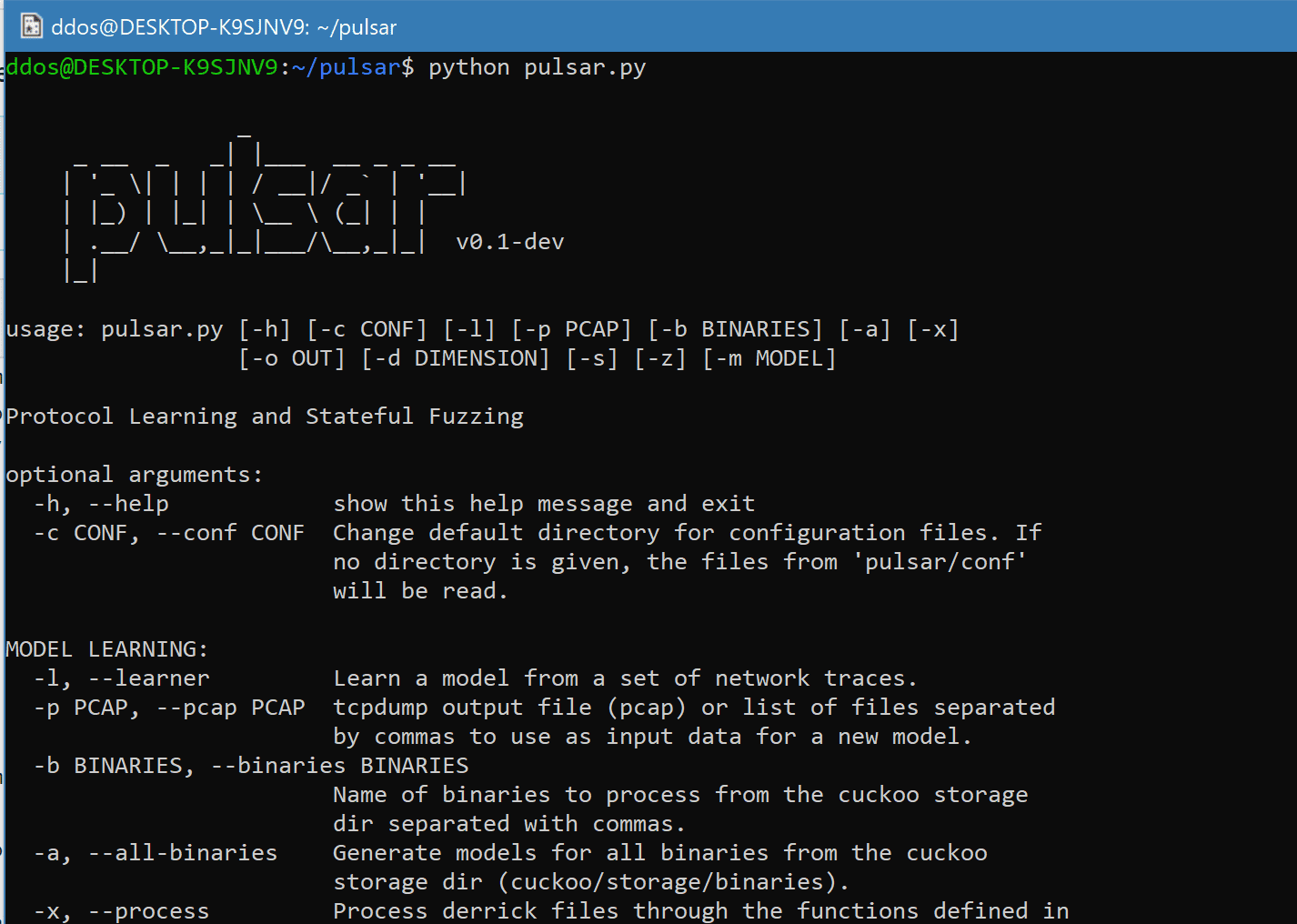
Examples
Generate the model of a communication channel from individual PCAP files or the recorded traces of one or more binaries run by cuckoo sandbox:
Simulate a communication channel based on a learned model:
Initiate a fuzzing session against a target given the model of its communication channel:
Copyright (c) 2014, Hugo Gascon
Source: https://github.com/hgascon/






