boko: Application Hijack Scanner for macOS
boko Application Hijack Scanner for macOS
boko.py is an application scanner for macOS that searches for and identifies potential dylib hijacking and weak dylib vulnerabilities for application executables, as well as scripts and application, may use that have the potential to be backdoored. The tool also calls out interesting files and lists them instead of manually browsing the file system for analysis. With the active discovery function, there’s no more guesswork if an executable is vulnerable to dylib hijacking!
The reason behind creating this tool was because I wanted more control over the data Dylib Hijack Scanner discovered. Most publicly available scanners stop once they discover the first case of a vulnerable dylib without expanding the rest of the rpaths. Since sometimes the first result is expanded in a non-existent file within a SIP-protected area, I wanted to get the rest of those expanded paths. Because of this, there are false positives, so the tool assigns a certainty field for each item.
| Certainty | Description |
|---|---|
| Definite | The vulnerability is 100% exploitable |
| High | If the vulnerability is related to a main executable and rpath is 2nd in the load order, there is a good chance the vulnerability is exploitable |
| Potential | This is assigned to dylibs and backdoorable scripts, worth looking into but may not be exploitable |
| Low | Low chance this is exploitable because of late load order, but knowledge is power |
Process Flow:
Passive mode:
Running:
- Identify all running processes on a system
- Obtain full path of running executable
- Read executables and identify macho headers
- Identify dylib relative paths that are loaded and check if files exist in that location
- Output hijackable dylibs and weak dylibs for running applications
Installed/Application:
- Scan full directory of application for all files
- Identify executable files, scripts, and other interesting files in the application directory
- Read executables and identify macho headers or if the file is a script
- Identify dylib relative paths that are loaded and check if files exist in that location
- Output hijackable dylibs, weak dylibs, backdoorable scripts, and interesting files (verbose only)
Active mode:
Running:
- Identify all running processes on a system
- Obtain full path of running executable
- Read executables and identify macho headers
- Execute the executable binaries for 3 seconds and analyze rpaths that are attempted to load
- Output hijackable dylibs and weak dylibs for running applications
Application:
- Scan full directory of application for all files
- Identify executable files, scripts, and other interesting files in the application directory
- Read executables and identify macho headers or if the file is a script
- Execute the executable binaries for 3 seconds and analyze rpaths that are attempted to load
- Output hijackable dylibs, weak dylibs, backdoorable scripts, and interesting files (verbose only)
Download
git clone https://github.com/bashexplode/boko.git
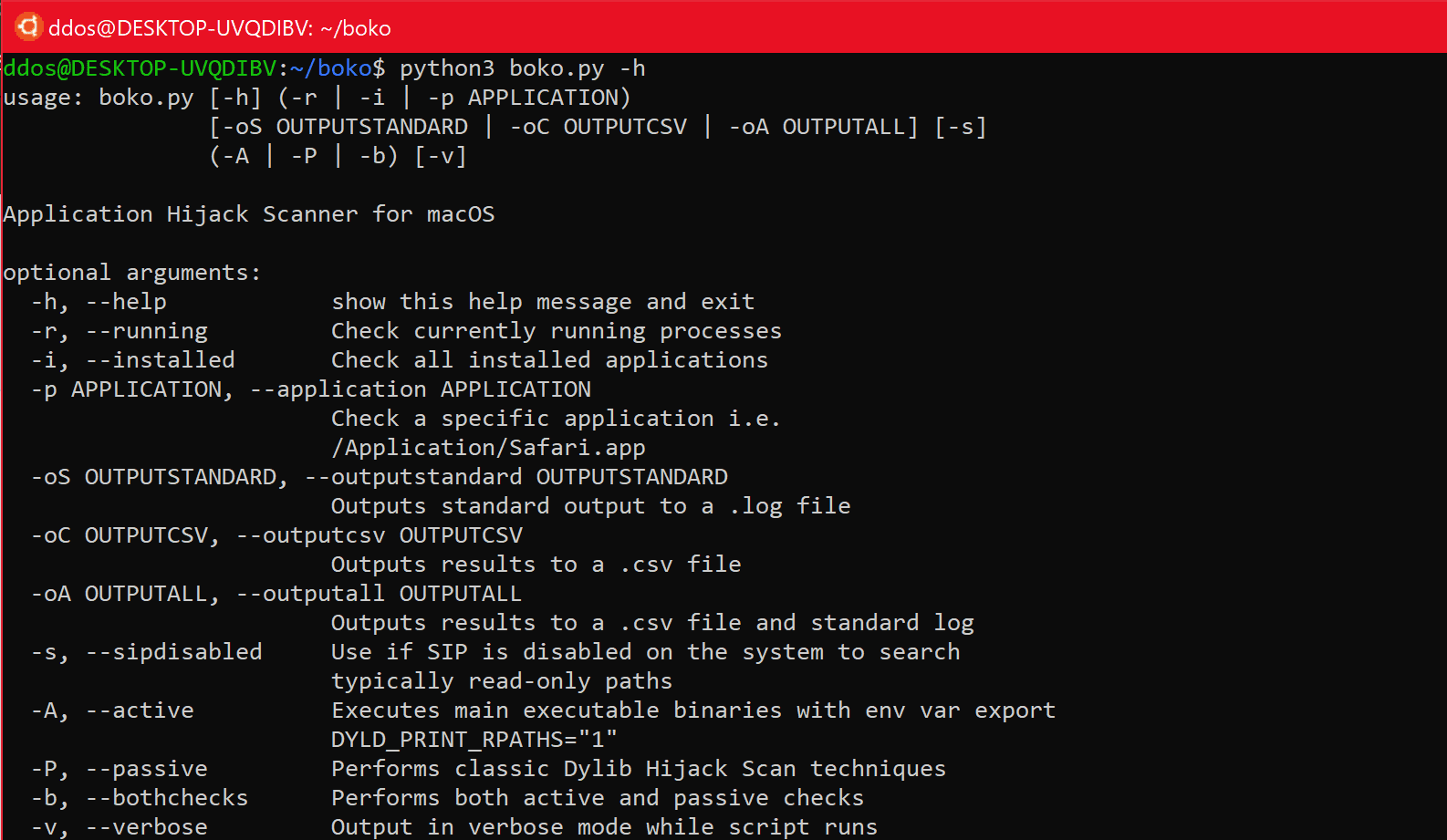
Use
Copyright (c) 2020, Jesse Nebling
All rights reserved.
Source: https://github.com/bashexplode/