armory: take in a lot of external and discovery data from a lot of tools
Armory is a tool meant to take in a lot of external and discovery data from a lot of tools, add it to a database and correlate all of the related information. It isn’t meant to replace any specific tool. It is meant to take the output from various tools, and use it to feed other tools.
Install
git clone https://github.com/depthsecurity/armory.git
python setup.py install
Next, edit settings.ini and modify the base_path option. This should point to the root path you are using for your current project. You should change this with every project, so you will always be using a clean database. All files generated by modules will be created here, as well as the sqlite3 database. By default, it will be within the current directory-.
Use
Modules
Modules run tools, ingest output, and write it to the database. To see a list of available modules, type:
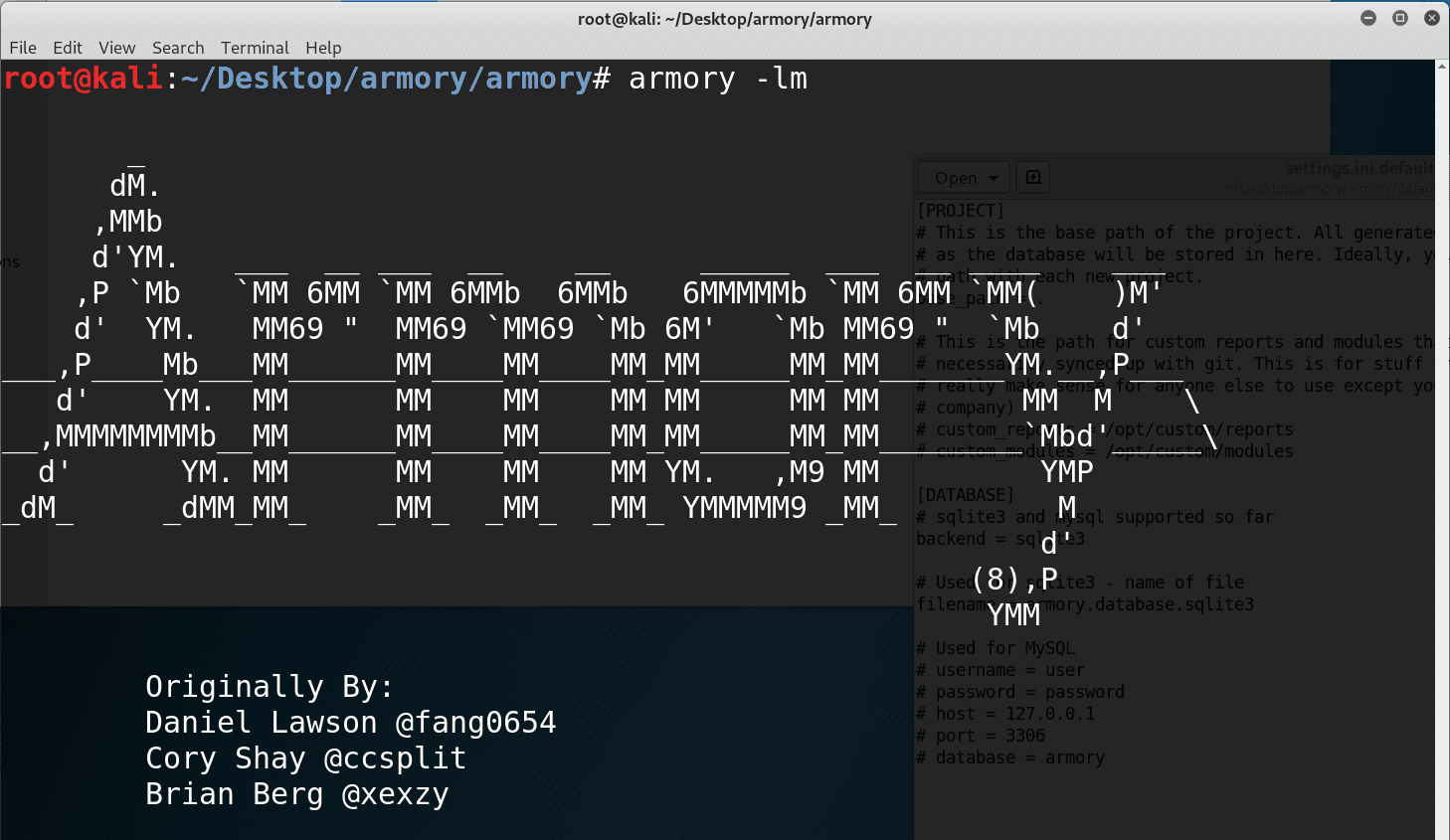
armory -lmAvailable modules:
DNSRecon
Fierce
GobusterDNS
GobusterDir
Gowitness
HeaderScanner
Hydra
Ingestor
LinkedInt
Nessus
Nmap
NmapCertScan
PowerMeta
SSLScan
SampleModule
SampleToolModule
Sublist3r
TheHarvester
Tko-subs
URLScanner
Whois
To see a list of module options, type:
armory -m <module> -M
Reports
Reports are similar to modules, except they are meant to pull data from the database and display it in a usable format. To view all of the available reports:
armory -lr
To view available report options:
armory -r <report> -R
Interactive Shell
There is also an interactive shell which uses IPython as the base and will allow you to run commands or change database values. It can be launched with armory-shell. By default, the following will be available: Domain, BaseDomains, IPAddresses, CIDRs, Users, Creds, Vulns, Ports, Urls, ScopeCIDRs.
Copyright (C) 2018




