assless-chaps: Crack MSCHAPv2 challenge/responses quickly
assless-chaps
Crack MSCHAPv2/NTLMv1 challenge/responses quickly using a database of NT hashes
Introduction
Assless CHAPs is an efficient way to recover the NT hash used in an MSCHAPv2/NTLMv1 exchange if you have the challenge and response (e.g. from a WiFi EAP WPE attack).
It requires a database of NT hashes, instructions on how to make these from existing lists or using hashcat with wordlists and rules are available below. I’ve included a sample database from SecLists. You’ll need to unzip it.
Technique
An MSCHAPv2 exchange does not require the clear-text password to be “cracked”, rather we merely need the NThash used.
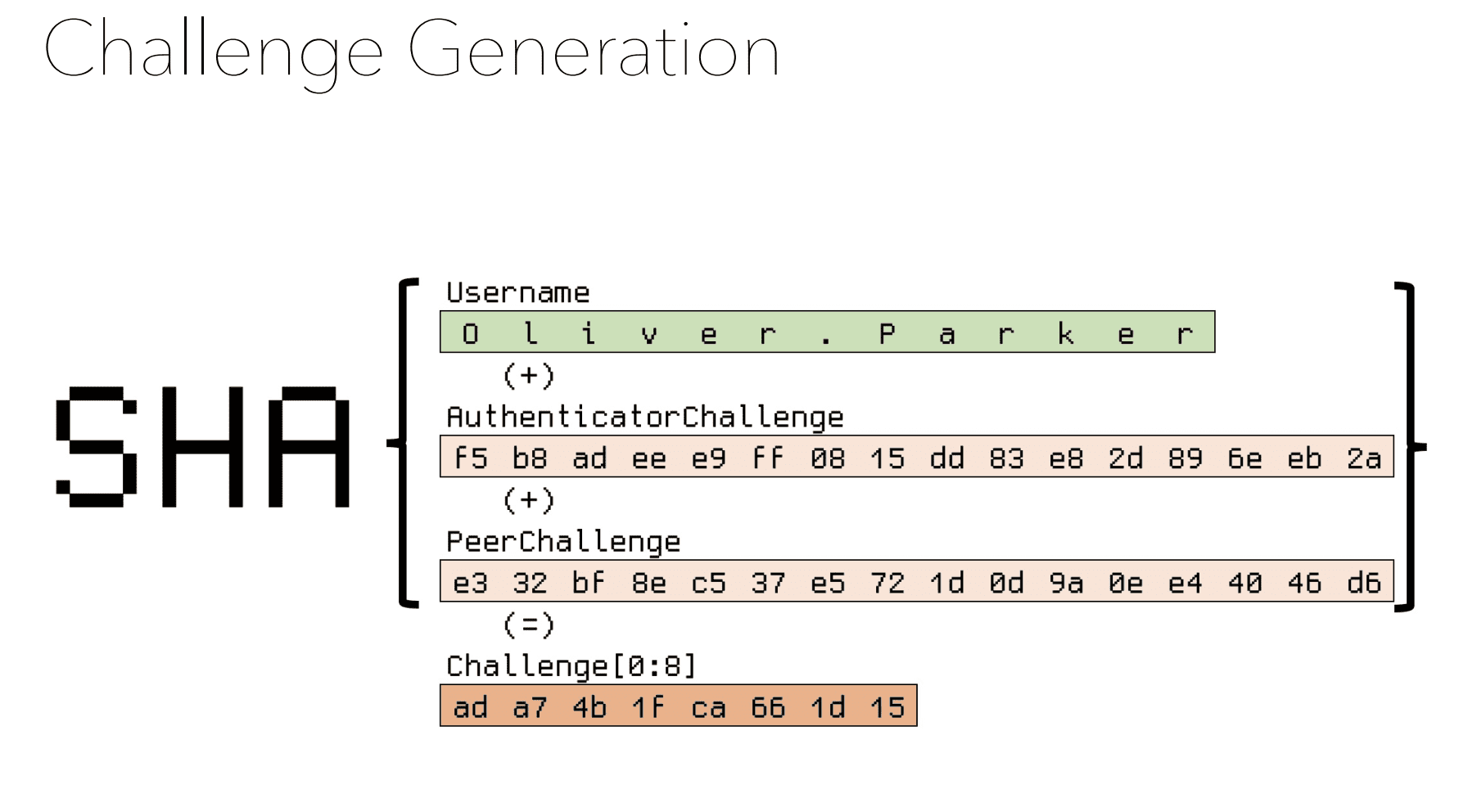
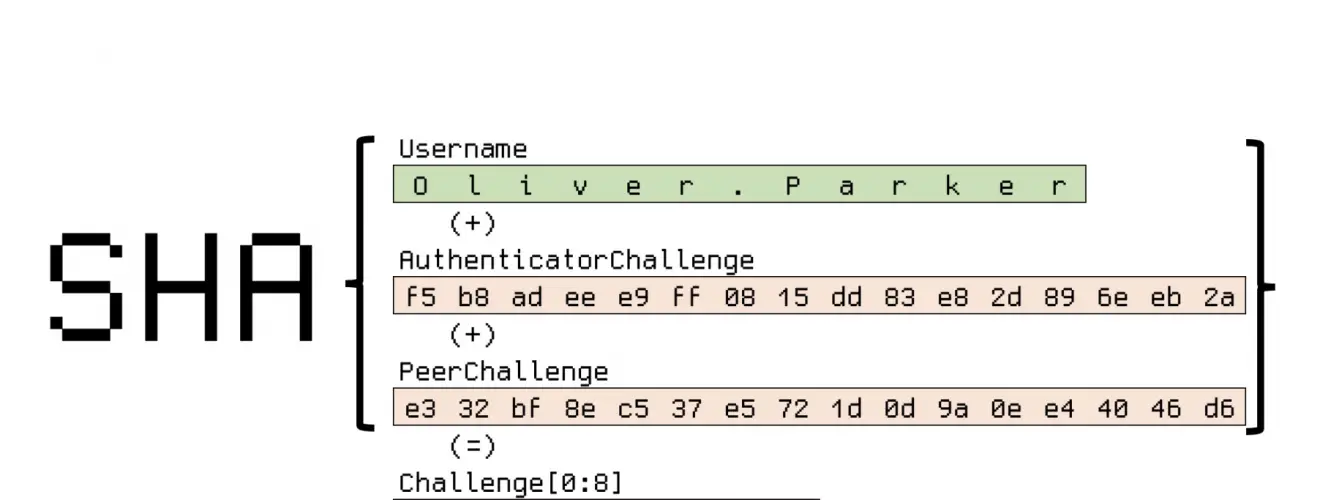
MSCHAPv2 splits the NThash into three parts and uses each part as different keys to DES encrypt the same challenge (derived from the peer and authenticator challenges). The NTHash is split into two 7-byte keys and one 2-byte key. This means the last key is padded with NULLs to make a key of the required length. This can be rapidly brute-forced due to the efficiency of DES operation and a keyspace of 65 535. Once we have those two bytes, we can look up all NThashes in our database, that end in those two bytes. This provides a much smaller set of possible hashes to check.
This is a form of space vs time tradeoff, similar to a rainbow table. It’s also a form of hash shucking.