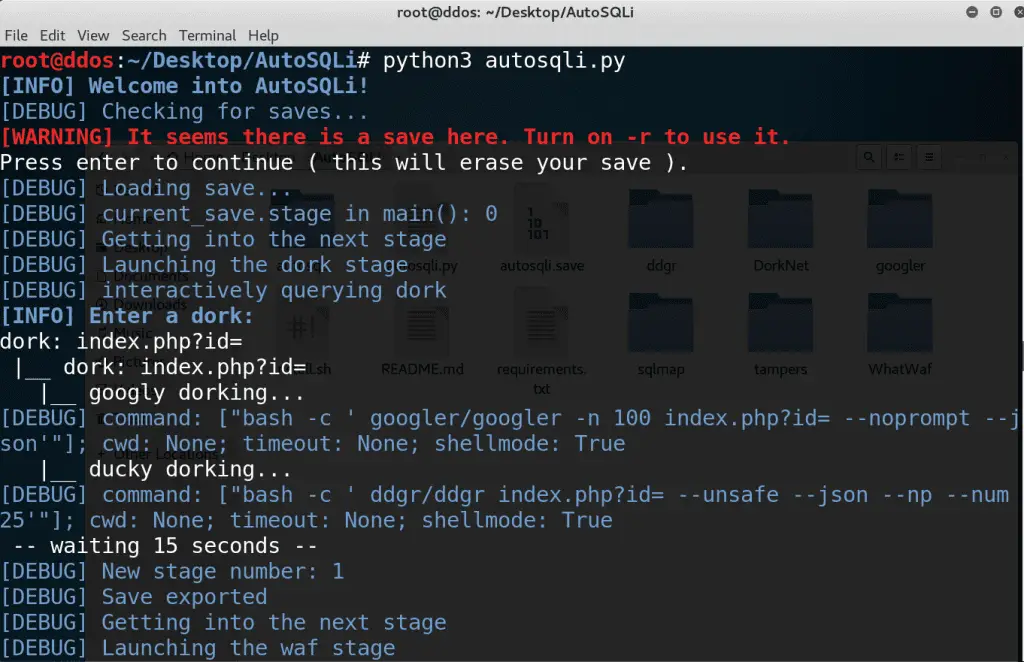
AutoSQLi: automatic SQL Injection tool
AutoSQLi
Features
- Save System – there is a complete save system, which can resume even when your pc crashed. – technology is cool
- Dorking – from the command line ( one dork ): YES – from a file: NO – from an interactive wizard: YES
- Waffing – Thanks to Ekultek, WhatWaf now has a JSON output function. – So it’s mostly finished 🙂 – UPDATE: WhatWaf is completely working with AutoSQLi. Sqlmap is the next big step
- SQL mapping – I’ll look if there is some sort of sqlmap API because I don’t wanna use
executethis time (: – Sqlmap is cool - REPORTING: YES
- Rest API: NOPE
it will follow this idea
- AutoSQLi will be a python application which will, automatically, using a dork provided by the user, return a list of websites vulnerable to a SQL injection.
- To find vulnerable websites, the users firstly provide a dork Dorking, which is passed to findDorks.py, which returns a list of URLs corresponding to it.
- Then, AutoSQLi will do some very basic checks ( TODO: MAYBE USING SQLMAP AND IT’s –smart and –batch function ) to verify if the application is protected by a Waf, or if one of it’s parameters is vulnerable.
- Sometimes, websites are protected by a Web Application Firewall, or in short, a WAF. To identify and get around these WAFs, AutoSQLi will use WhatWaf.
- Finally, AutoSQLi will exploit the website using sqlmap, and give the choice to do whatever he wants!
Tor
Also, AutoSQLi should work using Tor by default. So it should check for tor availability on startup.
Download
git clone https://github.com/jesuiscamille/AutoSQLi.git
Use
python3 autosqli.py