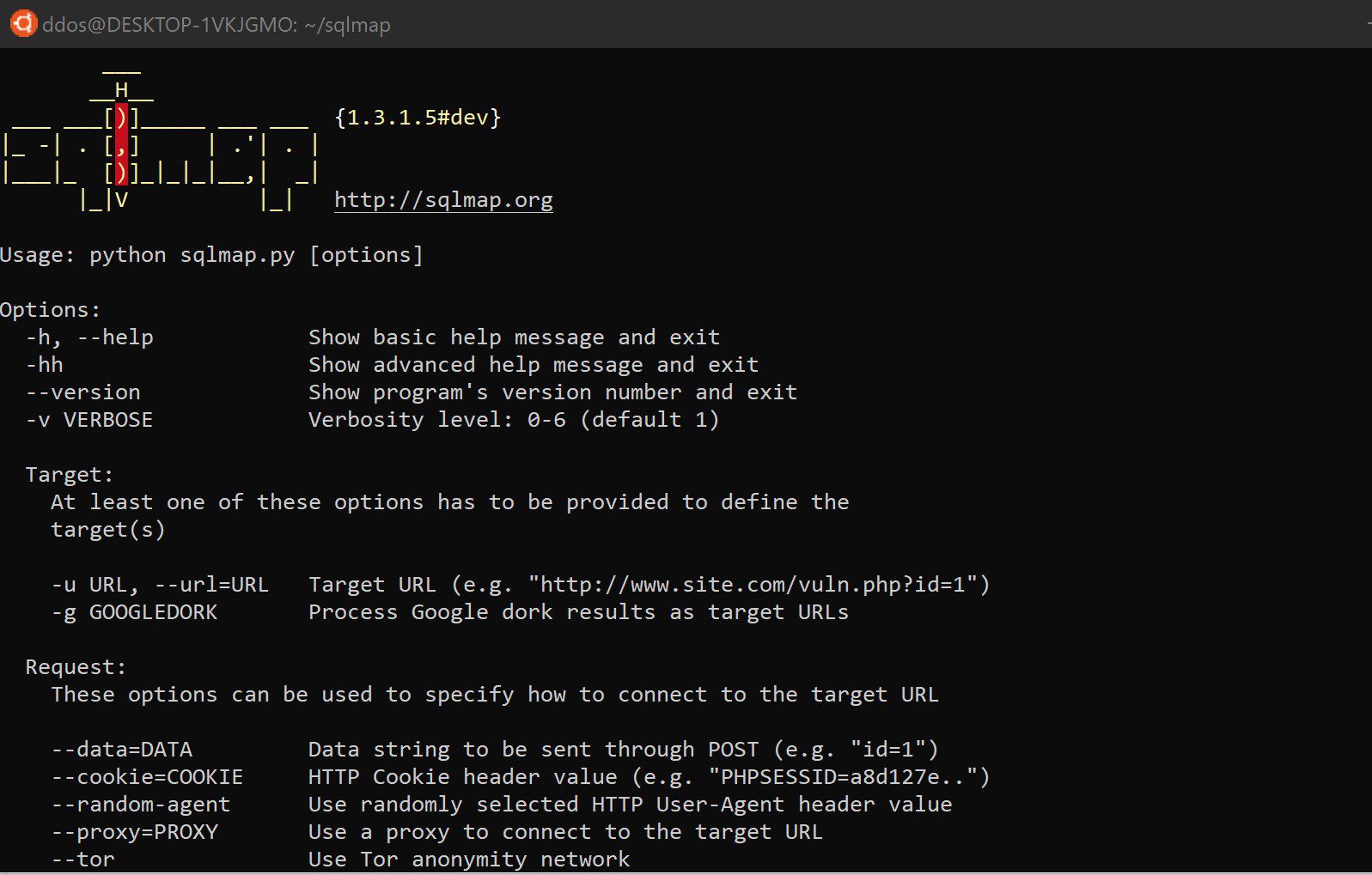
sqlmap v1.8 releases: automates the process of detecting and exploiting SQL injection flaws
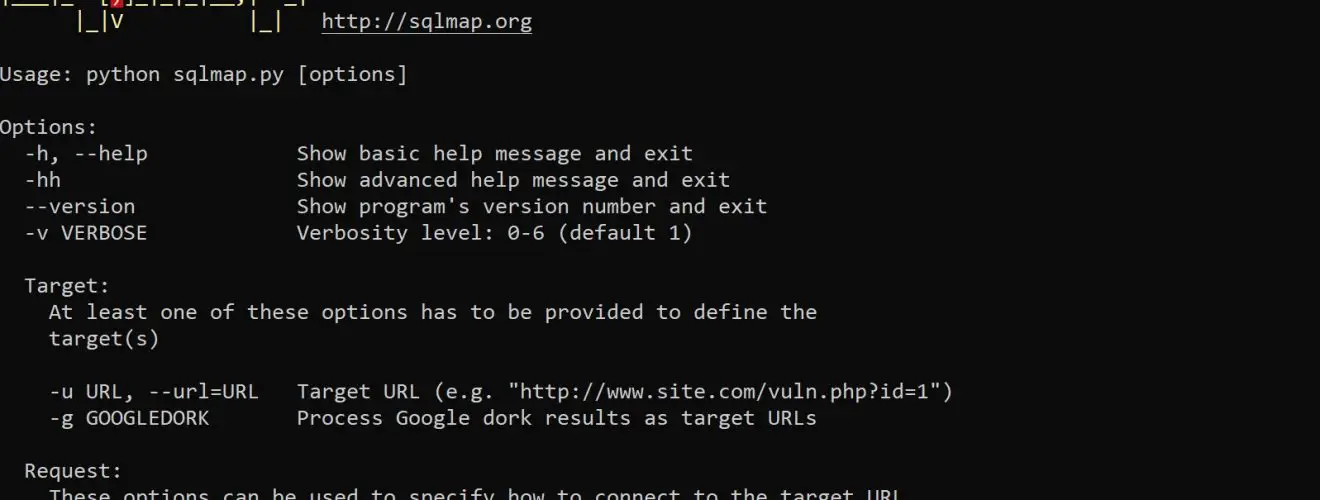
Sqlmap is an open-source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over database servers. It comes with a powerful detection engine, many niche features for the ultimate penetration tester, and a broad range of switches lasting from database fingerprinting, over data fetching from the database to accessing the underlying file system and executing commands on the operating system via out-of-band connections.
The sqlmap project is sponsored by Netsparker Web Application Security Scanner.
Features implemented in sqlmap include:
- Full support for MySQL, Oracle, PostgreSQL, Microsoft SQL Server, Microsoft Access, IBM DB2, SQLite, Firebird, Sybase, SAP MaxDB and HSQLDB database management systems.
- Full support for five SQL injection techniques: boolean-based blind, time-based blind, error-based, UNION query and stacked queries.
- Support to directly connect to the database without passing via a SQL injection, by providing DBMS credentials, IP address, port and database name.
- It is possible to provide a single target URL, get the list of targets from Burp proxy or WebScarab proxy requests log files, get the whole HTTP request from a text file or get the list of targets by providing sqlmap with a Google dork which queries Google search engine and parses its results page. You can also define a regular-expression based scope that is used to identify which of the parsed addresses to test.
- Tests provided GET parameters, POST parameters, HTTP Cookie header values, HTTP User-Agent header value and HTTP Referer header value to identify and exploit SQL injection vulnerabilities. It is also possible to specify a comma-separated list of specific parameter(s) to test.
- Option to specify the maximum number of concurrent HTTP(S) requests (multi-threading) to speed up the blind SQL injection techniques. Vice versa, it is also possible to specify the number of seconds to hold between each HTTP(S) request. Others optimization switches to speed up the exploitation are implemented too.
- HTTP
Cookieheader string support, useful when the web application requires authentication based upon cookies and you have such data or in case you just want to test for and exploit SQL injection on such header values. You can also specify to always URL-encode the Cookie. - Automatically handles HTTP
Set-Cookieheader from the application, re-establishing of the session if it expires. Test and exploit on these values is supported too. Vice versa, you can also force to ignore any Set-Cookie header. - HTTP protocol Basic, Digest, NTLM and Certificate authentications support.
- HTTP(S) proxy support to pass by the requests to the target application that works also with HTTPS requests and with authenticated proxy servers.
- Options to fake the HTTP
Refererheader value and the HTTPUser-Agentheader value specified by user or randomly selected from a textual file. - Support to increase the verbosity level of output messages: there exist seven levels of verbosity.
- Support to parse HTML forms from the target URL and forge HTTP(S) requests against those pages to test the form parameters against vulnerabilities.
- Granularity and flexibility in terms of both user’s switches and features.
- Estimated time of arrival support for each query, updated in real time, to provide the user with an overview on how long it will take to retrieve the queries’ output.
- Automatically saves the session (queries and their output, even if partially retrieved) on a textual file in real time while fetching the data and resumes the injection by parsing the session file.
- Support to read options from a configuration INI file rather than specify each time all of the switches on the command line. Support also to generate a configuration file based on the command line switches provided.
- Support to replicate the back-end database tables structure and entries on a local SQLite 3 database.
- Option to update sqlmap to the latest development version from the subversion repository.
- Support to parse HTTP(S) responses and display any DBMS error message to the user.
- Integration with other IT security open source projects, Metasploit and w3af.
- More…
Changelog v1.8
Related Reading SQLmap Tutorial
- tamper script for bypassing WAF
- with Google Dork for exploiting SQL injection
- POST request injection
- Perform a bulk injection testing with BurpSuite
- Web-GUI
- useful commands
sqlmap is (C) 2006-2018 Bernardo Damele Assumpcao Guimaraes, Miroslav Stampar.






