BlackWidow v1.3 releases: web application scanner to gather OSINT and fuzz for OWASP vulnerabilities

BlackWidow is a python based web application spider to gather subdomains, URL’s, dynamic parameters, email addresses and phone numbers from a target website. This project also includes Inject-X fuzzer to scan dynamic URL’s for common OWASP vulnerabilities.
FEATURES:
- Automatically collect all URL’s from a target website
- Automatically collect all dynamic URL’s and parameters from a target website
- Automatically collect all subdomains from a target website
- Automatically collect all phone numbers from a target website
- Automatically collect all email addresses from a target website
- Automatically collect all form URL’s from a target website
- Automatically scan/fuzz for common OWASP TOP vulnerabilities
- Automatically saves all data into sorted text files
Changelog v1.3
- Updated installer and both python scripts to support python3
- Fixed bug in BlackWidow dynamic URL’s not being captured properly
LINUX INSTALL:
git clone https://github.com/1N3/BlackWidow.git
cp blackwidow /usr/bin/blackwidow
cp injectx.py /usr/bin/injectx.py
pip install -r requirements.txt
USAGE:
blackwidow
- -u https://target.com – crawl target.com with 3 levels of depth.
- -d target.com -l 5 – crawl the domain: target.com with 5 levels of depth.
- -d target.com -l 5 -s y – crawl the domain: target.com with 5 levels of depth and fuzz all unique parameters for OWASP vulnerabilities.
injectx.py https://test.com/uers.php?user=1&admin=true – Fuzz all GET parameters for common OWASP vulnerabilities.
SAMPLE REPORT:
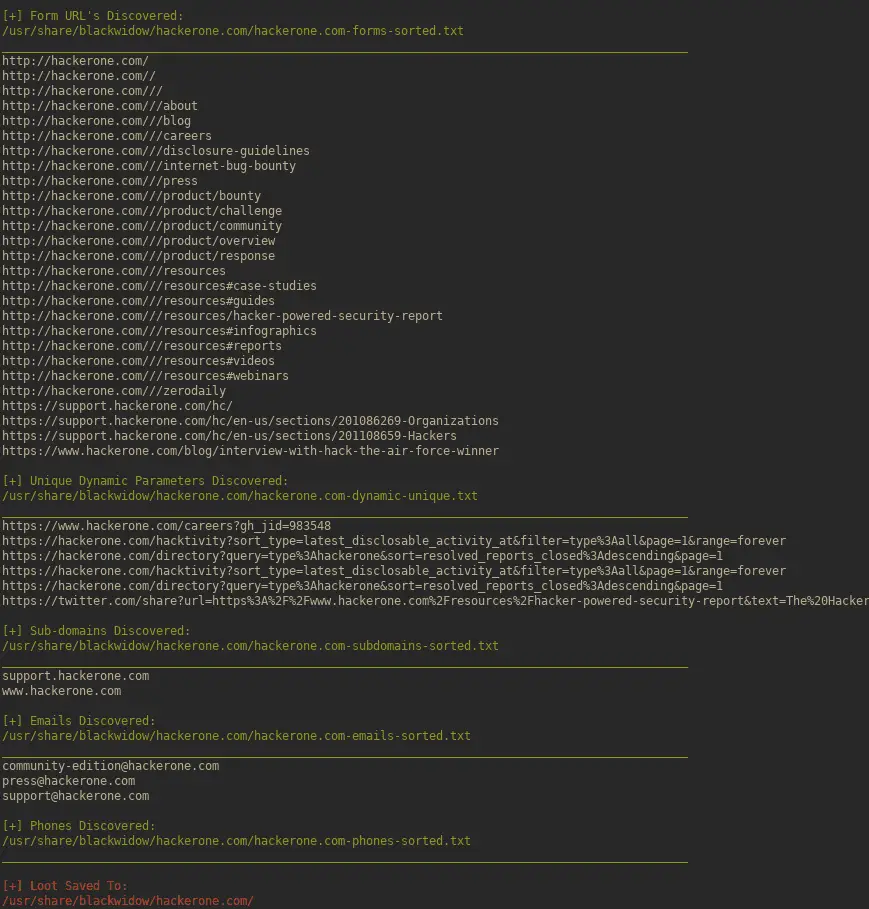
Demo
Copyright (C) 2018 1N3@CrowdShield
Source: https://github.com/1N3/






