bloodyAD v1.1.1 releases: Active Directory Privilege Escalation Framework

bloodyAD
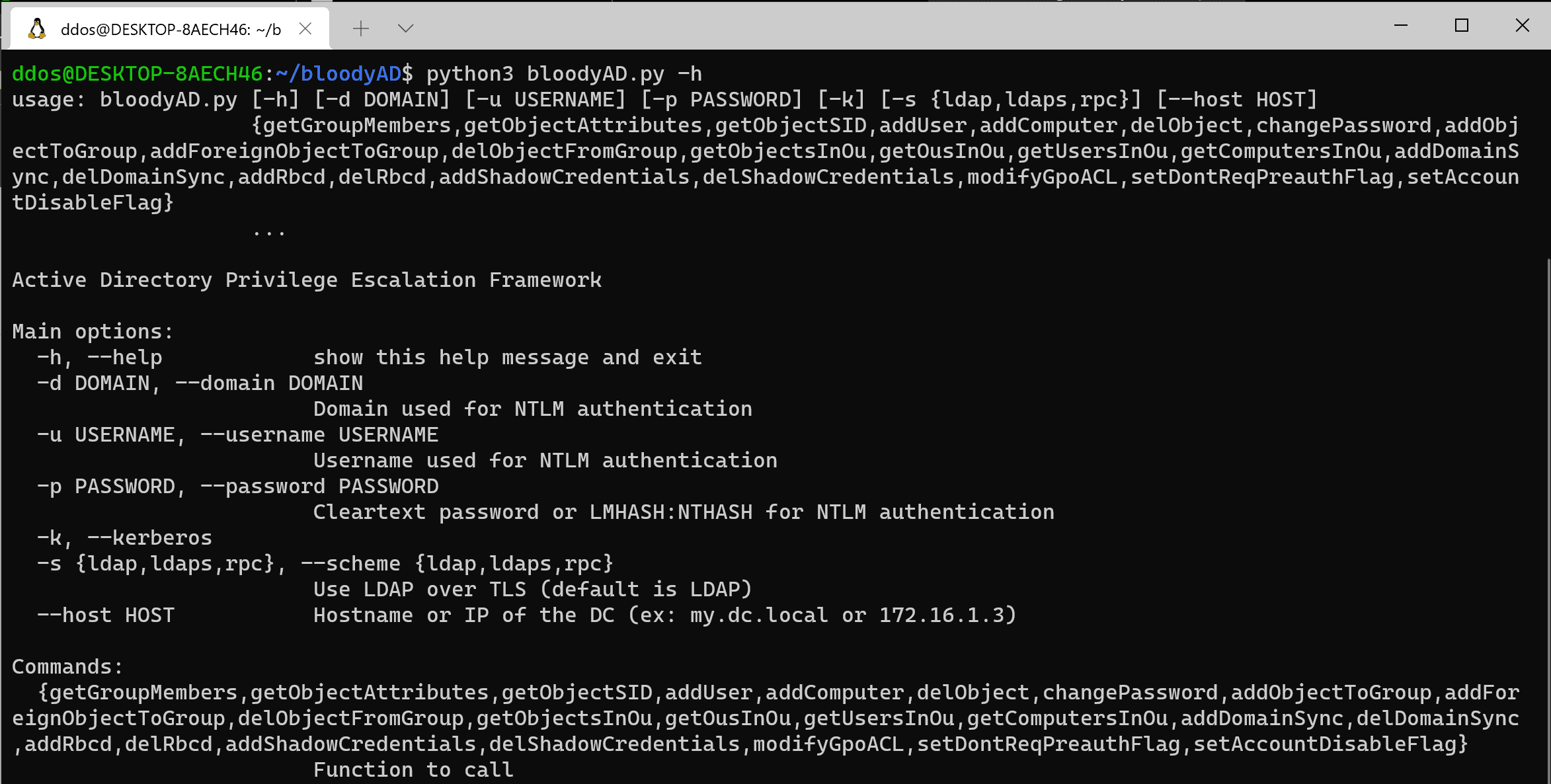
BloodyAD is an Active Directory Privilege Escalation Framework.
This tool can perform specific LDAP/SAMR calls to a domain controller in order to perform AD privesc. It supports authentication using cleartext passwords, pass-the-hash, pass-the-ticket, or certificates and binds to LDAP services of a domain controller to perform AD privesc.
It is designed to be used transparently with a SOCKS proxy.
How it works
bloodyAD communicates with a DC using mainly the LDAP protocol in order to get information or add/modify/delete AD objects. The exchange of sensitive information such as passwords is now supported using cleartext LDAP.
Changelog v1.1.1
-
Improve search functionalities
Install
Requirement
The following are required:
- Python 3
- DSinternals
- Impacket
- Ldap3
Download
git clone https://github.com/CravateRouge/bloodyAD.git
Use
Copyright (C) 2021 CravateRouge
Source: https://github.com/CravateRouge/






