Category: Post Exploitation
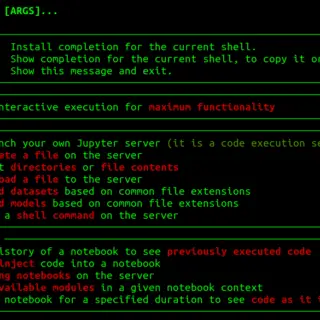
V’ger V’ger is an interactive command-line application for post-exploitation of authenticated Jupyter instances with a focus on AI/ML security operations. User Stories As a Red Teamer, you’ve found Jupyter credentials, but don’t know what you...
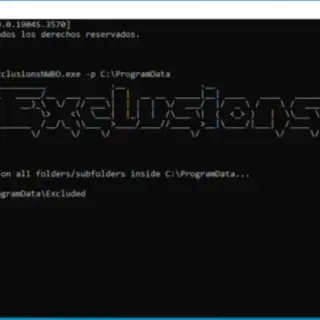
BadExclusions Now With Better Opsec BadExclusionsNWBO is an evolution from BadExclusions to identify folder custom or undocumented exclusions on AV/EDR. How it works? BadExclusionsNWBO copies and runs Hook_Checker.exe in all folders and subfolders of...
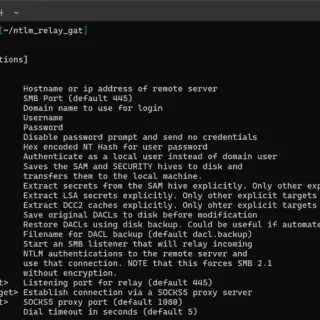
go-secdump Package go-secdump is a tool built to remotely extract hashes from the SAM registry hive as well as LSA secrets and cached hashes from the SECURITY hive without any remote agent and without...
proctools Small toolkit for extracting information and dumping sensitive strings from Windows processes. Made to accompany another project that’s in the works. procsearch – find sensitive strings in the target process memory searches for...
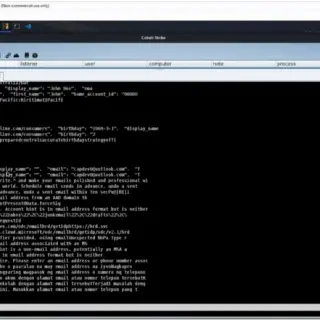
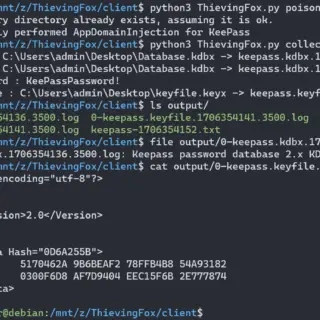
ThievingFox ThievingFox is a collection of post-exploitation tools to gather credentials from various password managers and Windows utilities. Each module leverages a specific method of injecting into the target process and then hooks internal...
NoArgs: Manipulating and Hiding Process Arguments NoArgs is a tool designed to dynamically spoof and conceal process arguments while staying undetected. It achieves this by hooking into Windows APIs to dynamically manipulate the Windows...
VectorKernel PoCs for Kernelmode rootkit techniques research or education. Currently focusing on Windows OS. All modules support 64-bit OS only. NOTE Some modules use ExAllocatePool2 API to allocate kernel pool memory. ExAllocatePool2 API is not...
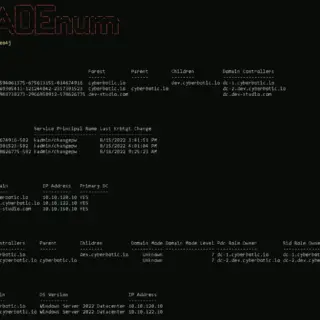
Invoke-ADEnum Active Directory Enumeration Invoke-ADEnum is an Active Directory enumeration tool designed to automate the process of gathering information from an Active Directory environment, leveraging the capabilities of PowerView. With Invoke-ADEnum, you can quickly...
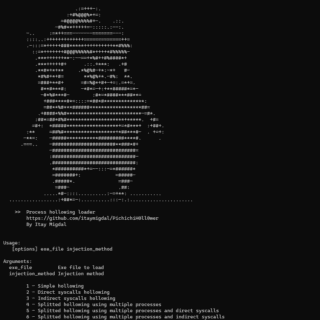
PichichiH0ll0wer Process hollowing loader written in Nim for PEs only PichichiH0ll0wer has some features to protect your payload. Features Configurable builder Payload encrypted and compressed (and optionally splitted) in the hollow loader Supports splitted...
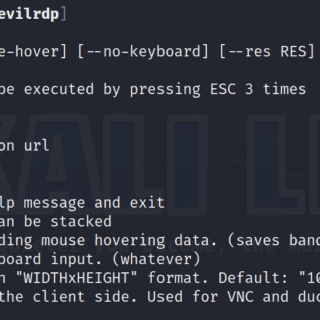
EVILRDP – More control over RDP The evil twin of aardwolfgui using the aardwolf RDP client library that gives you extended control over the target and additional scripting capabilities from the command line. Features Control the mouse...
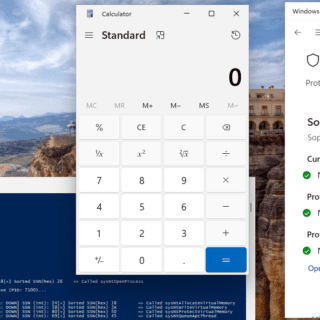
DarkWidow This is a Dropper/Post Exploitation Tool (or can be used in both situations) targeting Windows. Capabilities: Indirect Dynamic Syscall SSN + Syscall address sorting via Modified TartarusGate approach Remote Process Injection via APC...
MultiDump MultiDump is a post-exploitation tool written in C for dumping and extracting LSASS memory discreetly, without triggering Defender alerts, with a handler written in Python. MultiDump supports LSASS dump via ProcDump.exe or comsvc.dll, it offers...
UAC-BOF-Bonanza This repository serves as a collection of public UAC bypass techniques that have been weaponized as BOFs. A single module that integrates all techniques has been provided to use the BOFs via the...
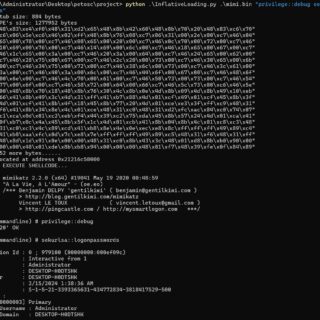
InflativeLoading Background Converting an exe to shellcode is one of my goals, in this way, some security tools like Mimikatz can be used with more flexibility. Though some tools like Donut already achieved it, I still...
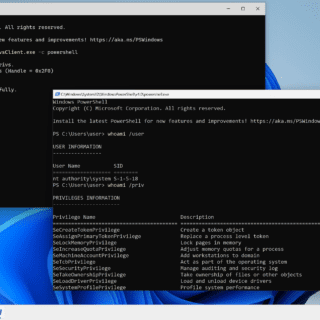
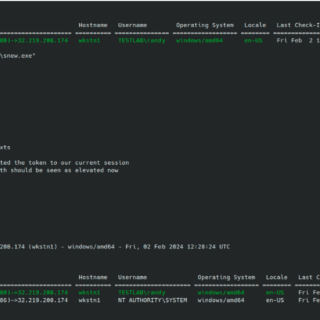
Disable Windows Defender Privilege tokens are permissions given by the system to a process. For example, if a process has a “SeShutdownPrivilege” token, then it has the right to turn off your computer.If your...