Category: Post Exploitation
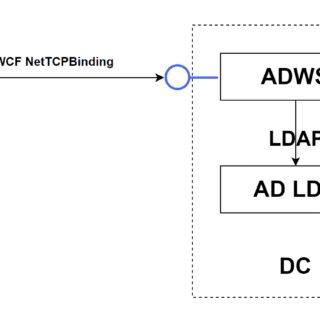
SOAPHound SOAPHound is a .NET data collector tool, which collects Active Directory data via the Active Directory Web Services (ADWS) protocol. SOAPHound is an alternative to several open-source security tools that are commonly used...
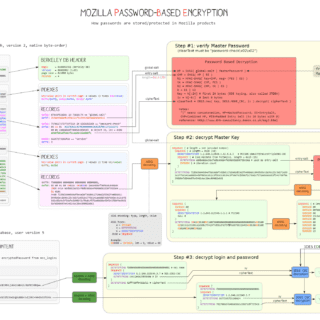
Cookie-Monster Steal browser cookies for Edge, Chrome, and Firefox through a BOF or exe! Cookie-Monster will extract the WebKit master key, locate a browser process with a handle to the Cookies and Login Data...
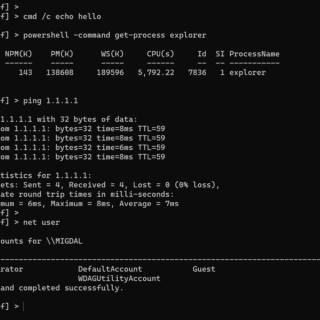
LOLSpoof LOLSpoof is an interactive shell program that automatically spoofs the command line arguments of the spawned process. Just call your incriminate-looking command line LOLBin (e.g. powershell -w hidden -enc ZwBlAHQALQBwAHIAbwBjAGUA….) and LOLSpoof will...
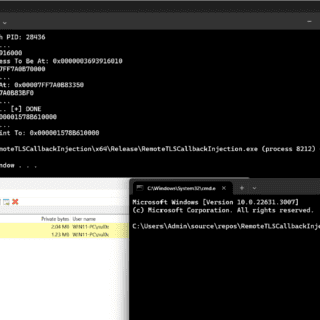
Maldev Academy – RemoteTLSCallbackInjection This method utilizes TLS callbacks to execute a payload without spawning any threads in a remote process. This method is inspired by Threadless Injection as RemoteTLSCallbackInjection does not invoke any API calls...
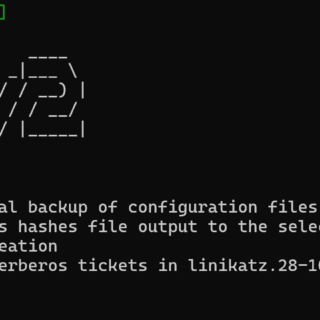
LinikatzV2 LinikatzV2 is a bash script based on the Linikatz tool developed by a time machine. It allows post-exploitation tasks on UNIX computers joined to Active Directory, using various methods for credential mining. This...
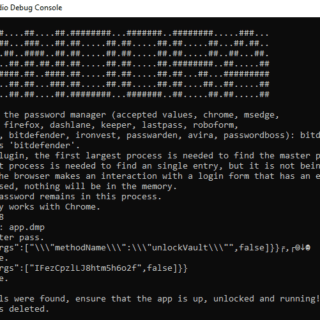
Pandora This is a red team tool that assists in gathering credentials from different password managers. They are separated into three categories, Windows 10 desktop applications, browsers, and browser plugins. This may work on...
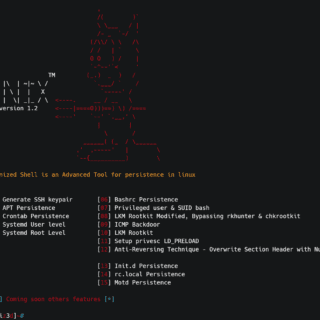
D3m0n1z3dShell Demonized Shell is an Advanced Tool for persistence in Linux. Demonized Features Auto Generate SSH keypair for all users APT Persistence Crontab Persistence Systemd User level Systemd Root Level Bashrc Persistence Privileged user...
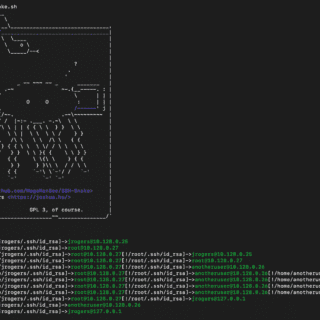
SSH-Snake: Automated SSH-Based Network Traversal SSH-Snake is a powerful tool designed to perform automatic network traversal using SSH private keys discovered on systems, to create a comprehensive map of a network and its dependencies,...
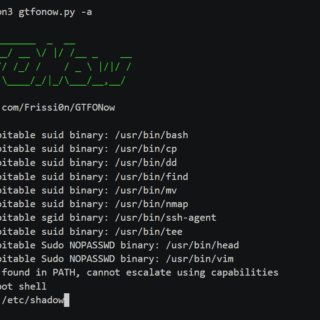
GTFONow Automatic privilege escalation on Unix systems by exploiting misconfigured setuid/setgid binaries, capabilities, and sudo permissions. Designed for CTFs but also applicable in real-world pentests. Features Automatically exploit misconfigured sudo permissions. Automatically exploit misconfigured...
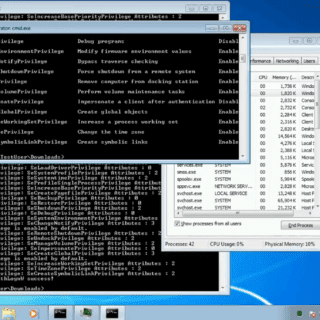
Stinger CIA Vault7 leak describes Stinger as a Privilege Escalation module in the “Fine Dining” toolset. Stinger is a “UAC bypass that obtains the token from an auto-elevated process, modifies it, and reuses it...
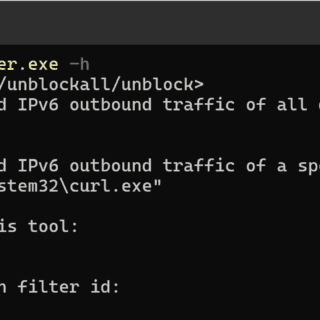
EDRSilencer Inspired by the closed-source FireBlock tool FireBlock from MdSec NightHawk, I created my version. This tool was created to block the outbound traffic of running EDR processes using Windows Filtering Platform (WFP) APIs....
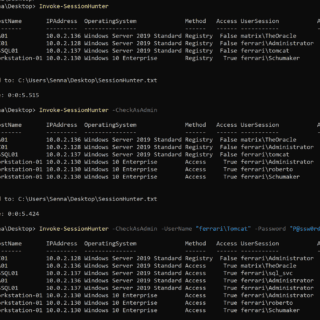
Invoke-SessionHunter Retrieve and display information about active user sessions on remote computers. No admin privileges are required. The tool leverages the remote registry service to query the HKEY_USERS registry hive on the remote computers....
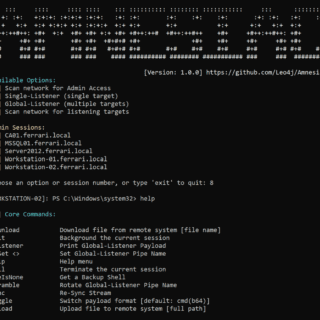
Amnesiac Amnesiac is a post-exploitation framework designed to assist with lateral movement within active directory environments. Amnesiac is being developed to bridge a gap on Windows OS, where post-exploitation frameworks are not readily available...
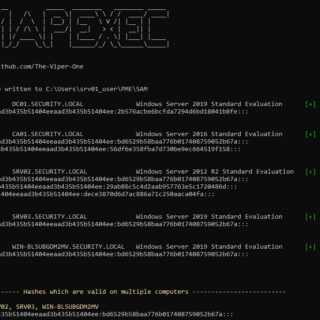
What is PsMapExec A PowerShell tool heavily inspired by the popular tool CrackMapExec. Far too often I find myself on engagements without access to Linux in order to make use of CrackMapExec. PsMapExec is...
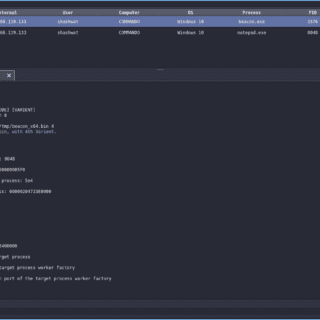
PoolParty A collection of fully-undetectable process injection techniques abusing Windows Thread Pools. Presented at Black Hat EU 2023 Briefings under the title – The Pool Party You Will Never Forget: New Process Injection Techniques Using...