DarkWidow: a Dropper/Post Exploitation Tool targeting Windows
DarkWidow
This is a Dropper/Post Exploitation Tool (or can be used in both situations) targeting Windows.

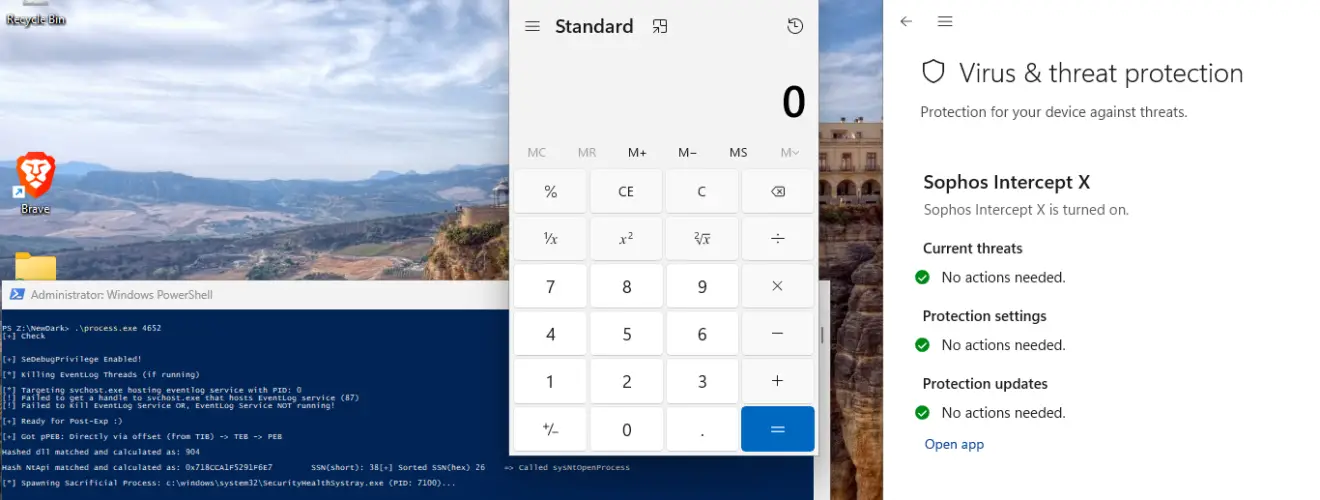
Successful Execution WithOut Creating an Alert on Sofos XDR EndPoint
- Indirect Dynamic Syscall
- SSN + Syscall address sorting via Modified TartarusGate approach
- Remote Process Injection via APC Early Bird (MITRE ATT&CK TTP: T1055.004)
- Spawns a sacrificial Process as the target process
- ACG(Arbitrary Code Guard)/BlockDll mitigation policy on the spawned process
- PPID spoofing (MITRE ATT&CK TTP: T1134.004)
- Api resolving from TIB (Directly via offset (from TIB) -> TEB -> PEB -> resolve Nt Api) (MITRE ATT&CK TTP: T1106)
- Cursed Nt API hashing
- EDR/Ring-3/UserLand hook Bypass
- The syscall and return statement are executed from the memory of ntdll.dll
- EDR detection based on checking the return address in the call stack can be bypassed.
Install & Use
Copyright (c) 2023 Soumyani1





