BLUESPAWN
What it does
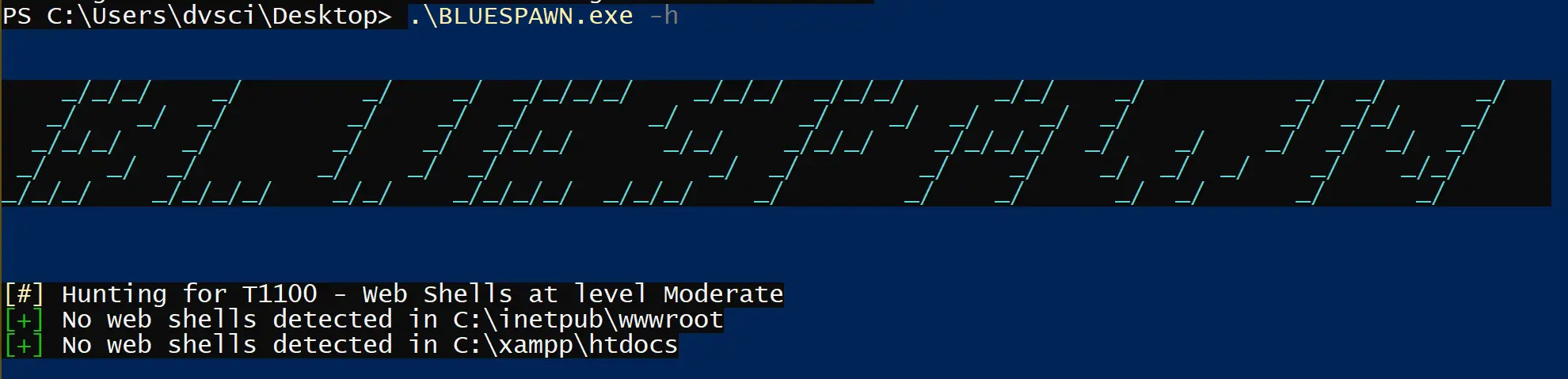
BLUESPAWN helps blue teams monitor Windows systems in real-time against active attackers by detecting anomalous activity
Why we made BLUESPAWN
We’ve created and open-sourced this for a number of reasons which include the following:
- Move Faster: We wanted tooling specifically designed to quickly identify malicious activity on a system
- Know our Coverage: We wanted to know exactly what our tools could detect and not rely on blackbox software as much (ie AV programs). This approach will help us to better focus our efforts on specific lines of effort and have confidence in the status of others.
- Better Understanding: We wanted to better understand the Windows attack surface in order to defend it better
- More Open-Source Blue Team Software: While there are many open-source Red Team Tools out there, the vast majority of some of the best Blue Team tools are closed-source (ie, AVs, EDRs, SysInternals, etc). We shouldn’t need to rely on security through obscurity to prevent malicious actors (obviously very difficult, but something to strive for!)
- Demonstrate Features of Windows API: We combed through a ton of Microsoft Documentation, StackOverflow Answers, and more to create this. Hopefully, others may find some of the code useful.
Architecture
BLUESPAWN consists of three main modules – Hunt, Monitor, and React. Each of these modules, while a largely self-contained project, will have a way to interact with other modules. For example, Monitor may notice something fishy going on and notify Hunt. Hunt could then perform a deeper analysis of the suspicious file or process, and depending on its decision, inform React that something must be done about it.
Each module consists of multiple sub-modules.
Project Structure
- Hunt
- Configuration-Settings
- CollectInfo.(h/cpp)
- Registry.(h/cpp)
- Services.(h/cpp)
- Drivers.(h/cpp)
- FileSystem
- FileSystem.(h/cpp)
- ProcessAnalyze
- Hunt.(h/cpp)
- Techniques.(h/cpp)
- Configuration-Settings
- Monitor
- FileMonitor (File System Minifilter)
- ProcessMonitor
- RegistryMonitor
- UserHooking
- ETW??
- SSDTHooking??
- React
- BLUESPAWN (main)
- BLUESPAWN.cpp
- Logging
- ConsoleOutput.(h/cpp)
- FileOutput.(h/cpp)
Module Relationship
- A Hunt can be customized by Tactic, Data Source, Verbosity, Reaction Type, Aggressiveness.
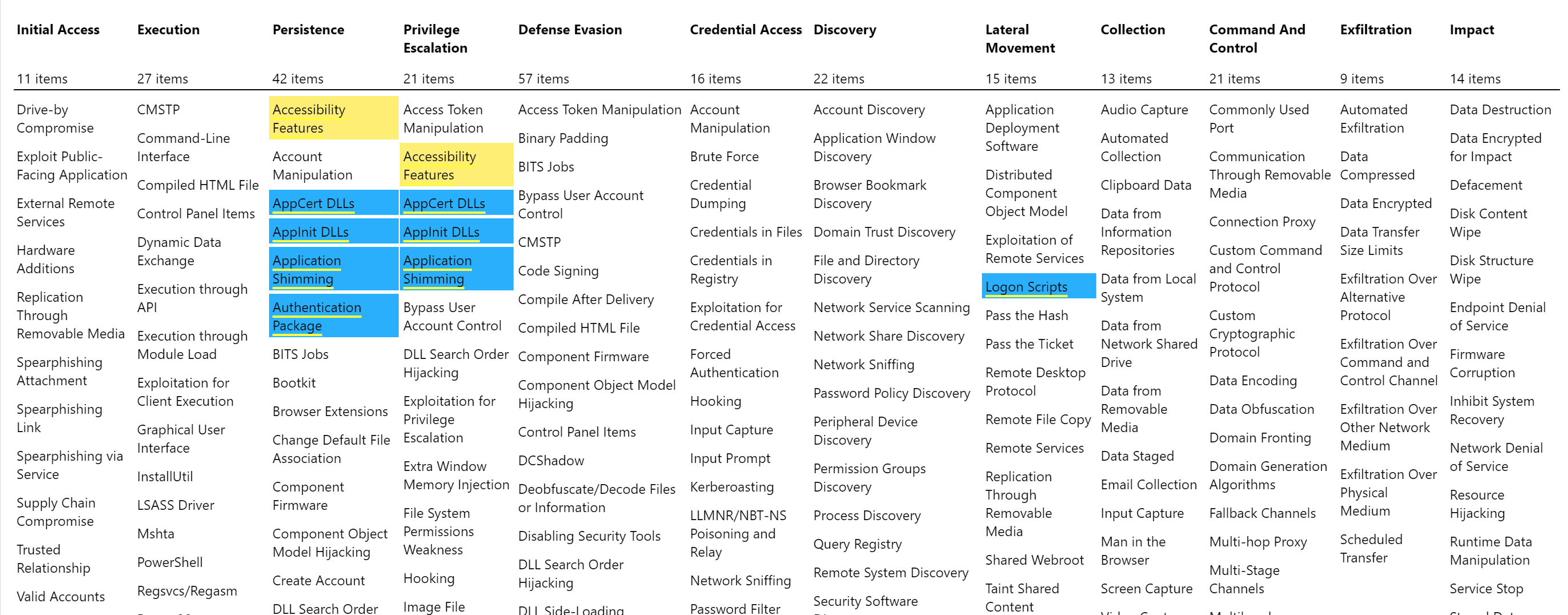
- Tactic – {Initial Access, Execution, Persistence, Privilege Escalation, Defense Evasion, Credential Access, Discovery, Lateral Movement, Collection, Command and Control, Exfiltration, Impact}
- Data Source – {Configuration-Settings, File System, Processes}
- MITRE Data Sources – {Windows Event Logs, Anti-virus, Binary File Metadata, Data Loss Prevention, DLL Monitoring, Loaded DLLs, Malware Reverse Engineering, Netflow/Enclave Netflow, Network Intrusion Detection System, Network Protocol Analysis, SSL/TLS Inspection, System Calls}
- Verbosity – {{Good, Bad, Good + Bad}, {Item, Item + Detail}
- Reaction Type
- Aggressiveness – {Cursory, Moderate, Careful}
- A Technique should have 3 levels of aggressiveness (see above).
- Logging output can take the following forms: {Regular, Markdown, JSON, XML}
Changelog v0.5.1-alpha
- Add interface for scan mode! Scan folders, files, and processes directly with the
--scanflag! - User permissions management added
- JSON log sink added
- Add more hunts
- Bugfixes
Mitigate Mode
- Mitigations are now configurable via json
- New mitigations have been added
- Mitigations’ enforcement-levels are now properly configured
- Mitigations’ associated software is now used. Mitigations may have an associated software and version, and unless the system has that software at the specified version, the mitigation won’t be applied.
- Mitigation enforcement can now be configured with a much finer granularity. A default enforcement level may be specified, which can be overwritten for each mitigation, and each mitigation policy may be configured to ignore the default enforcement level.
- Mitigation enforcement now produces a report describing the results
Download
Use
Copyright (C) 2019 ION28