BruteLoops v0.2 releases: Protocol agnostic online password guessing API
BruteLoops
A dead-simple library providing the foundational logic for efficient password brute force attacks against authentication interfaces.
A “modular” example is included with the library that demonstrates how to use this package. It’s fully functional and provides multiple brute force modules. Below is a sample of its capabilities:
http.accellion_ftp Accellion FTP HTTP interface login module
http.basic_digest Generic HTTP basic digest auth
http.basic_ntlm Generic HTTP basic NTLM authentication
http.global_protect Global Protect web interface
http.mattermost Mattermost login web interface
http.netwrix Netwrix web login
http.okta Okta JSON API
http.owa2010 OWA 2010 web interface
http.owa2016 OWA 2016 web interface
smb.smb Target a single SMB server
testing.fake Fake authentication module for training/testing
Key Features
- Protocol agnostic – If a callback can be written in Python, BruteLoops can be used to attack it
- SQLite support – All usernames, passwords, and credentials are maintained in an SQLite database.
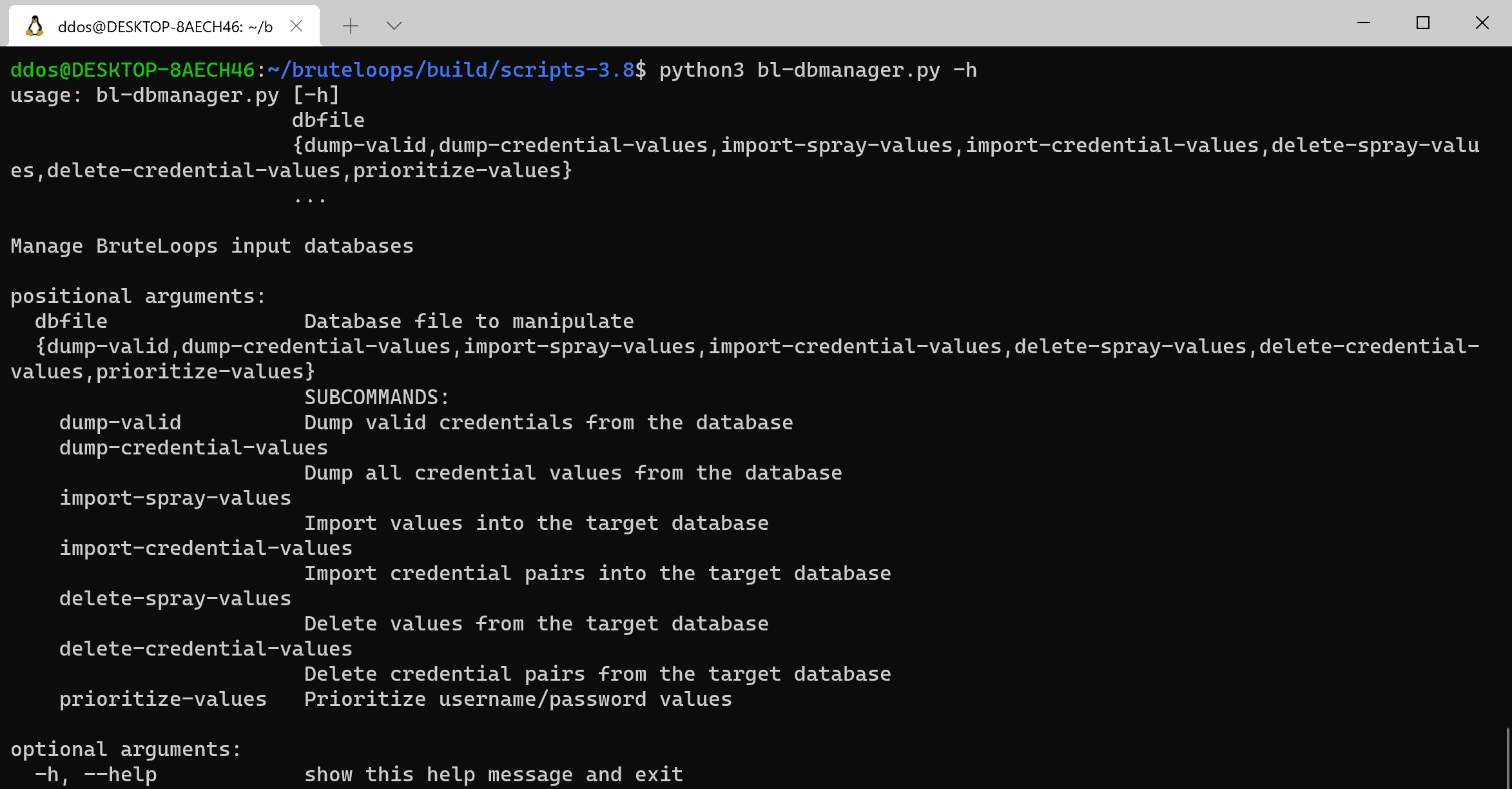
- A companion utility (dbmanager.py) that creates and manages input databases accompanies BruteLoops
- Spray and Stuffing Attacks in One Tool – BruteLoops supports both spray and stuffing attacks in the same attack logic and database, meaning that you can configure a single database and run the attack without heavy reconfiguration and confusion.
- Guess scheduling – Each username in the SQLite database is configured with a timestamp that is updated after each authentication event. This means we can significantly reduce the likelihood of locking accounts by scheduling each authentication event with precision.
- Fine-grained configurability to avoid lockout events – Microsoft’s lockout policies can be matched 1-to-1 using BruteLoop’s parameters:
- auth_threshold = Lockout Threshold
- max_auth_jitter = Lockout Observation Window
- Timestamps associated with each authentication event are tracked in BruteLoops’ SQLite database. Each username receives a distinct timestamp to assure that authentication event are highly controlled.
- Attack resumption – Stopping and resuming an attack is possible without worrying about losing your place in the attack or locking accounts.
- Multiprocessing – Speed up attacks using multiprocessing! By configuring the`parallel guess count, you’re effectively telling BruteLoops how many usernames to guess in parallel.
- Logging – Each authentication event can optionally be logged to disk. This information can be useful during red teams by providing customers with a detailed attack timeline that can be mapped back to logged events.
Install
git clone https://github.com/arch4ngel/bruteloops
cd bruteloops
python3 -m pip install -r requirements.txt
Tutorial
Copyright (c) 2020 Justin Angel





