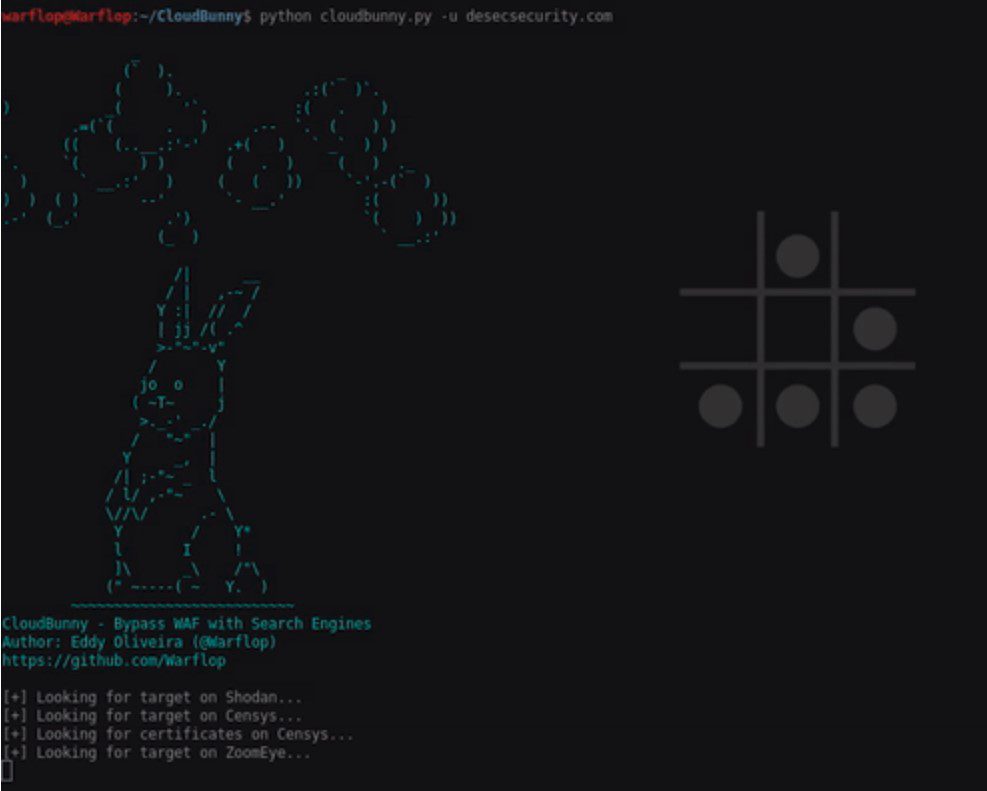
CloudBunny v2.0 releases: capture the real IP of the server that uses a WAF as a proxy or protection
CloudBunny
CloudBunny is a tool to capture the origin server that uses a WAF as a proxy or protection. You can read more about the tool here.
Changelog v2.0
- Fixed issues with running the code.
- Added page and result number options for Censys search. (1)
- Along with the ability to just search by certificate or by title.
- Added ability to authenticate with just your API key in Zoomeye.
- Added option for free account users on Shodan to search. (2)
- General code cleanup.
- Comming soon: the ability to read input files of domains list and save the output to file.
Download
git clone https://github.com/bwimpsett/CloudBunny.git
How works
In this tool, we used three search engines to search domain information: Shodan, Censys, and Zoomeye. To use the tools you need the API Keys, you can pick up the following links:
Shodan - https://account.shodan.io/ Censys - https://censys.io/account/api ZoomEye - https://www.zoomeye.org/profile
NOTE: In Zoomeye you need to enter the login and password, it generates a dynamic api key and I already do this work for you. Just enter your login and password.
After that, you need to put the credentials in the api.conf file.
Install the requirements:
$ sudo pip install -r requirements.txt
Usage
By default, the tool searches on all search engines (you can set this up by arguments), but you need to put the credentials as stated above. After you have loaded the credentials and installed the requirements, execute:
$ python cloudbunny.py -u securityattack.com.br
Check our help area:
$ python cloudbunny.py -h
Change securityattack.com.br for the domain of your choice.
Copyright (c) 2022 Brian Wimpsett
Source: https://github.com/bwimpsett/





