CLZero: fuzzing HTTP/1.1 CL.0 Request Smuggling Attack Vectors
CLZero
A project for fuzzing HTTP/1.1 CL.0 Request Smuggling Attack Vectors.
Inspired by the tool Smuggler all attack gadgets adapted from Smuggler and https://portswigger.net/research/how-to-turn-security-research-into-profit
CL.0 Identification method
The first request will be the “base” request. This is just for retrieving a successful response to compare probes against. All sequential requests will be the smuggle and probe pairs for each technique provided. The smuggle request contains the smuggle gadget and the probe is the request we will hopefully404 or hopefully405 status response – indicating a successful smuggle. Using a single TCP connection and pipelining both the smuggle request and the probe, would be perfect, however, it is difficult to tell whether the interesting/giveaway part of the response was generated by the front end or the backend – resulting in a lot of false positives. Using separate TCP connections to send the smuggle request and the probe, skips this. And ensures far fewer false positives. However, there is a new problem.
The problem
Ensuring that the smuggle request and probe are processed sequentially can be tricky, especially when dealing with a high-traffic site. To combat this CLZero can use the -skipread flag to skip reading the response of the smuggle request and instead immediately send the probe request. This saves a lot of time between requests and should be your most used technique as there is no real reason to wait for the response, we are just interested in the response to the probe request.
For more info see this blog.
Install
git clone https://github.com/Moopinger/CLZero.git
cd CLZero
pip3 install -r requirements.txt
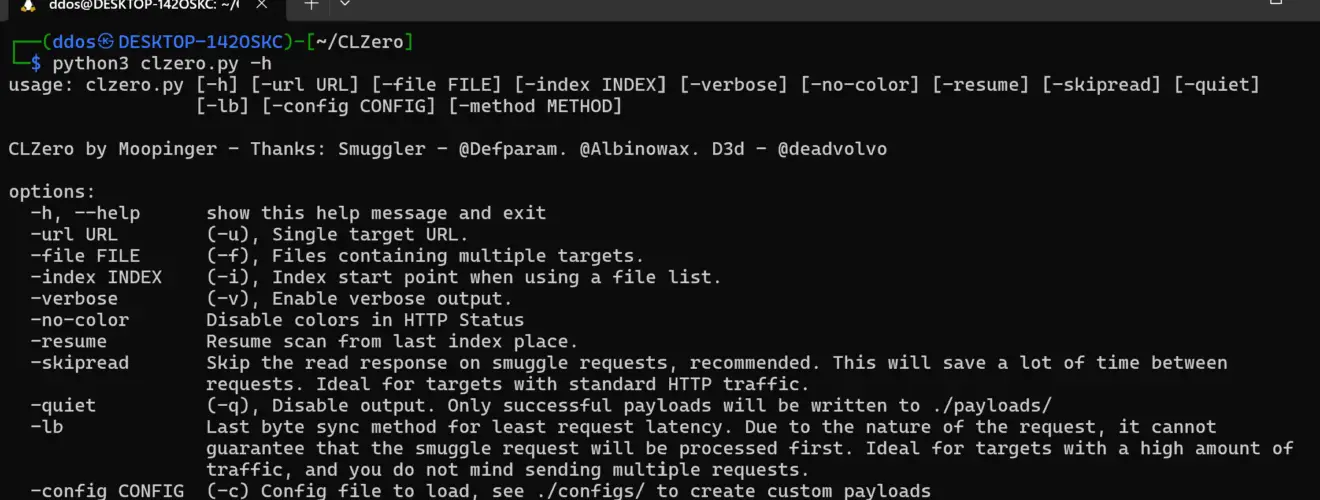
Use

Single target attack:
-
python3 clzero.py -u https://www.target.com/ -c configs/default.py -skipread
-
python3 clzero.py -u https://www.target.com/ -c configs/default.py -lb
Multi-target attack:
-
python3 clzero.py -l urls.txt -c configs/default.py -skipread
-
python3 clzero.py -l urls.txt -c configs/default.py -lb
Copyright (c) 2023 Charlie Smith
Source: https://github.com/Moopinger/






