Collect-MemoryDump v1.0 releases: Automated Creation of Windows Memory Snapshots for DFIR
Collect-MemoryDump
Collect-MemoryDump – Automated Creation of Windows Memory Snapshots for DFIR
Collect-MemoryDump.ps1 is a PowerShell script utilized to collect a Memory Snapshot from a live Windows system (in a forensically sound manner).
Features:
- Checks for Hostname and Physical Memory Size before starting memory acquisition
- Checks if you have enough free disk space to save the memory dump file
- Collects a Raw Physical Memory Dump w/ DumpIt, Magnet RamCapture, and WinPMEM
- Collects a Microsoft Crash Dump w/ DumpIt for Comae Beta from Magnet Idea Lab
- Checks for Encrypted Volumes w/ Magnet Forensics Encrypted Disk Detector
- Collects BitLocker Recovery Key
- Checks for installed Endpoint Security Tools (AntiVirus and EDR)
- Enumerates all necessary information from the target host to enrich your DFIR workflow
- Creates a password-protected Secure Archive Container (PW: IncidentResponse)
Usage
.\Collect-MemoryDump.ps1 [-Tool] [–skip]
Example 1 – Raw Physical Memory Snapshot
.\Collect-MemoryDump.ps1 -DumpIt
Example 2 – Microsoft Crash Dump (.zdmp) → optimized for uploading to Comae Investigation Platform
.\Collect-MemoryDump.ps1 -Comae
Note: You can uncompress *.zdmp files generated by DumpIt w/ Z2Dmp (Comae-Toolkit).
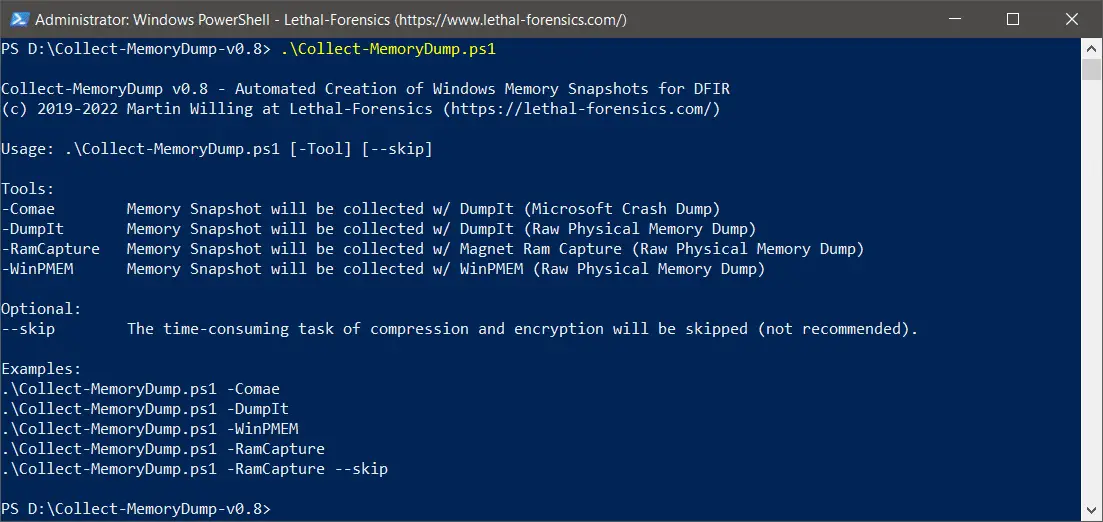
Fig 1: Help Message
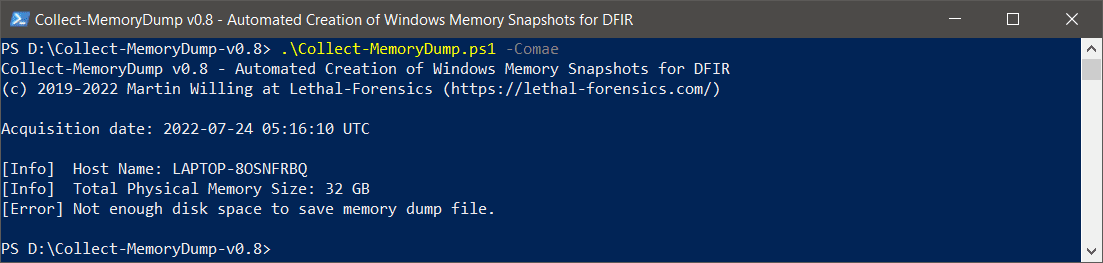
Fig 2: Check Available Space
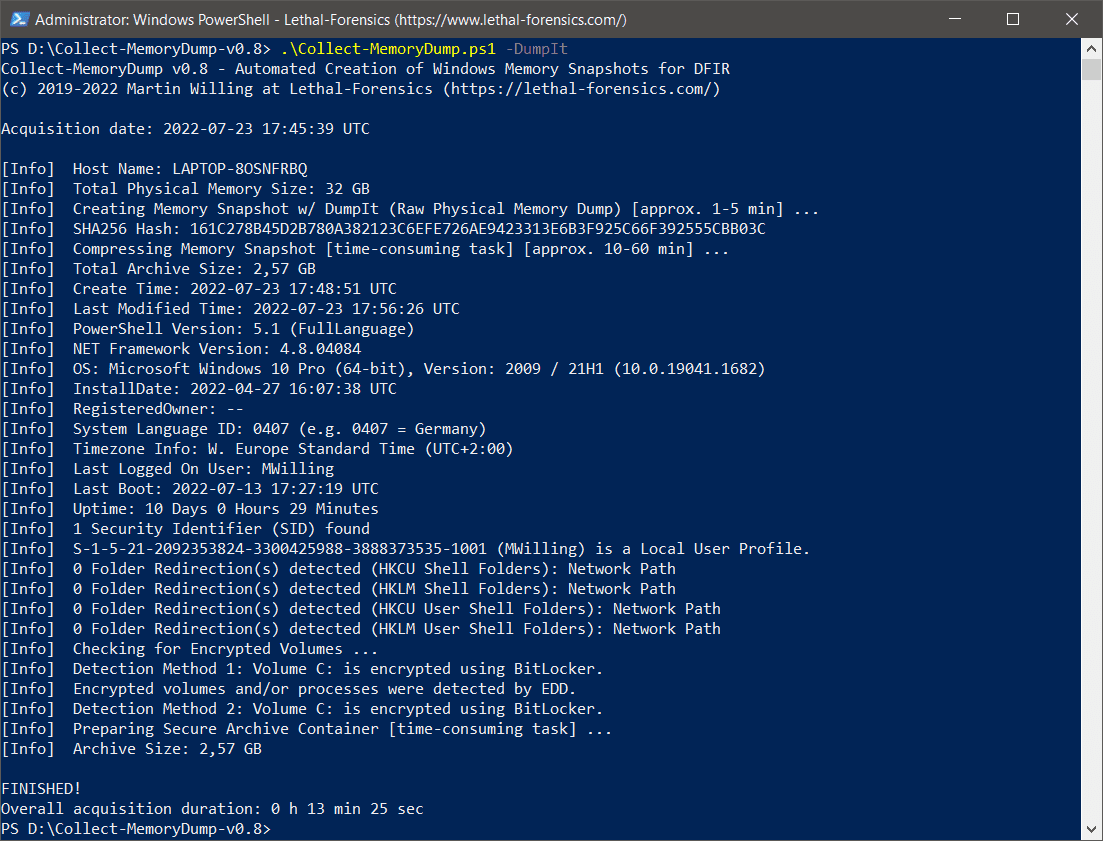
Fig 3: Automated Creation of Windows Memory Snapshot w/ DumpIt
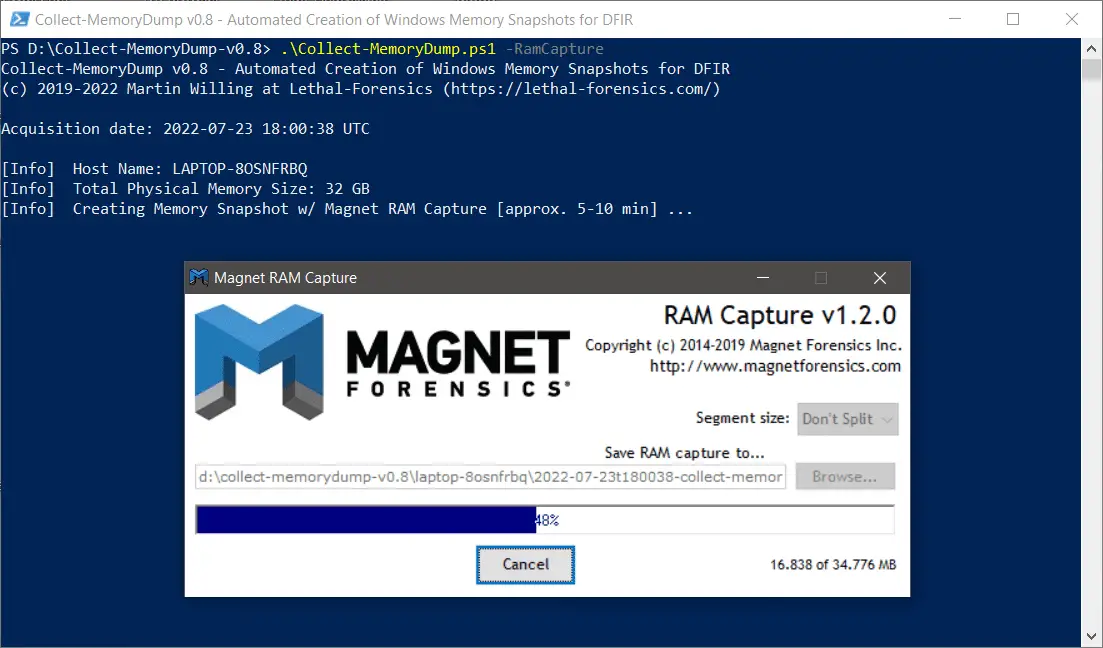
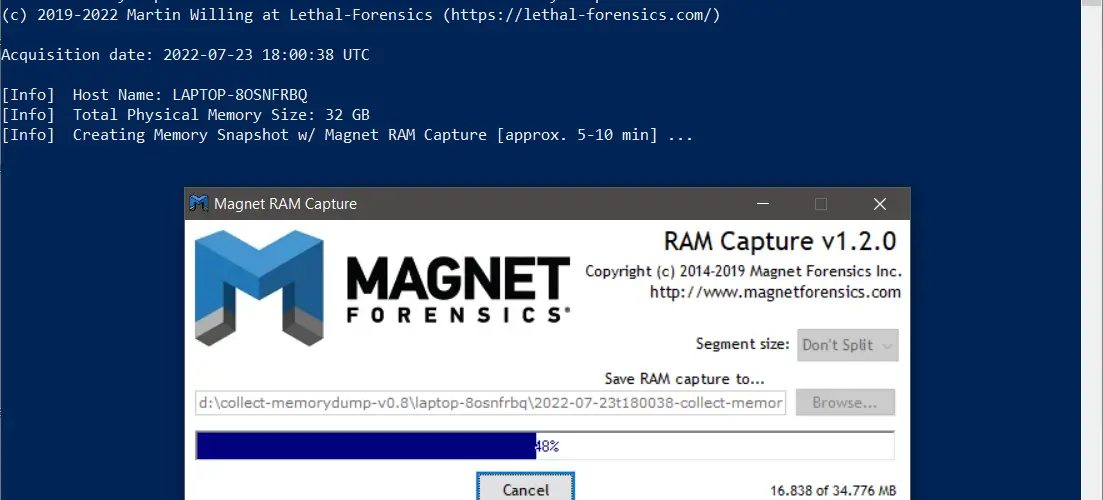
Fig 4: Automated Creation of Windows Memory Snapshot w/ Magnet RAM Capture
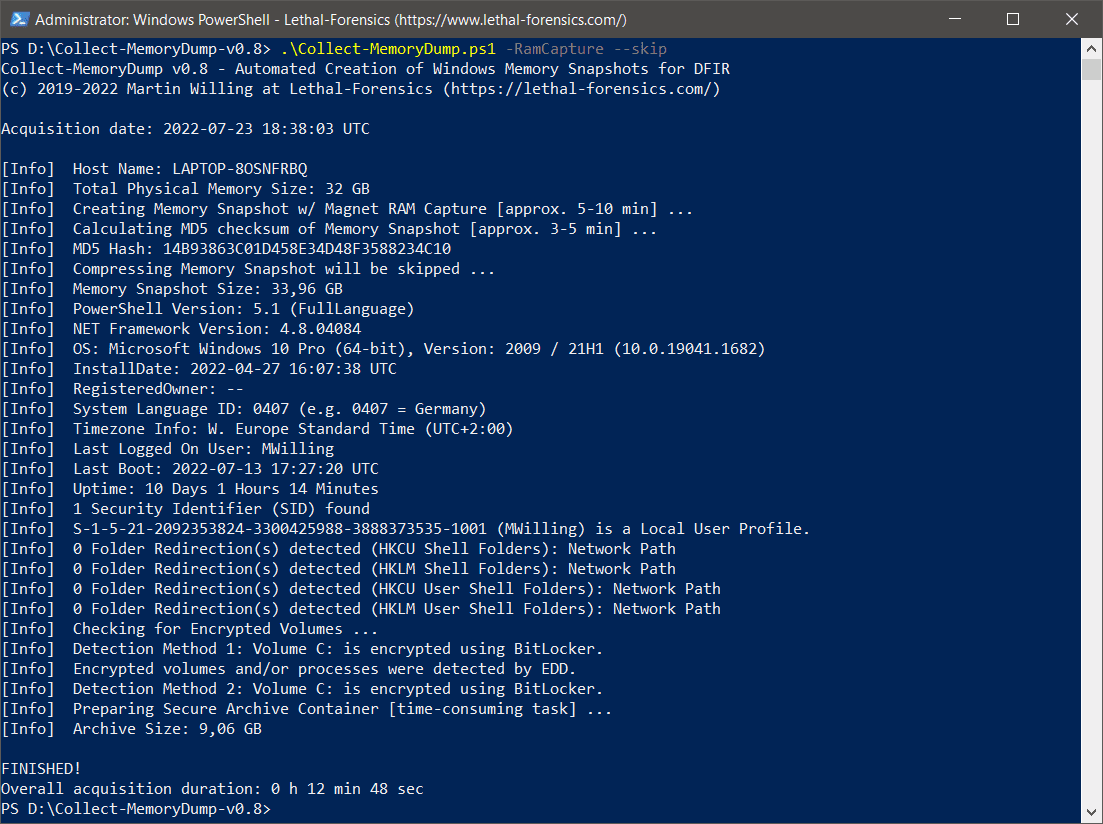
Fig 5: The time-consuming task of compressing the memory snapshot can be skipped (if needed)
Changelog v1.0
Added: Pagefile Collection w/ Magnet RESPONSE v1.7.0
Added: Capturing Running Process/Module Information w/ Magnet RESPONSE v1.7.0
Added: Error Notification (MessageBox)
Added: Improved OS Fingerprinting
Added: Improved LastBoot and Uptime (when Fast Startup is enabled)
Update: 7-Zip 22.01 Standalone Console –> 7-Zip 23.01 Standalone Console (2023-06-20)
Fixed: Other minor fixes and improvements
Download
Copyright (C) 2022 evild3ad






