CryptoTester: utility for playing with cryptography, geared toward ransomware analysis
CryptoTester
A utility for playing with cryptography, geared toward ransomware analysis.
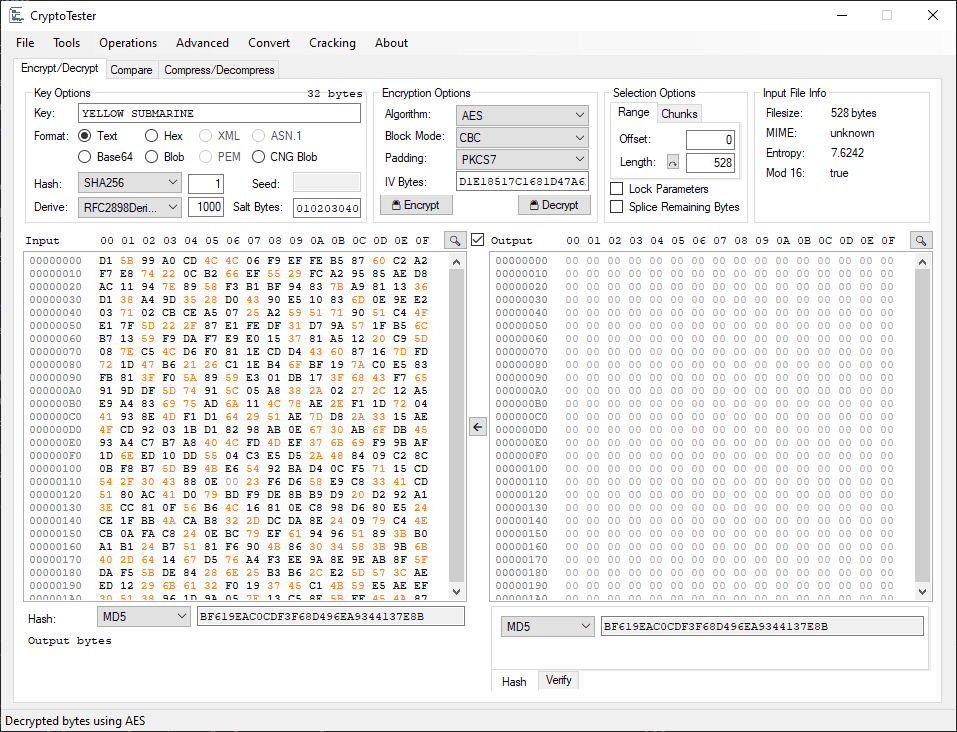
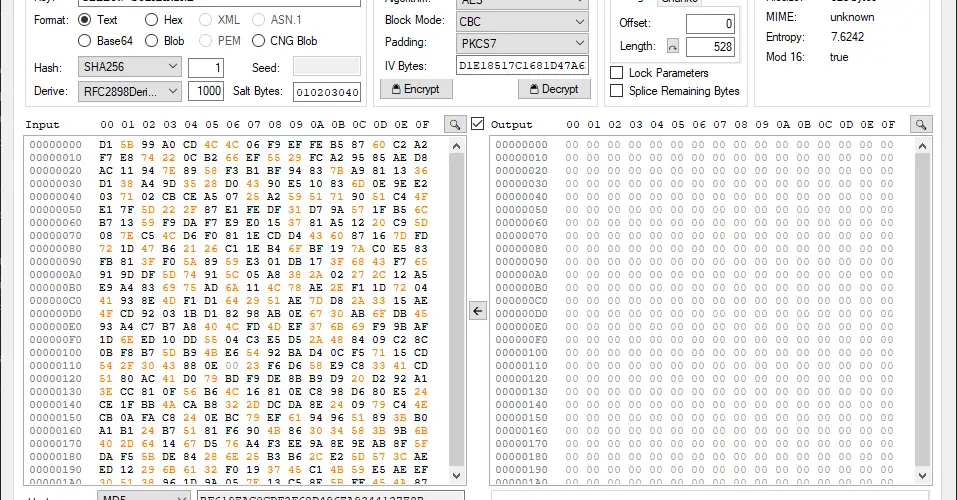
Hex Views
All hex views used in CryptoTester offer a few enhanced capabilities.
- Null bytes are colored a lighter gray
- Bytes representing ASCII characters are colored orange
- Newline patterns (0D 0A) are colored purple
- If pasting is available, any whitespace, newlines, and common delimiters are removed before parsing as hex
- Right-click options for copying bytes as a C Array or BigNum
On many views (e.g. Input and Output), clicking on the offset row (the 00 01 02 03… above the respective view) will open a dialog showing the bytes alongside the decoded view.
Integer Parsing
Most inputs that accept an integer, also accept special values and functions.
Examples:
- Hex: x10 -> 16
- Input Length: len -> 400
- Blocksize: block -> 16 (blocksize of the selected algorithm)
- Nearest: near(60, 16) -> 64
Simple arithmetic can be used in combination with these functions.
- near(len-x100, b)– Subtracts 256 from the input length, then rounds (up) to the nearest block size of the selected algorithm (e.g. 16 for AES)
Any negative values are assumed to be len – value, aka relative to the end of the input.






