Apache Calcite Avatica released the latest security bulletin on July 28, which contains a remote code execution vulnerability (CVE-2022-36364). The severity is moderate. The security researcher Peter M (@h1pmnh) has been credited with reporting this flaw.
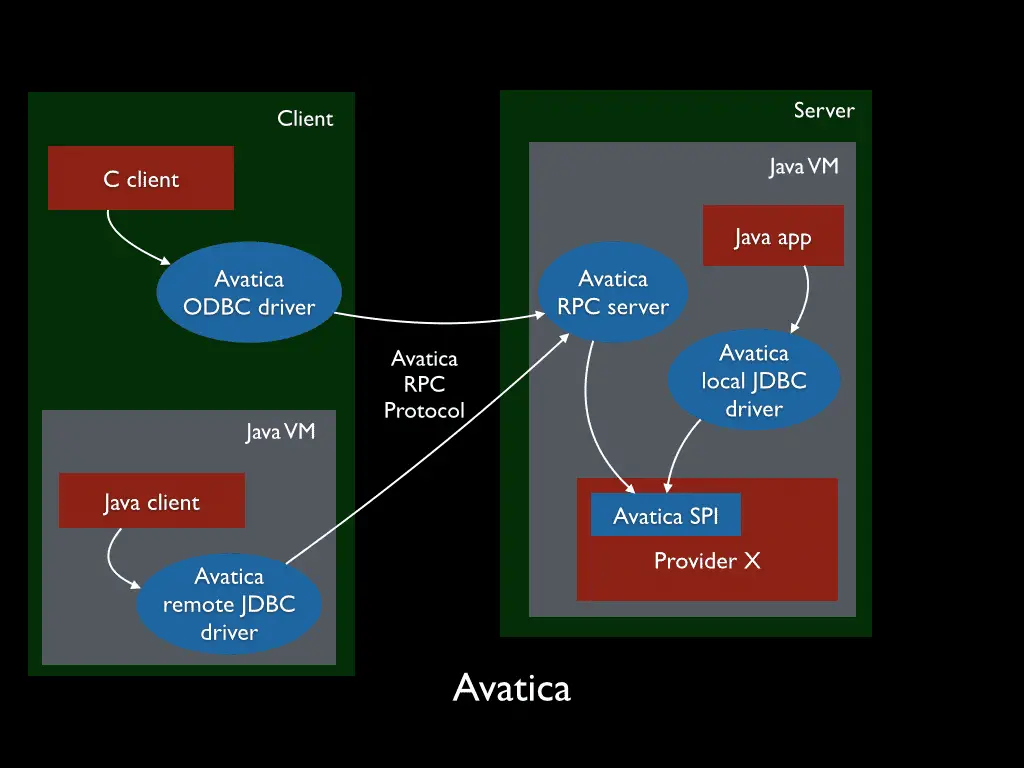
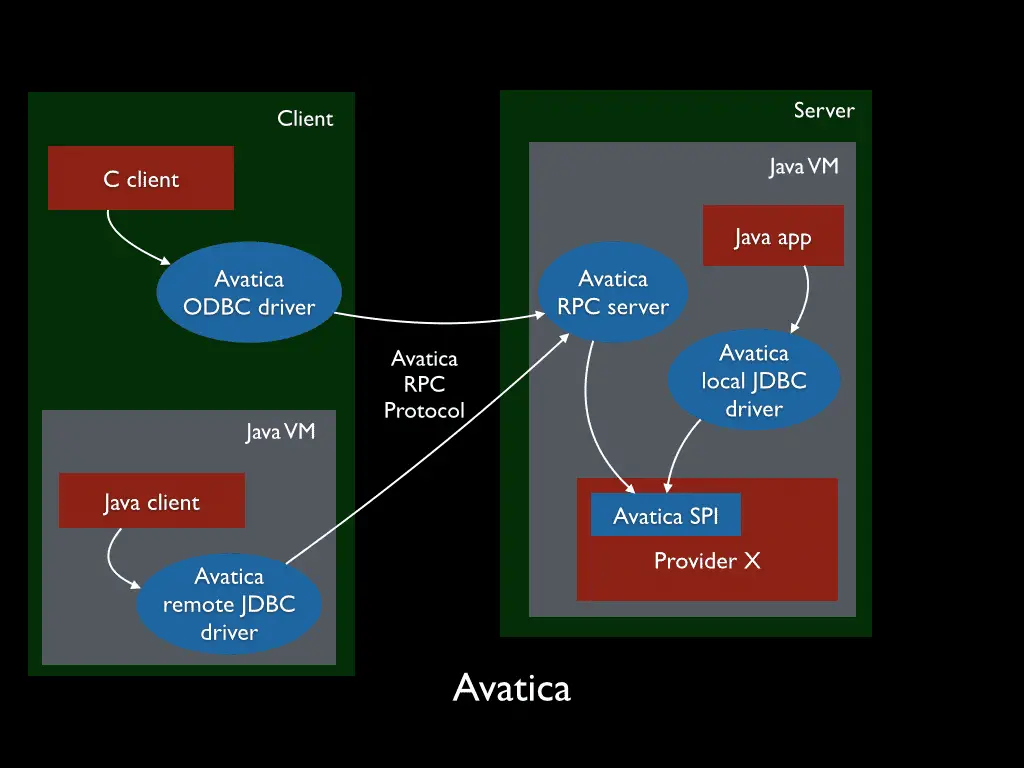
Avatica is a framework for building database drivers. Avatica defines a wire API and serialization mechanism for clients to communicate with a server as a proxy to a database. The reference Avatica client and server are implemented in Java and communicate over HTTP. Avatica is a sub-project of Apache Calcite.
“Apache Calcite Avatica JDBC driver creates HTTP client instances based on class names provided via `httpclient_impl` connection property; however, the driver does not verify if the class implements the expected interface before instantiating it, which can lead to code execution loaded via arbitrary classes and in rare cases remote code execution,” read the security bulletin.
To exploit the vulnerability:
1) the attacker needs to have privileges to control JDBC connection parameters;
2) and there should be a vulnerable class (constructor with URL parameter and ability to execute code) in the classpath.
Apache Calcite Avatica 1.22.0 will be verified that the class implements the expected interface before invoking its constructor. In this regard, we recommend that users upgrade Avatica in time to fix CVE-2022-36364.