CyLR v2.2 releases: Live Response Collection
CyLR
What is CyLR?
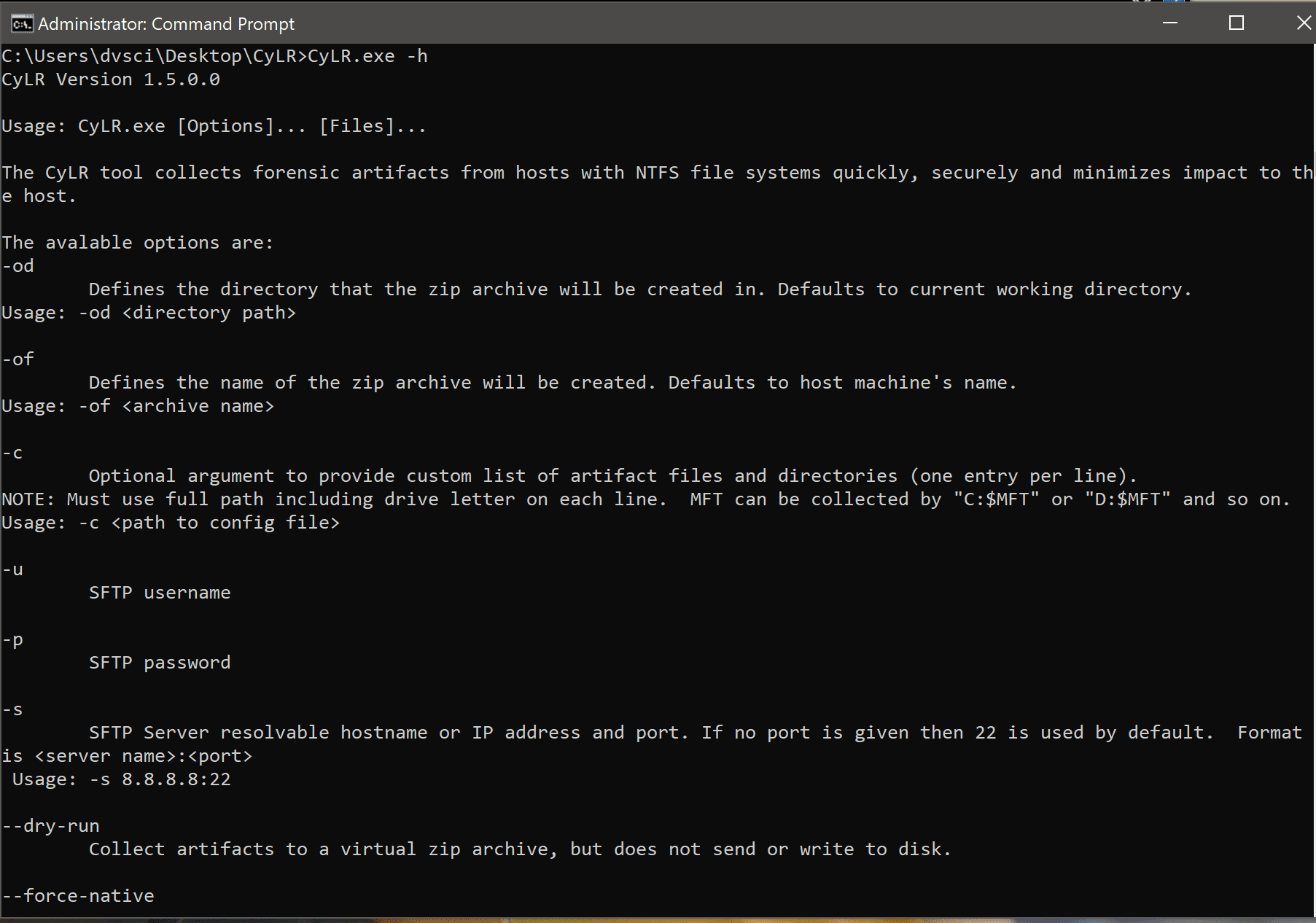
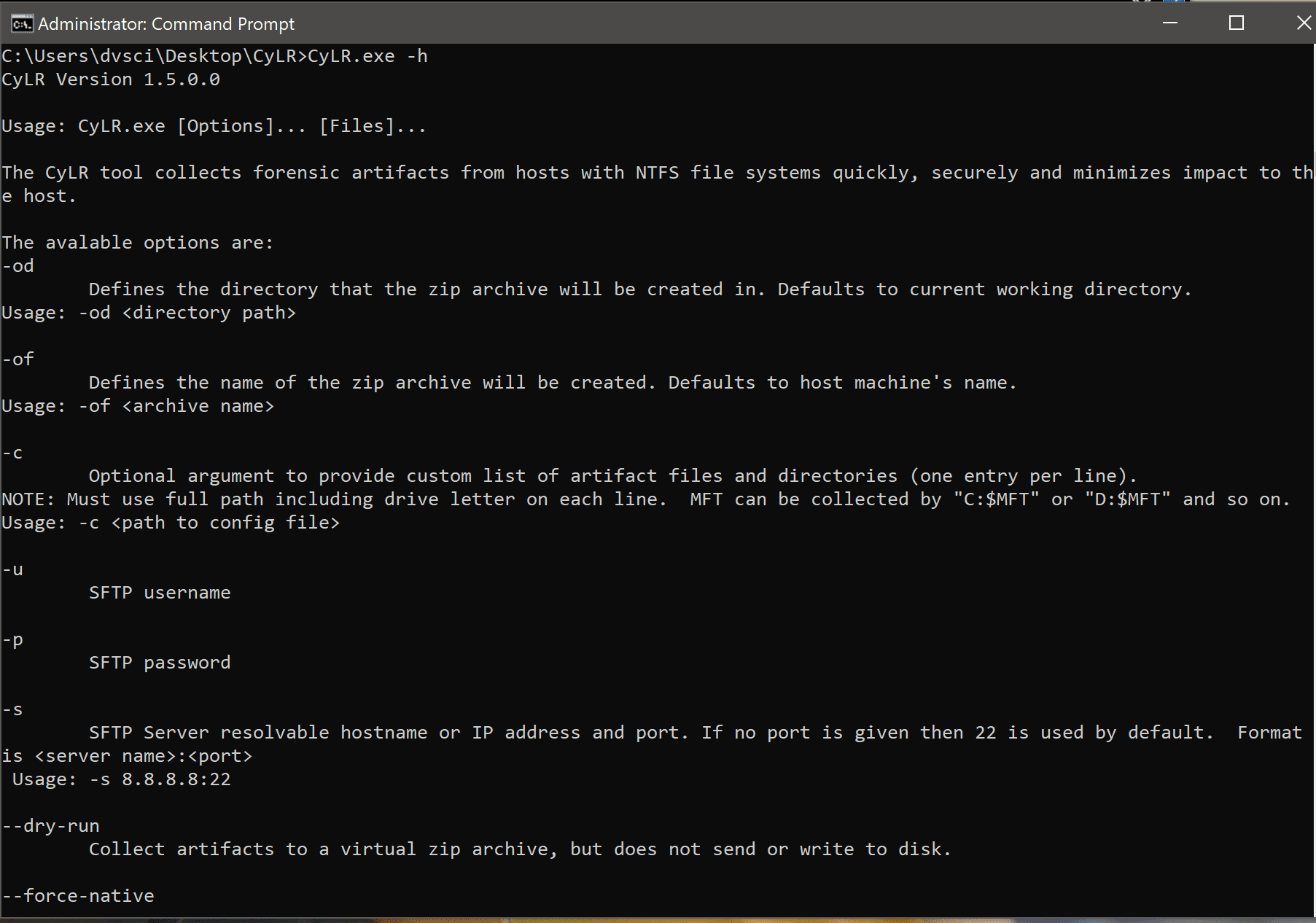
The CyLR tool collects forensic artefacts from hosts with NTFS file systems quickly, securely and minimizes impact to the host.
The main features are:
- Quick collection (it’s really fast)
- Raw file collection process does not use Windows API
- Optimized to store the collected artefacts in memory (minimizing or removing entirely the need to write additional artefacts on the host disk)
- Built-in SFTP capability
CyLR tool collects forensic artefacts from hosts with NTFS file systems quickly, securely and minimizes impact to the host.
The standard list of collected artifacts are:
Windows Default
- System Level Artifacts
- %SYSTEMROOT%\SchedLgU.Txt
- %SYSTEMROOT%\Tasks
- %SYSTEMROOT%\Prefetch
- %SYSTEMROOT%\inf\setupapi.dev.log
- %SYSTEMROOT%\Appcompat\Programs
- %SYSTEMROOT%\System32\drivers\etc\hosts
- %SYSTEMROOT%\System32\sru
- %SYSTEMROOT%\System32\winevt\logs
- %SYSTEMROOT%\System32\Tasks
- %SYSTEMROOT%\System32\LogFiles\W3SVC1
- %SYSTEMROOT%\System32\config\SAM
- %SYSTEMROOT%\System32\config\SYSTEM
- %SYSTEMROOT%\System32\config\SOFTWARE
- %SYSTEMROOT%\System32\config\SECURITY
- %SYSTEMROOT%\System32\config\SAM.LOG1
- %SYSTEMROOT%\System32\config\SYSTEM.LOG1
- %SYSTEMROOT%\System32\config\SOFTWARE.LOG1
- %SYSTEMROOT%\System32\config\SECURITY.LOG1
- %SYSTEMROOT%\System32\config\SAM.LOG2
- %SYSTEMROOT%\System32\config\SYSTEM.LOG2
- %SYSTEMROOT%\System32\config\SOFTWARE.LOG2
- %SYSTEMROOT%\System32\config\SECURITY.LOG2
- %PROGRAMDATA%\Microsoft\Search\Data\Applications\Windows
- %PROGRAMDATA%\Microsoft\Windows\Start Menu\Programs\Startup
- %SystemDrive%$Recycle.Bin
- %SystemDrive%$LogFile
- %SystemDrive%$MFT
- Artifacts For All Users
- {user.ProfilePath}\NTUSER.DAT
- {user.ProfilePath}\AppData\Local\Microsoft\Windows\UsrClass.dat
- {user.ProfilePath}\AppData\Roaming\Microsoft\Windows\Recent
- {user.ProfilePath}\NTUSER.DAT
- {user.ProfilePath}\NTUSER.DAT.LOG1
- {user.ProfilePath}\NTUSER.DAT.LOG2
- {user.ProfilePath}\AppData\Local\Microsoft\Windows\UsrClass.dat
- {user.ProfilePath}\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG1
- {user.ProfilePath}\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG2
- {user.ProfilePath}\AppData\Local\Microsoft\Windows\Explorer
- {user.ProfilePath}\AppData\Local\Google\Chrome\User Data\Default\History\
- {user.ProfilePath}\AppData\Local\Microsoft\Windows\WebCache\
- {user.ProfilePath}\AppData\Local\ConnectedDevicesPlatform
- {user.ProfilePath}\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\
- {user.ProfilePath}\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadline
- {user.ProfilePath}\AppData\Roaming\Mozilla\Firefox\Profiles\
Mac and Linux Default
- “/var/log”,
- “/private/var/log/”,
- “/.fseventsd”,
- “/etc/hosts.allow”,
- “/etc/hosts.deny”,
- “/etc/hosts”,
- “/System/Library/StartupItems”,
- “/System/Library/LaunchAgents”,
- “/System/Library/LaunchDaemons”,
- “/Library/LaunchAgents”,
- “/Library/LaunchDaemons”,
- “/Library/StartupItems”,
- “/etc/passwd”,
- “/etc/group”
- All plist files
- All .bash_history files
- All .sh_history files
- Chrome Preference files
- FireFox Preference Files
Changelog v2.2.0
This version includes numerous modifications and introduction of new features,
highlighted below:
Added
- Logging is available, to destinations including the console, a log file, and
embedded within the resulting archive. The log name is specified with-l
and verbosity is adjusted with-vto increase or-qto silence. - Added
CUSTOM_PATH_TEMPLATE.txtwith documentation on how to specify custom
paths for collection. - Implemented enumeration of files system contents in the same manner cross
platform - Through new FS enumeration, eliminated extra scanning/duplicate collection
of data within symbolic link directories. Eliminated dependency on the
findbinary. - Enabled the use of globbing patterns within paths. This includes patterns
such as:**/*.plist/home/*/.*sh_history\Windows\Temp\[a-z0-9][a-z0-9][a-z0-9][a-z0-9]\***/Library/*Support/Google/Chrome/Default/History*
- Enabled the use of regular expressions within paths. This includes full line
and substring patterns, such as:.*mawlare.*^C:\Windows\Temp\[A-Za-z0-9]{8}\.*$^C:\Windows\System32\Config\(SOFTWARE|SYSTEM|SAM|SECURITY).*$
- Added functionality to allow the user to select whether the existence of a
custom collection list (-c) should be in addition to versus in place of
the default artifact list. Continues to default to the replacement option
where it will only collect specified files. - Modified config file to support specification of path pattern type. Can be
one ofstatic,glob, orregex. Format should be a tab delimited text
file with one pattern type and path per line. A line starting with a pound
character will be ignored. - Provided status messages to summarize the number of files scanned and paths
staged for collection. - Increased documentation of source code.
Removed
- Removed collection of Windows Search path due to large size on some systems
(%PROGRAMDATA%\Microsoft\Search\Data\Applications\Windows).
Please use-cto re-include as needed.
Changed
- Edited build scripts to point to C:\Program Files\7z instead of x86 folder
- Improved the default collection paths for Linux platforms.
- Modified the USNJrnl collection argument to default to disabled collection.
- Improved SFTP handling to collect to a local zip file and attempt the
upload three times, with a 30 second delay between attempts. - Semantic changes to packaging and build scripts to avoid alias use.
- Added packaging script check to see if packaging tool was local before
re-downloading. - Updated argument usage information.
- Added tests to increase coverage of Arguments.cs
- Updated to use travis-ci.com
Download
Use
Copyright (C) 2017 Alan Orlikoski and Jason Yegge
Source: https://github.com/orlikoski/





