EfiGuard v1.4 releases: Disable PatchGuard and DSE at boot time
EfiGuard is a portable x64 UEFI bootkit that patches the Windows boot manager, boot loader, and kernel at boot time in order to disable PatchGuard and Driver Signature Enforcement (DSE).
Features
- Currently supports all EFI-compatible versions of Windows x64 ever released, from Vista SP1 to Server 2019.
- Easy to use: can be booted from a USB stick via a loader application that automatically finds and boots Windows. The driver can also be loaded and configured manually using either the UEFI shell or the loader.
- Makes extensive use of the Zydis disassembler library for fast runtime instruction decoding to support more robust analysis than what is possible with signature matching, which often requires changes with new OS updates.
- Works passively: the driver does not load or start the Windows boot manager. Instead it acts on a load of
bootmgfw.efiby the firmware boot manager via the boot selection menu or an EFI application such as the loader. If a non-Windows OS is booted, the driver will automatically unload itself. - Supports four-stage patching for when
bootmgfw.efistartsbootmgr.efirather thanwinload.efi. This is the case when a WIM file is loaded to boot WinPE, Windows Setup or Windows Recovery mode. - Graceful recovery: in case of patch failure, the driver will display error information and prompt to continue booting or to reboot by pressing ESC. This is true even up to the final kernel patch stage, because the last patch stage happens before
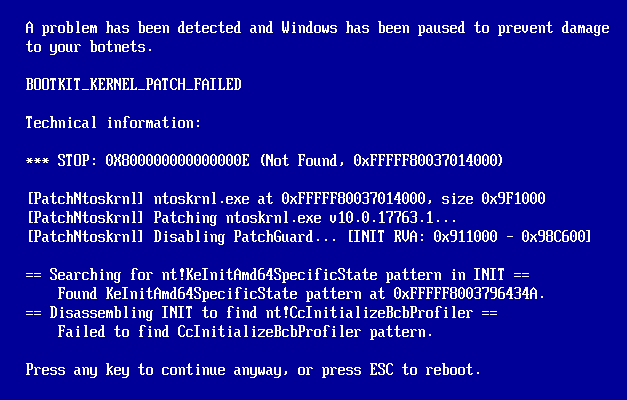
ExitBootServicesis called. Many UEFI Windows bootkits hookOslArchTransferToKernelwhich, while easy to find by pattern matching, is a function that executes in protected mode afterExitBootServices. This means no boot services are available to tell the user that something went wrong. Simulated patch failure with error information
Simulated patch failure with error information - Debuggable: can output messages to a kernel debugger and to the screen (albeit buffered) during the kernel patching stage, and to a serial port or unbuffered to the screen during the boot manager and boot loader patching stages. If the driver is compiled with PDB debug information, it is possible to load the debug symbols at any point after HAL initialization by specifying the virtual DXE driver base and debugging it as you would a regular NT driver.
- DSE bypasses: available as either a straightforward UPGDSED-style DSE disable at boot time or as a hook on the
SetVariable()EFI runtime service. The latter serves as an arbitrary kernel-mode read/write backdoor that can be called from Windows usingNtSetSystemEnvironmentValueExand allows settingg_CiEnabled/g_CiOptionsto the desired value. A small DSEFix-style application namedEfiDSEFix.exeis provided that can be used to do this. It is also possible to leave DSE enabled and to disable only PatchGuard. The loader will use theSetVariablehook method by default, due to the fact that some anti-cheat and anti-virus programs do not understand the difference between cheats or malware and self-signed drivers in general and target the UPGDSED fix. - Supports on-disk modified kernels and boot loaders by patching
ImgpValidateImageHashat every stage as well asImgpFilterValidationFailure, which may silently rat out some classes of violations to a TPM or the SI log file. - Allows Secure Boot to work with Windows 7 (not a joke!). Windows 7 itself is oblivious to Secure Boot as it does not support it, or (officially) even booting without CSM. This is useful for people who want to use Windows 7 on a locked down device that requires WHQL Secure Boot.
Changelog v1.4
EfiGuardDxe
- Compatibility fixes to support future versions of Windows. This affects Windows Insider builds 25941 and up. (#103)
EfiGuardDxenow correctly clears and restoresCR4.CETalong withCR0.WPif needed.
As a result of this, EfiGuard can now also disable write protection during copies from its runtimeSetVariablehook, which it previously did not do due to the potential for conflicts with CET.- Restored compatibility with EasyAntiCheat (EAC) (but see below). This fixes a regression introduced in v1.1.
- Note: This fix requires Windows 11 or Server 2022 in order to work for reasons related to PatchGuard internals.
Older versions will see no benefit. This is unlikely to ever change. - Note: Compatibility with anti-cheat software is not necessarily a goal of EfiGuard. This change fixes a regression that was affecting legitimate users. Issues complaining that EfiGuard isn’t letting you cheat in video games will still be closed WONTFIX.
- Note: This fix requires Windows 11 or Server 2022 in order to work for reasons related to PatchGuard internals.
Loader
- Interactive driver configuration through the loader has been changed from a compile time to a runtime switch. If you were using
Loader.config.efi, you can now access this functionality by pressing the<HOME>key when prompted. - Fixed chainloading issue when using a third party boot manager such as Ventoy to boot Windows. (#91)
EfiDSEFix
EfiDSEFixwill now acquireSE_DEBUG_PRIVILEGEbefore attempting to query kernel modules. (#97)
This is another compatibility fix for Windows Insider that will likely be required in future versions of Windows.- Fixed invisible/hidden console output when running from a non-elevated prompt with UAC enabled. (#75)
Download && Use
Copyright (C) 2019 Mattiwatti





